IPads and iPhones are pretty awesome. They are slick looking and fun to play with. My friend’s Android is pretty cool as well. I had to find an app that gave my iPhone a slider login to counter his coolness. Regardless of the cool factor, many agencies are afraid these devices bring lots of risk if permitted on the cooperate network.
As C-level executives / high-ranking commanders get their hands on fancy mobile devices, they start to demand for a policy to bring mobile devices onto the network.
My recommendation to secure mobile devices is to look at this from two sides:
1) NETWORK: How do I provision network access for approved and non-approved mobile devices?
2) END POINT: How do I manage approved mobile devices such as enforcing polices around what applications are used, avoiding jail broken devices, etc.
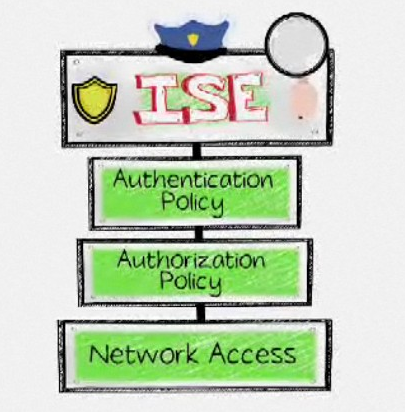
To answer question 1, the best way to look at this is as an access control problem. Many customers I have worked with provision non-approved devices on a limited network through the use of VLAN redirection, ACLs or separate wireless SSID. For cooperate issued devices, they leverage authentication to see if the user is approved and scan for policy checks to verify the device is safe before provisioning access. Failure to meet these checks either defaults the device to the guest network, limits the cooperate access or completely denies the device. Some examples of access control solutions are Cisco ISE, Cisco NAC appliance and Forscout.
To answer question 2, this comes down to end point management. Vendors like Symantec offer mobile device management solutions, which offer an agent to enforce policy. They have features like password enforcement, remote wiping only corporate data (key for not upsetting users violating policy), checking for jailbreaks, and offering additional authentication methods.
The final point I’ll bring up is its best practice to enforce the end point management piece through the access control solution. For example, develop a policy that looks for an iPad and checks for who is authenticated as well as if the end point management agent is installed, up to date and running. As long as the end point management agent is doing its job, you know the iPad is used by a approved user and is not brining on additional risk since it meets all cooperate policies enforced by the end point management agent. There are many ways to design this type of solution but hopefully this helps understand how to approach this situation from a high level viewpoint.