David Balaban from Privacy PC wrote an interesting article about the Google Maps services. My buddy Aamir Lakahani has also done some talks on compromising mobile apps to gain access to their location data and applying it to Google Maps to track movement. It’s an interesting concept using Google Maps for nefarious purposes. Here is the article from David Balaban. This blog appreciates his contribution.
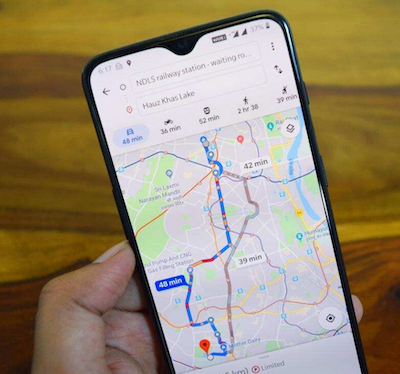
Google Maps, the web search giant’s proprietary geolocation service, is an instrument whose importance is difficult to overestimate these days. Not only does it help people find their way in unfamiliar places, but it also bridges the gap between businesses and potential customers who want to drop by.
However, there are exploitation vectors that may misguide Google Maps users or even get them in trouble. Why on earth would anyone want to do this? Well, there are plenty of reasons. One of them is to sabotage a competitor’s café or store by deceiving clients into thinking it’s currently closed. The other is to get someone ambushed by making them head in the wrong direction.
Believe it or not, some of these stratagems are ridiculously easy and inexpensive to execute. The stories below demystify a few notorious Google Maps Hacks and explain how they work.
Traffic Jams That Aren’t There
In February 2020, a German enthusiast named Simon Weckert spread the word about an incredibly simple way to manipulate Google Maps. All it took was a handcart with 99 used smartphones in it. One more component of the hack was a casual walk around the streets of Berlin with his odd-looking baggage. This innocuous adventure caused the geolocation service to display a red level of road traffic intensity along Weckert’s route. In other words, the person was able to spoof traffic jams.
Here’s the thing: GPS data from mobile devices located within a particular area is one of the sources fueling Google Maps traffic congestion measurement. If the algorithm spots a large number of smartphones in the same street and additionally identifies that these gadgets are moving at a low speed, then it interprets this combo of metrics as a telltale sign of a traffic jam. As a result, most drivers would take a different route to avoid pseudo congestion.
The Ghost Map Trick
Researchers from Microsoft, Virginia Tech, and the University of Electronic Science and Technology of China teamed up to demonstrate a Google Maps hack that can guide a car driver to a wrong destination. Unlike the above hoax involving business listings, this one is more complex than modifying crowdsourced search results. It relies on some equipment furtively attached to a vehicle.
To be precise, the analysts used a Raspberry PI single-board computer, HackRF One radio transceiver, an antenna, and a portable power supply. The total cost of this small-sized kit is just a little over $200. Its primary purpose is to forge satellite signals, replacing them with an attacker’s data.
Although this might seem like a commonplace GPS spoofing attack, the hack has a hallmark that makes it stand out from the crowd. It leverages what’s called a “ghost map” that resembles the real one but has a number of subtle differences. This way, the fake route is less likely to raise red flags. In the proof-of-concept under scrutiny, these faux maps were based on a dataset of 600 taxi trips taken in Boston and Manhattan.
When the hack is underway, a specially crafted attack algorithm determines the victim’s current whereabouts and finds a “ghost map” that closely matches this route. Then, the radio equipment transmits spoofed GPS signals so that the target’s Google Maps service is fooled into showing a rogue path.
Restaurant Closed? Not Really
A longstanding eatery called “Serbian Crown” in Great Falls, Virginia was once a popular place among gourmets. Famous for exotic meals in its menu, such as lion and kangaroo meat, it had been a prosperous business for almost 40 years until 2012 when things started getting out of hand. The owner, Rene Bertagna, found himself perplexed over a dramatic decline in the number of visitors for ostensibly no evident reason. It started out of the blue and went on for months.
The entrepreneur would have probably stayed clueless about the cause of this nosedive if one of the remaining customers hadn’t drawn his attention to a bewildering fact. The restaurant’s working hours shown on Google Places (now rebranded as Google My Business) turned out to be totally incorrect. The local business listings service relying on Google Maps misleadingly stated that “Serbian Crown” was closed on weekends, the time when the number of clients typically reached its peak.
It appeared that somebody had skewed information in Google listings to discourage visitors from going to the restaurant. This impacted the business badly because it was in a location with hardly any transit traffic, so people usually went there because they intended to. Having seen the “Closed” status on Google Places, a customer simply changed their mind and picked another place instead.
The dodgy tweak was most likely made by a competitor, although nobody was ever caught red-handed doing it. It took the owner more than a year to sort things out. He hired an Internet consultant who fixed the listings. By that time, though, he had lost most of his customers and fired some of the personnel. This made Bertagna call it quits and close the place – for real this time.
The fight for justice went on in the legal domain as the entrepreneur filed a lawsuit against Google. He and his lawyer boiled the case down to imperfections of Google Maps, which supposedly allowed an adversary to ruin his business by modifying the listings.
As a matter of fact, these claims make quite a bit of sense. The loopholes stem from the crowdsourcing gist of the service. It means a fraudulent community edit or bogus business profile may distort the online presence of an enterprise, and Google’s verification mechanisms aren’t effective enough to thwart this. There are quite a few similar examples of exploitation, including millions of fake listings with spammy company names. The biggest issue is that Google appears to have a hard time differentiating phony profiles from real ones. In spite of these evident flaws, Bertagna got nowhere with the lawsuit.
The Bottom Line
Google Maps is definitely an awesome service, and yet it’s far from being flawless. Cybercrime statistics show us that nothing can be safe these days. The Google Maps service turns out to be susceptible to exploitation – from inundating location-based business listings with fake profiles and inaccurate information, to displaying spoofed maps and simulating traffic jams. The terrifying thing is that these hacks can go beyond the cyber realm and have real-world consequences for people. With that said, Google engineers should rethink some of the anti-fraud and security implementations related to their navigation services to make sure that regular users are on the safe side.
David Balaban is a computer security researcher with over 15 years of experience in malware analysis and antivirus software evaluation. David runs the Privacy-PC.com project which presents expert opinions on contemporary information security matters, including social engineering, penetration testing, threat intelligence, online privacy, and white hat hacking. David has a strong malware troubleshooting background, with the recent focus on ransomware countermeasures.