The majority of today’s workforce uses multiple devices such as laptops, tablets and smartphones (IE brings their own device or BYOD). Leadership from most industries is being asked to permit these devices on the network in some limited or full fashion. Common BYOD questions are “how do I support growth for users with multiple devices?”, “what type of access should guest and employees use for mobile devices?”, “how do I provision corporate mobile devices?”, and “what security vulnerabilities am I exposed to by permitting mobile devices?”. All are good questions and can be addressed by focusing on three core BYOD concepts: Infrastructure, Access Control and Device Management.
The majority of today’s workforce uses multiple devices such as laptops, tablets and smartphones (IE brings their own device or BYOD). Leadership from most industries is being asked to permit these devices on the network in some limited or full fashion. Common BYOD questions are “how do I support growth for users with multiple devices?”, “what type of access should guest and employees use for mobile devices?”, “how do I provision corporate mobile devices?”, and “what security vulnerabilities am I exposed to by permitting mobile devices?”. All are good questions and can be addressed by focusing on three core BYOD concepts: Infrastructure, Access Control and Device Management.
The first thing to consider for BYOD is if your wireless network can support growing from one device per user to potentially 2-4 devices. The best way to find out is by performing a wireless assessment to verify capabilities and potential risks caused by obstacles and nearby rouge networks (IE Starbucks using a similar RFID channel). Security features such as wireless intrusion detection and prevention (WIDS /WIPS) as well as controlling the number of permitted associated devices per user should be considered for BYOD to guarantee scalability and service.
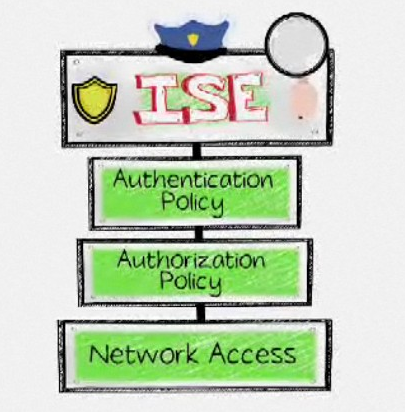
Another common area of concern for BYOD is provisioning access to employees and guests. The first BYOD question typically asked is “should all mobile devices be handled by a separate network or should employee owned mobile devices share the same core network while guest devices use another network?”. However you plan to permit mobile devices, best practice for BYOD is to automate the process based on multiple factors such as device type, user authentication and risk status. Policies permitting employee access using personal devices should have a process to register and track those devices (IE web registration page like in hotels) rather than an “employee wireless password” that could get compromised and not associated to a device. Many solutions such as Cisco Identity Services Engine (ISE) offer self-registration to eliminate the need for employee or guest users to deal with an IT member to gain network access. Solutions that leverage profiling technologies can automatically assigned specific access types based operating system, device type and other details (IE provide different access for iPhones and Androids) so you know who and what is on your network. “Knowing is half the battle”, GI JOE
The final piece to the BYOD puzzle is device management. Most mobile hardware vendors give power to device owners meaning Apple, Android, etc. device users can take themselves out of compliance at anytime (blackberry is the only exception). Solutions such as Mobile Iron and AirWatch provide methods to assess devices for high risk factors such as jailbreaking or using unapproved applications which is crucial for BYOD. Application based endpoint management solutions verify devices and either permit or deny corporate services such as providing email based on policy status (IE no email service while angry birds is installed). Common BYOD policies are enforcing the use of passwords, remote locking devices, denying hacked devices, provisioning specific applications and having the ability to remote wipe only corporate data. The mobile security market leaders offer a breath of operating systems and hardware options as well as easy methods to communicate when end users fall out of compliance.
 Industry leaders for security are focusing on BYOD by developing solutions for mobile devices. RSA and Symantec recently released data loss prevention (DLP) for mobile devices to deny sensitive information such as social security numbers from moving to or from mobile devices. Network vendors such as Cisco are partnering with mobile manufactures to address BYOD by offering VPN technology that encrypt traffic from mobile devices while off the corporate network. There are many options for endpoint security when looking at BYOD, which the investment for mobile security should match protecting laptops and desktops regardless if the employee owns the asset.
Industry leaders for security are focusing on BYOD by developing solutions for mobile devices. RSA and Symantec recently released data loss prevention (DLP) for mobile devices to deny sensitive information such as social security numbers from moving to or from mobile devices. Network vendors such as Cisco are partnering with mobile manufactures to address BYOD by offering VPN technology that encrypt traffic from mobile devices while off the corporate network. There are many options for endpoint security when looking at BYOD, which the investment for mobile security should match protecting laptops and desktops regardless if the employee owns the asset.