I am asked about Cisco Next Generation Security aka FireSIGHT licensing at least once a week. This post will explain the license options for Cisco FirePOWER and what is needed to request demo licenses to enable your demo system. NOTE: This is the current license model as of March 8th 2015.
For those that are not familiar with the new Cisco FirePOWER offering, it is a blend of Content Filtering, Reputation Security, Application Visibility and Controls, Vulnerability Scanning, IPS/IDS, Network and Endpoint Day Zero protection. These features are offered as a dedicated physical or virtual appliance, as a software option ran inside of a X generation ASA or as a Cloud service. For the dedicated appliance, virtual appliance and ASA version, there are three license options.
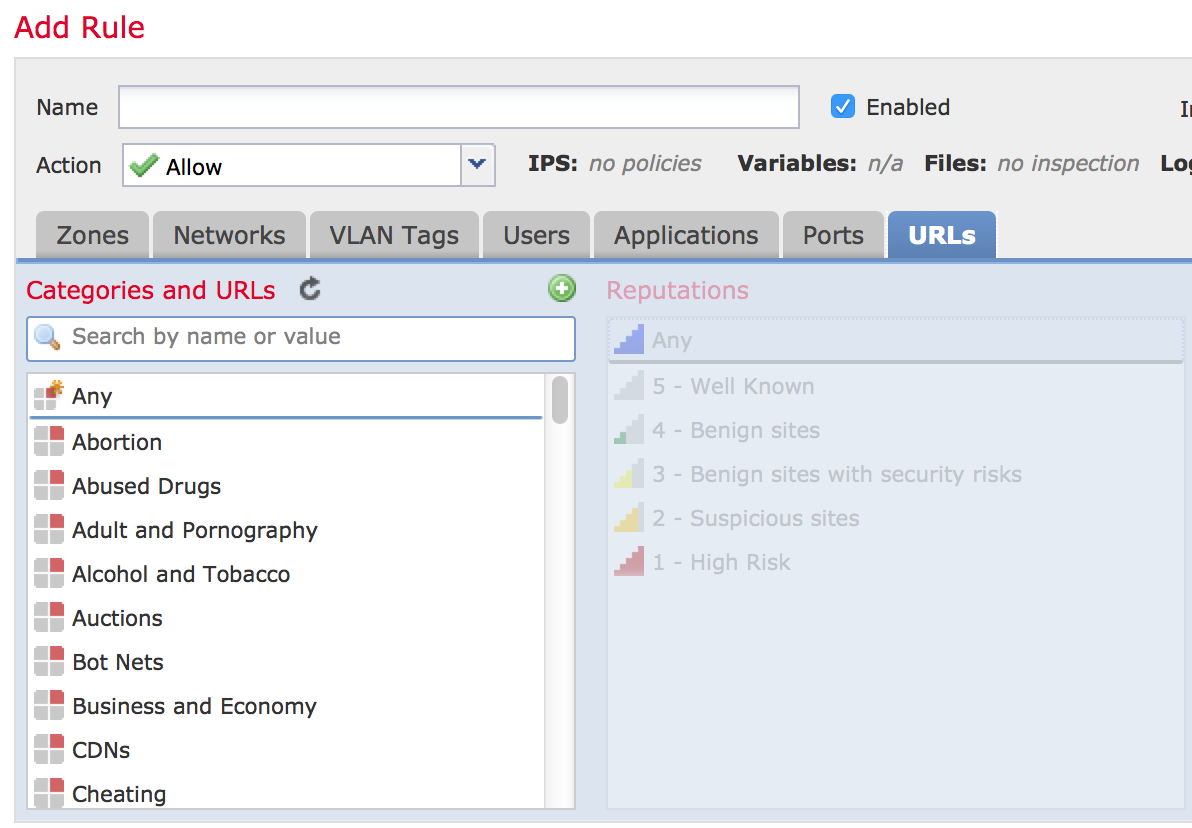
1) URL – This gives you a subscription feed updating website categories and reputation. This means you can block specific types of websites such as “adult” or “gambling” websites. Applications are included with the default system and do not require the URL license. For example, blocking Facebook games, Bittorrent or AOL Chat all can be done without the URL license.
The URL license also includes monitoring the reputation of a website meaning its “credit score” type rating. So if a website says they are a bank however have been online for one hour, hosted from godaddy.com and so on, it is probably not a bank and will have a low reputation score. Same goes for a real bank that is breached and starts passing malware to users. This isn’t fool proof since somebody could breach a trusted website and launch attacks from it however as those attacks are seen, the credit score will eventually go down. It is a great first line of defense to scrap off the common web attacks. You can learn more about reputation security HERE.
URL Tab shows the URL License. Other Tabs Are Default Options
2) Intrusion Detection / Prevention – This provides the ability to identify and prevent attacks. Whats unique about the FirePOWER offering is the IPS not only provides the general signatures, but it also leverages the built in vulnerability scanner and content visibility to self tune or adapt to your environment. This means if you have assets that are not protected, FireSIGHT will recognize and either auto protect or recommend to enable protection before the vulnerability is exploited. The same goes for recommending to turn off signatures for assets that don’t exist on the network.
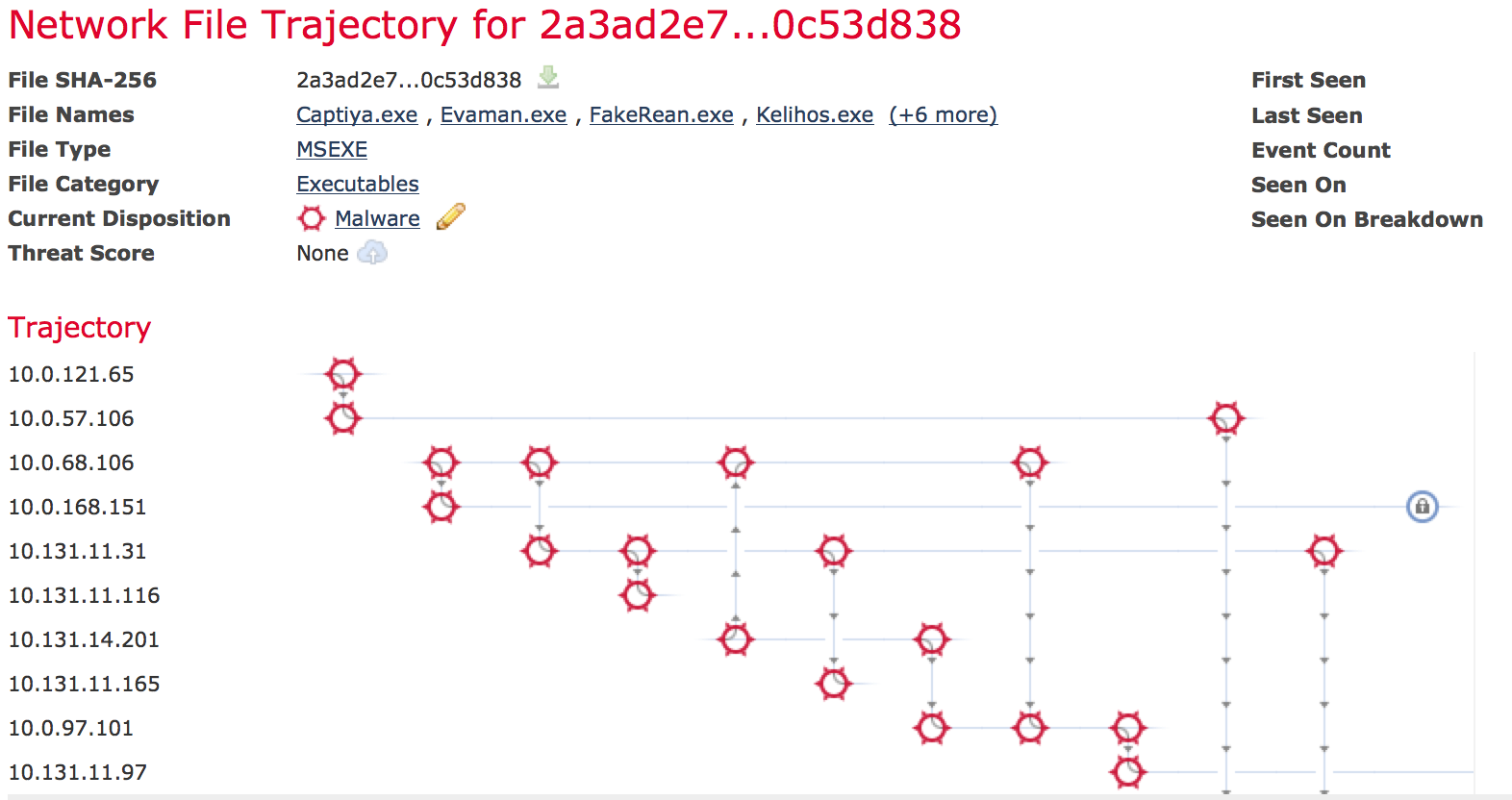
3) Advanced Malware Protection (AMP) – When AMP is enable, every file on the network is given a SHA256 hash. That hash can be sent to Cisco’s Talo’s team (once ThreatGRID) to see if anybody has seen it as being malicious. If the file is interesting, the actual file could be sent to the cloud to be fully analyzed for malicious intent. Files are also monitored on network for behavior such as polymorphism, Fuzzing, what ports are used and so on basically looking for indications of a system being compromised. (NOTE: This can be files crossing the appliance and internal files seen going between hosts). If the cloud lookup, cloud file dissection or network monitoring identify the file as being malicious, a page is created showcasing what the infection is, who first brought it on the network, everybody who has seen and infected by the file, other possible versions seen in the wild and so on. This does not require any agents meaning it is just a license to enable all of this.
Shows .exe malware SHA introduced and passed to other systems
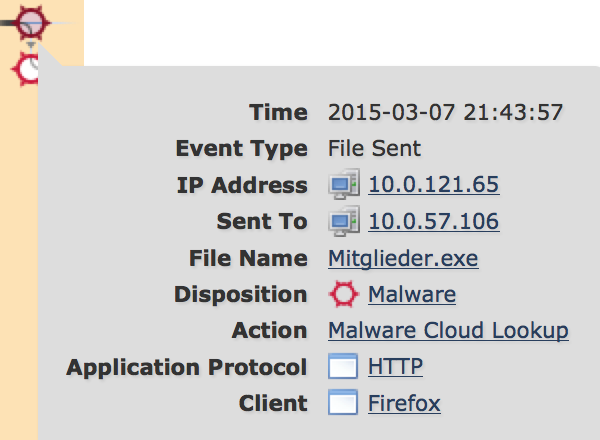
The Mitglieder.exe malware was introduced through Firefox by this person
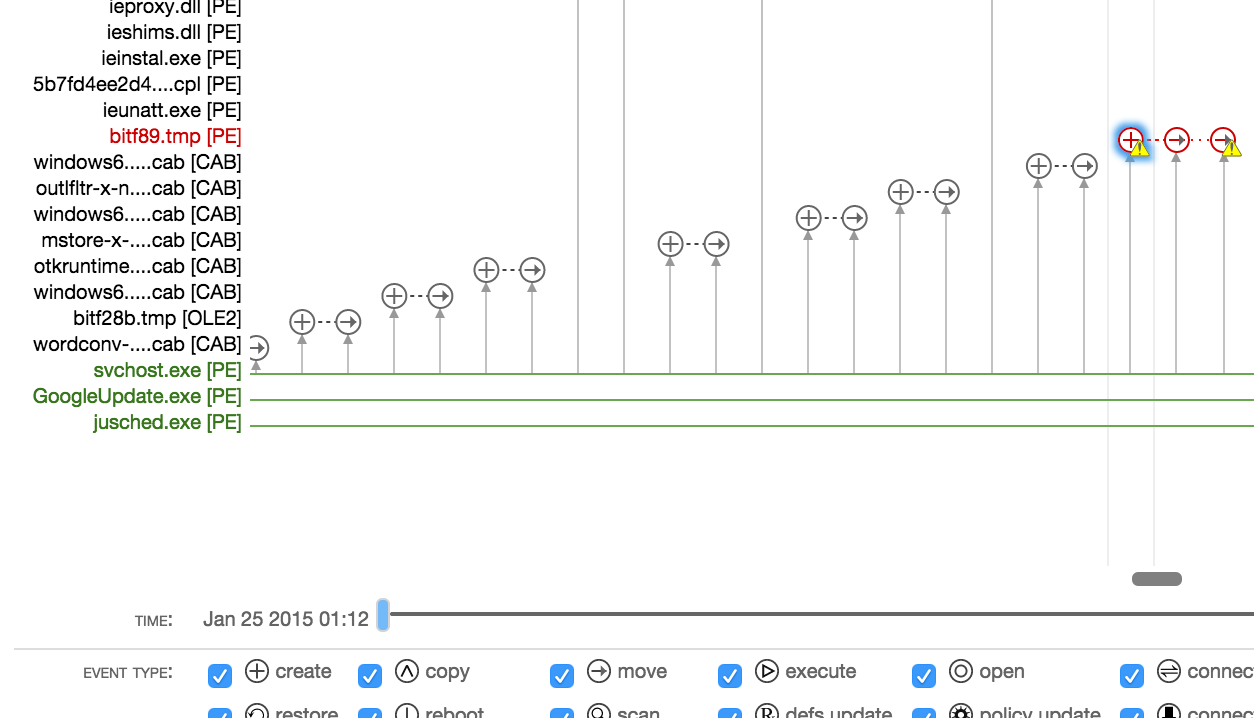
NOTE: There is a optional agent you can install on endpoints to provide deeper visibility. The agent can tell you where the infection is installed, what it modified, provide more visibility about the endpoints behavior and auto remove the file. It is not required as just with network AMP you will know anybody infected, how it happened and what to look for however you won’t be able to know where it is at on each host or have the ability to auto remove it. I personally use AMP as a cloud service meaning just the agents on my family’s computer as a means to catch malware that bypasses my family’s anti-virus. The AMP agent has an additional cost sold as bundles and available for windows, MAC and mobile devices.
Shows Infection Stopped By AMP
Application Visibility and Control comes with the default system. You also need a controller license if you are using the ASA version of FirePOWER that is bundled in at no cost. If you want centralized management for the ASA models, there are three license options for the virtualized version of FireSIGHT (most common request for demos). They are a limit to 2 ASAs license, limit to 10 ASA license and unlimited which maxes out at 25 ASAs. The hardware managers can go beyond 25 ASAs if that is required.
If you want to test out the FirePOWER solution on your ASA or as a dedicated appliance, you will need to request one or more of the licenses listed above, a licenses for the management system (if you are using FireSIGHT for centralized management) and the controller if you are using a ASA to host FirePOWER. Your Cisco rep will ask you for two things required to provide you a demo license. Those are
1) The model of hardware you want to enable FirePOWER on
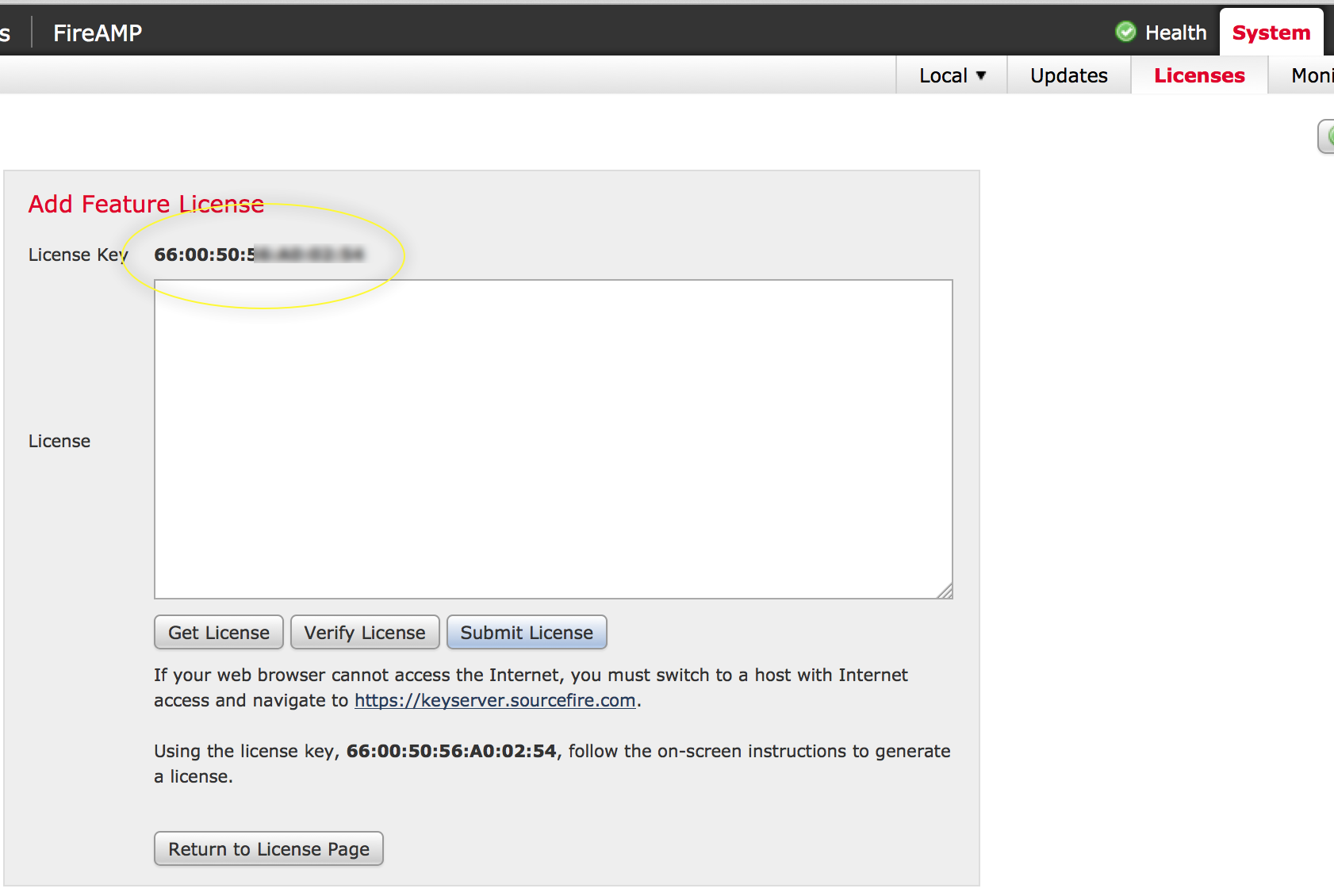
2) The Management License Key – This is found in FireSIGHT for versions 5.1 and later. Go to System -> Licenses and click “Add new License”. The Add Feature License page will appear and show you the license key. Here is an example of what you will see.
Hopefully this post helps answer Cisco FirePOWER questions about licensing.





I am in the process of setting up an ASA 5525-X with FireSIGHT virtual defense center. I received my URL and AMP license PAK via email, and control and protection PAK came with the router in an envelope. I added my ASA 5525-X to the defense center and applied all of these licenses to it. However, when I view the Application Statistics dashboard all of the widgets say “No FireSIGHT license available.” and have a link for me to install another license. I saw some mentions online of there being a “FireSIGHT license” (different form the four that I mentioned above) but have no idea where to find the PAK for it. Is this something I would have had to purchase separately, or am I just missing something here?
Your help would be appreciated. I’d also like to thank you for your blog posts, they really helped in getting me set up.
You may be missing the ASA controller license. It is free but has to be added to the manager. Confirm that you have that installed in FireSIGHT
I’m certain that I didn’t install that license. Where would I find it?
It should be something like ASA(model number)-CTRL-LIC so ASA5515-CTRL-LIC for example. I suggest you reach out to the person that provided the solution to you. Confirm you have the ASA controller license that should have been included. It is added like the other licenses.
Thanks very much. I’ve confirmed that this license was in my original Cisco quote but was not on the BOM that I ordered from my supplier. I’m getting it straightened out now.
Perfect. I’m glad I could help.
How long does the demo license last for? 60 days?
It depends on how long the Cisco support person cuts it for. The average is 60 days.
Any doco detailing what lic’s are available for eval? I went through the process and it came back with URL filtering only.
Speak with your trusted partner or Cisco rep. Any Cisco SE or CSE can cut you a eval key of the three licenses using internal tools.
Hi,
I have a 5545-X with FP and have installed a Defence Centre as VM machine. According to Cisco the Protection and Control licenses come bundled with at the time of ordering (i.e. free). I have a few questions;
What is the difference between Defence Centre and FireSight?
When trying to do a network discovery, it alerted by saying FireSight license is required. I am under the impression this is pre-bundled with the ASA/Defence Centre?
I would be grateful if you could clarify for me.
Thanks.
Mo
Hi Mo,
FireSIGHT and Defense Center are the same products. It is just a name change when Cisco acquired Sourcefire. Defense Center represents the pre Cisco naming.
Regarding licensing, the pre Cisco licensing is a little different from the post Cisco licensing. Post Cisco licensing has three parts as explained in this post (URL, IPS and AMP). The Application Visibility and Controls stuff is free. If you include a ASA, there is a controller license that is zero cost IE bundled at the time of ordering.
The FireSIGHT / Defense center system for virtual has three license options. There is a 2, 10 and unlimited (maxed at 20) license that permits you to manage those number of devices. For example, if you have only two ASAs running firepower running as a HA cluster, the 2 license would work for your FireSIGHT.
Your problem could be either that you don’t have the management license or the connector license. Feel free to email me at jomuniz AT cisco.com with your management key. I can generate you a temp key to see if that will fix the issue. If it does, we can figure out how to get you a more permanent solution.
Hi
I have a control license and I activated firepower through ASDM with that, now I want to use FireSight and when I create access control policy and want to assign to a device , it said that you need control license.
now I used CTRL-L before and can’t generate .lic again becuase license keys (shows in FirePower and FireSight are different) , what should I do ?
Your help would be appreciated.
Hi Tim. To be clear, you were using FirePOWER features managed by ASDM however now you are using FireSIGHT and you lost the CTRL license when choosing to manage with FireSIGHT verses ASDM? Note that newer FireSIGHT uses smart licensing that removes this and other problems while old licensing is where this problem comes into play. My suggestion at this point is to open a TAC case and have them correct the license issue. If you can go smart license, do that so you don’t have to enter licenses anymore. You just log into your account and everything is pushed down to the ASA. If you want to stay with the old license, note you won’t be able to use the unified image (6.1 coming out any day now) and you may need TAC to generate another CTRL license if you can’t find the one you where using. Hope this helps
Hi
I have license control for asa5545-x , and I activated FirePower with this license through ASDM, now I want to use FireSight Management, but the problem is because I used CTR-L on FirePower, when I want to create access control policy on FireSight Management and assign it to a device, it said that I should add license. So I can’t use the CTR-L that I used before for activate FireSight Management (License Key is different).
Now my question is what should I do ? can I use that license for FireSight Managemnt ?
Best Regards.
Hi Tim. To be clear, you were using FirePOWER features managed by ASDM however now you are using FireSIGHT and you lost the CTRL license when choosing to manage with FireSIGHT verses ASDM? Note that newer FireSIGHT uses smart licensing that removes this and other problems while old licensing is where this problem comes into play. My suggestion at this point is to open a TAC case and have them correct the license issue. If you can go smart license, do that so you don’t have to enter licenses anymore. You just log into your account and everything is pushed down to the ASA. If you want to stay with the old license, note you won’t be able to use the unified image (6.1 coming out any day now) and you may need TAC to generate another CTRL license if you can’t find the one you where using. Hope this helps
Hello.
I requested for ASA 5555x with firePOWER from a vendor. They purchased an ASA 5555x without requesting for the firePOWER services because the vendors themself don’t know much about it firePOWER.
Now I have my ASA without the firePOWER. After few months I realised that the firePOWER services are not available and I went back to the vendor reporting the issue to them.
Now am told to find out what I needed and let them get me that.
My questions are:
1. What is the best way to request for the firePOWER services alone with the default licenses?
2. And can you please state the cost of the firePOWER service alone with the default license.
3. Please list the default license that should be included.
4. Please list other licenses that are not part of the default with their cost.
Thanks.
Hi Simple,
First thing to note is this blog post came out in early 2015. Second, with regards, the licensing, there are two options now, which are SMART and REGULAR licensing. SMART licensing takes care of things like this meaning you call Cisco TAC or the partner you purchased the gear from and they get things modified via your SMART account. Cisco cloud directly updates your ASA providing the features you need. The newer threat defense or unified images require smart licensing. For the separate ASA and Firepower image, you can still use the older license model and I can see how a miss configuration during the order could occur.
Here are some answers to your questions. The sum of it will be I’m just a guy with a blog so you probably want to open a TAC case or reach out to the solution provider who sold you the technology and have them fix this.
1. What is the best way to request for the firePOWER services alone with the default licenses? —- Not sure what you mean by requesitng firePOWER services alone with default license. You can use smart or regular licenses. There are three license option, which are URL, IPS and AMP. Cisco offers one part that is a bundle of all three licenses. You probably want to purchase that to get the most discount and fully license your ASA with firePOWER services.
2. And can you please state the cost of the firePOWER service alone with the default license. —- Cost depends on who you buy from, who you are, etc. Everything has a street cost however that typically is not the final cost. Speak with your trusted solution provider regarding quotes.
3. Please list the default license that should be included. — If you are looking for a fully licensed firepower solution, the TAMC is what represents this.
4. Please list other licenses that are not part of the default with their cost. Again pricing depends on who is selling you the technology. I recommend stepping back and asking for your solution provider to look at what you are trying to protect and align your goals with the technology options Cisco has to offer. There are on prem, cloud and hybrid security solutions that offer similar capabilities but designed for different environments. The most vanilla security platform we offer would be a ASA appliance with the TAMC license fully enabling all firePOWER capabilities (URL, IPS and AMP).
Hope this helps
Hi there,
Congrats for your blog. You explain things with the clarity sometimes missing from cisco docs. I hope you can help me with this.
I generated a TAMC classic licence with the DeviceID from the ASDM on a ASAwithFPWR… only to later realise, i should have done it with the DeviceID of the FPManager. I managed to rehost the control licences but i’m not seeing the option to rehost the TAMC licence. Am i missing something? Is it not possible to rehost TAMC licences?
Thank you for your help.
Hi,
Are you a Cisco partner? Only Cisco employees or partners can issue TAMC temporary licenses. As a reminder, these kind of issues will go away as Cisco moves to smart licensing.
You should be able to reissue a license with the old tool or have TAC do it for you. I found that sometimes there is a internal data base issue when I use the same manager and continue to re-image and license firepower appliances using the older system (non smart licenses). I recommended to my engineers to rebuild the firepower manager for new installs or using the same firepower appliances with different licenses to avoid a situation where the older license / MAC address is stuck in the database. Worst case, if you are using the firepower manager VM, just rebuild it and try adding it with the right TAMC (may be faster than spending hours troubleshooting). In your case though, usually these errors are more about adding the firepower appliance to the manager verses getting the TAMC to work, hence why I think you should be able to just re-license it and it should work without a firepower manager rebuild.
Hope this helps. Let me know if it works
Do you know of anyway to move the licenses from one Firepower to the next if you don’t have the original PAKS?