Cisco has posted the next release of their flagship security solution Identity Services Engine ISE 1.1.1 or ISE 1.1MR. ISE 1.1.1 is coined a maintenance release however includes some important new features such as some themed around Bring Your Own Device (BYOD).
You can find the ISE 1.1.1 release HERE and latest ISE 1.1.1 documents HERE or go to
www.cisco.com/go/ise for more information and
http://www.cisco.com/en/US/products/ps11640/prod_installation_guides_list.html for ISE 1.1.1 documentation
Here is a breakdown of what is new with ISE 1.1.1
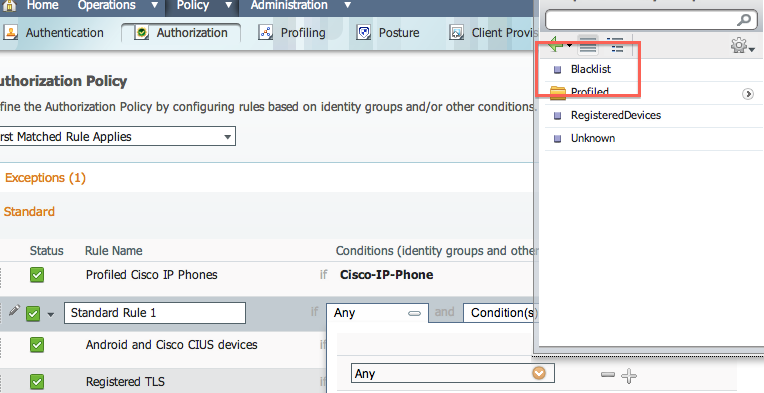
- New Default Authorization Profile (“Blacklist”) – ISE 1.1.1 can now “blacklist” user devices that get “lost,” or otherwise become unusable or taken out of circulation, until the device can be reinstated or has been completely removed from the network. Cisco ISE 1.1.1 removes “blacklisted” devices from the network and thay are not allowed back on until the device is reinstated

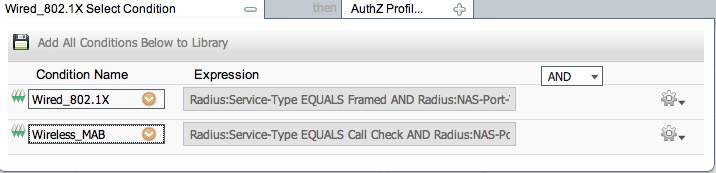
- Dictionary Attribute-to-Attribute Authorization Policy Configuration – You now have the option, when constructing policy conditions in an Authorization Policy, to specify another Dictionary Attribute to which you can associate the source Attribute during policy configuration

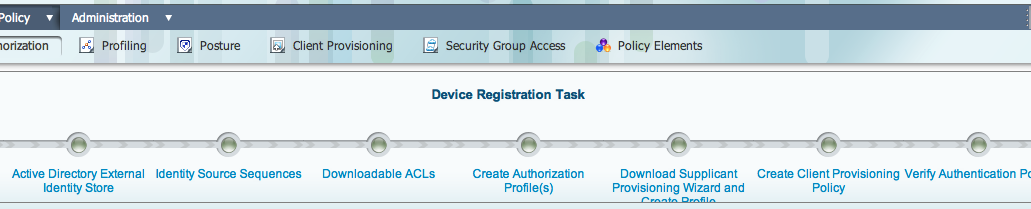
- New Device Registration Task Manager – New visual path through the various Cisco ISE 1.1.1 administration and configuration processes necessary to enable administrators to set Cisco ISE 1.1.1 up to provide multiple, configurable device support for end users

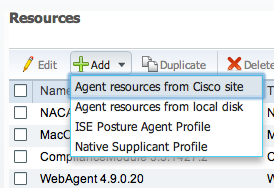
- Native Supplicant Provisioning Profile Configuration – Configure native supplicant profiles for client provisioning in addition to the existing “ISE Posture Agent Profiles” currently available in Cisco ISE Releases 1.0.4 and 1.1. This profile type allows you to specify settings for user registration via personal devices like iPhones/iPads and Android

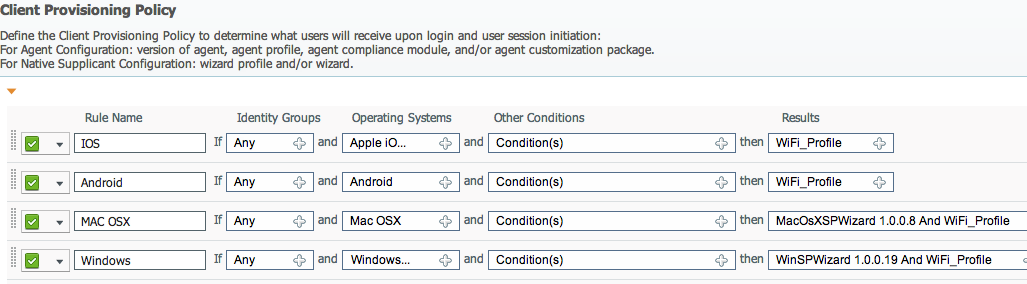
- Enhanced Client Provisioning Policy Configuration – You can now create or edit client provisioning policies to allow for expanded personal device support, including iPhones/iPads and Android. For the personal device support, specifically, you can configure the policy to upload the appropriate configuration wizard necessary to enable the user’s device to negotiate and register with Cisco ISE 1.1.1 (NOTE: In my example below, I’m using the IOS and Android native while I downloaded from Cisco wizards for MAC OX and Windows.)

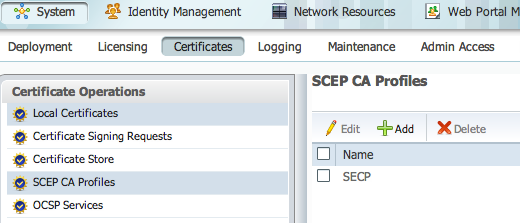
- SCEP Authority Profile Configuration Page – Enables you to configure one or more Simple Certificate Enrollment Protocol (SCEP) authority profiles. Cisco ISE 1.1.1 verifies maintains connectivity with the SCEP authority server(s) you specify, and even performs load-balancing among multiple servers to ensure optimal connectivity for users when they use their personal devices to access the network

- RADIUS Proxy Attribute – Enhance the RADIUS sequence flows and processing. When Access-Accept is received from an external RADIUS server, Cisco ISE 1.1.1 continues to the configured authorization policy for further decisions making based on additional attributes and groups queried from AD and LDAP.
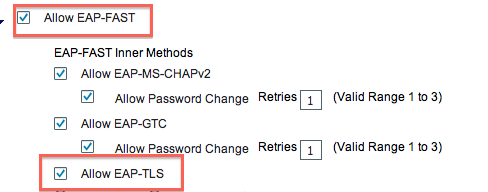
- EAP Chaining – Allows authenticating both machine and user in the same EAP-FAST authentication in a configurable order. When EAP-FAST authentication result is determined, Cisco ISE 1.1.1 allows you to apply authorization policy depending on the result of both authentications. When EAP chaining is turned off, Cisco ISE 1.1.1 performs usual EAP-FAST authentication.

- EAP-TLS as an Inner Method for EAP-FAST- Allows usage of EAP-TLS protocol as an inner method for EAP-FAST protocol. The implementation is equal to usage of EAP-TLS as inner method of PEAP

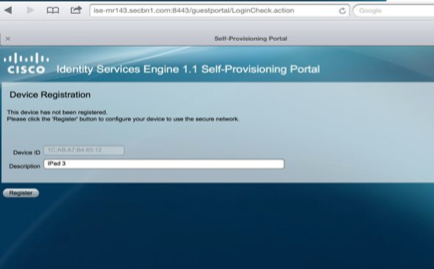
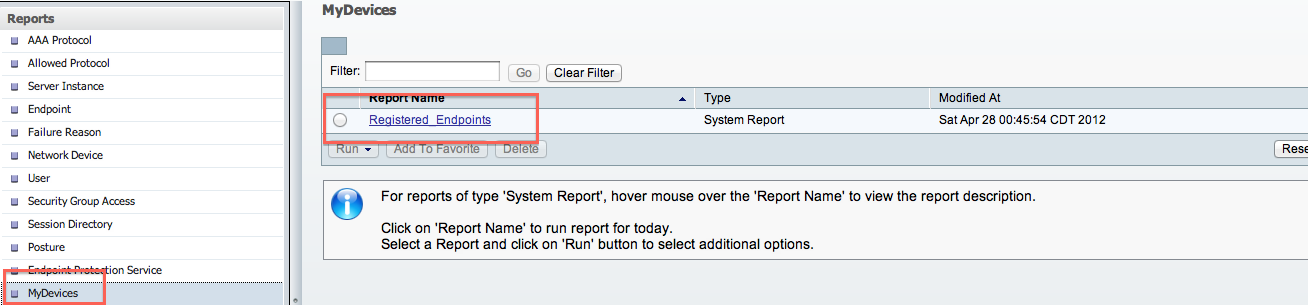
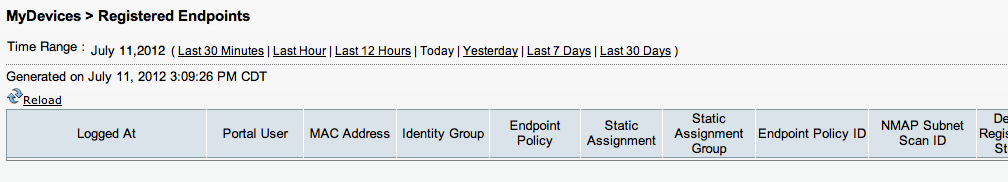
- Device Registration Portal – A standalone portal that can be completely customized to suite your organization. A network access user who is configured as an employee in an organization can access the portal that allows them to bring in their personal devices into an enterprise network through an employee authentication, and then a device registration process. An employee can manage their devices to add, edit, reinstate, and delete their devices through this portal. Cisco ISE 1.1.1 adds these devices to the endpoints database, and profile them like any other endpoint. The Cisco ISE 1.1.1 administrators can manage the registered endpoints from the administrator user interface, by using the identities list and reports

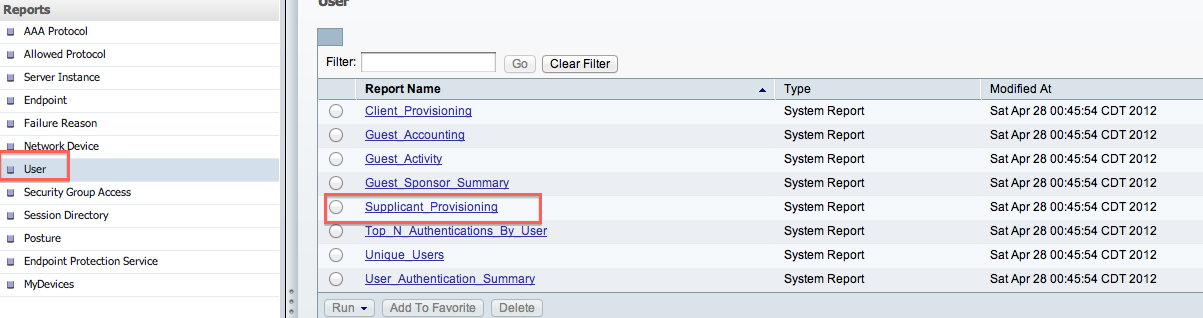
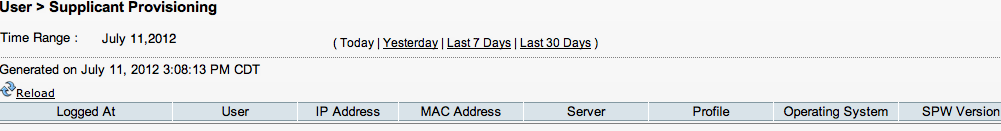
- New Reports in Cisco ISE 1.1.1
- Change of Authorization – Triggers a CoA when an endpoint is added or removed from an endpoint identity group that is used by authorization policy. Any change in an endpoint identity group assignment for an endpoint that occurs due to dynamically profiling or a static assignment to an endpoint identity group, a CoA is triggered in both the cases
Go download the latest ISE 1.1.1 release. The upgrade process will take you around 30 minutes to complete. Here what it will look like.
ISE-10MR2/admin# application upgrade ise-appbundle-1.1.1.268.i386.tar.gz ftp
Save the current ADE-OS running configuration? (yes/no) [yes] ?
Generating configuration…
Saved the ADE-OS running configuration to startup successfully
Initiating Application Upgrade…
Stopping ISE application before upgrade…
Running ISE Database upgrade…
Upgrading ISE Database schema…
Upgrading Session Directory… Completed.
ISE Database schema upgrade completed.
Running ISE Global data upgrade as this node is a STANDALONE…
Running ISE data upgrade for node specific data…
% NOTICE: Upgrading ADEOS. Appliance will be rebooted after upgrade completes successfully.
The mode is licensed.
% This application Install or Upgrade requires reboot, rebooting now…
Broadcast message from root (pts/0) (Wed Jul 11 15:27:38 2012):
The system is going down for reboot NOW!



Hi Ed.
One of our engineers had a similar issue with the upgrade using SSH. You need to set a keep alive (securecrt will do it) for about every 10 minutes. Or just set a stopwatch and just hit enter. It does take a LONG time. Avoid CTRL-C.
Hi Kyle,
Check out the latest config guide on http://www.cisco.com/go/ise and look for Multi-Portal Configurations. It states
A predefined DefaultGuestPortal is available under Multi-Portal Configurations. This portal has the default Cisco look-and-feel that you can choose to customize it through the Cisco ISE Admin user interface, or you can upload HTML pages to create a customized portal. To create a personalized portal with custom HTML pages, you must first add a new portal.
Guest Portal URL
The following procedure utilizes the Guest portal URL. For reference, the Guest portal URL for the wired and wireless local web authentication is as follows:
https://ip:8443/guestportal/portals/PortalName/portal.jsp
Where the PortalName is the name of the portal as it is created during the upload.
The Guest portal redirect URL for CWA is:
https://ip:port/guestportal/gateway?sessionId=SessionIdValue&portal=PortalName&action=cwa
The `ip’ and `port’ values are updated by the RADIUS server as the URL-redirect is returned to the NAD. These values are the IP address and port number for the Cisco ISE guest portal server
Hope this helps
Thank you, that is great.
Thanks for having a look at my earlier post.
I would like to avail your valuable inputs to understand on the Client provisioning part for the Mobile Devices/ Laptop. I understand from your reply that MDM integration is not available in the current release ISE 1.1
Kindly let me know your views or any documents on the following scenarios with the current release in mind
User with Mobile devices connecting to Wireless ( both Employee and Guest ) , How the Flow differs for the Employee and Guest. How the client provisioning is done ( i.e. Like Posturing or Compliance Check ).
User with Laptop connecting to Wireless ( both Employee and Guest ). How the client provisioning is done ( i.e. Like Posturing or Compliance Check ).
What are advantages of having ISE also in place for Mobile devices, since most of the Mobile related tasks ( like Authentication, Authorization, Profiling and Posture ) are carried out by MDM. I am checking for the significant advantage of having ISE for Client network having only Mobile devices. Kindly clarify.
Do you recommend 802.1X Authentication to use for the Employee and Contractor? The Guest user authentication as Open ?
How can we ensure the Encryption of traffic from the Guest user to the NAD ( Network Access devices ) ?
We are also looking for VDI ( Citrix, VMware ) solution for the client ( both Employee and Guest ) , how ISE can play a role in securing the VDI environment.
Is that any integration required with Citrix or VMware. How the VDI can be offered based on the User role ( i.e. Employee, Contractor or Guest ), since Guest database is available only with ISE, how the checks are made from the VDI environment.
Our solution demands MDM in the integrated solution, As on today ISE cant be integrated with MDM. so what kind of solution we can propose to have MDM and Cisco ISE .Do the clients now enter the network should have already installed the MDM agent (or) any other way of pushing the same to the Client.
Hi Arun,
First off let me clarify that today with ISE1.1MR, you CAN check to see if a MDM agent is installed and do something about if it is/isn’t installed. What you CAN’T do today is use ISE to view what the MDM agent is looking for. For example, you CAN check to see if Zenprise is installed and based on that with other things, provision specific access. You CAN’T have ISE kick somebody off the network if they fail a MDM policy such as having a iPAD jailbroken. The assumption is, if there is a MDM agent, its probably secure. A future release of ISE is suppose to be able to leverage the MDM agent so you can kick people off the network who fail a MDM policy.
Regarding your questions, the flows can be designed many different ways. Employee polices can range from checking for how people authenticate, what types of devices they have, searching for things like certificates to verify they have issued devices, etc. Enforcement can be through combinations of VLANs, ACLS, SGAs, dACLs, etc. Guest can be the same way however common practices are to leverage the build in advanced guest services such as web redirection (like a hotel), self provisioning (IE filling out a form and having a password generated), on-boarding (self approving the MAC of the guest device), etc. I’ll be posting more about certificates and on-boarding shortly.
Posture can be enforced through a Agent or agentless. THe idea is the agent only pops up when it sees somebody is connecting and quickly provides the user posture status. This is also key for sigle sign-on with posture. Without an agent, a system can be assessed with a JAVA or Active X web scanner however it takes a short time to scan and auto remediation is not possible (IE it will tell you to click a link or something similar to get a patch rather than auto patching). Remediation options can also very depending on how you configure the system.
I do recommend using 802.1x, MAB if 802.1x is not available and default with guest access.
When you ask about the encryption, are you concerned about man in the middle attacks while guest users authenticate? Please elaborate on what you are looking for.
VDI aka sandbox is an approach for provisioning access to specific applications from untrusted networks. For the internal network, ISE makes complete sense for locking down who and what is on the network (IE printers, card readers, laptops, etc). For remote access, you may want to control which devices connect to the sandbox (IE only issued devices). Also, you may want to verify there is AV, patches, etc to avoid things like keyloggers that can capture sensitive data during a sandbox session. Some VPN solutions offer these features as well (ex Cisco ASA can do posture and look for keyloggers). The only downside is now you have to manage to systems to identify who and what is coming on the network. The last comment I’ll make on sandboxes is that in many cases, people tend to work around them to be work done (IE email internal docs to personal email, screen shots, etc). Sandboxes are good but having some access control around who can connect to the sandbox is better.
Regarding pushing out MDM agents, there are different ways depending on the vendor. Most offer methods to email, push SMS, send users to a specific link, etc. ISE can redirect a device without a MDM to a link to download it if it sees the MDM is not present. Pushing MDM can be done many ways.
Hope this helps
Joey
Dear Joey,
Thanks very much, Am running with busy schedule and back to the post today.
We are also now planning to extend the BYOD for Ipv6, kindly let us know the support of ISE for Ipv6. Or what else can be showcased for BYOD for ipv6.
Hi Arun,
Currently ISE 1.1.1 doesn’t support IPV6. Its a roadmap item for next year.
Hi Joey,
Appreciate your efforts to help out engineers with new ISE deployment. I am running POC in the lab. Can we use ISE 1.1.1 for machine authentication based on certificate instead of AD?
In my use case, we have to check if there is a company issued cert on Windows laptop or Apple laptop or iPad or Andriod. If the cert is confirmed and the user has valid ID as an employee then the machine will be connected to company’s network. Thanks for your reply in advance. Adil.
Hi Adil,
Yes you can and its a common use case. I’ve seen people validate that machines are company owned, what version of “ghost” image is running via checking the dates of the cert to verify if a machine has been out in the field too long and other use cases. Its done via a posture check. You can see the workflow of this via the Task Navigator on the top right hand part of the ISE GUI (scroll to CP and Posture). Look under create policy conditions and you will see a registry condition section. Thats were you can look for specific certs. That or you can use MAB to verify approved devices and check for policies via authorization policies once they pass the internal MAB list (IE create a MAB authentication policy for issued devices and specific authorization policies if they fall in that bucket).
Hope this helps!
Greetings from Colorado! I’m bored at work so I decided to browse your blog on my iphone during lunch break. I enjoy the info you provide here and can’t wait to take a look when I get home.
I’m surprised at how quick your blog loaded on my mobile .. I’m not even using WIFI, just 3G .
. Anyways, excellent blog!
[WORDPRESS HASHCASH] The poster sent us ‘0 which is not a hashcash value.