My buddy Aamir Lakhani wrote a great post covering the recently exposed security vulnerability that impacts more than half of the websites on the Internet. Its something everybody needs to be aware of. The original article can be found HERE. 
Heartbleed is a serious vulnerability affecting OpenSSL cryptographic libraries. The Heartbleed vulnerability allows an attacker to steal information protected under normal SSL TLS conditions.
Here is what you need to know:
- This is a very serious vulnerability.
- It harms personal computers and everyday users. Attackers could possibly steal user information.
- Many popular websites, including social media, search, email, banking, and health sites are vulnerable.
- The bug is found on most systems and has been present since 2012.
- Most likely, attackers knew about the vulnerability, and may have been exploiting it for a long time.
- Patching and updating systems will not protect owners from attackers who have already captured data.
The bug allows a remote attacker to read up to 64 bytes of memory. The attack works against clients and servers. Critical information such as private keys, passwords, access methods, and other sensitive information is stored in memory. Attackers could exploit web servers they are browsing, or they could exploit client machines such as Linux, Mac, Windows, and Android systems.
Keep in mind attackers only have access to a limited subset of the memory buffer, however, the memory may contain a website’s SSL private keys and other passwords.
Web site owners are encouraged to change and re-key their SSL certificates. If encrypted data was captured and stored by an attacker, or a third party, and if this attack is used to successfully obtain the private keys, then an attacker or a third party could potentially decrypt and read the old captured data.
If you are using a personal computer, connecting to open wireless networks by using and OpenSSL VPN, attackers could intercept your traffic and compromise your data. If you are not sure if your VPN device is vulnerable, I would work under the assumption SSL VPN tunnels are not keeping you secure. I have no doubt all major vendors that are vulnerable will be issuing fixes within the next 48 hours if not sooner.
If you are using any modern type of Unix or Linux system, then you are most likely vulnerable to the bug. Microsoft IIS servers use the Microsoft Windows Crypto Implementation, therefore are not vulnerable.
Furthermore, Windows systems that are using modern web browsers are not vulnerable since they use the Window Crypto library for SSL. There are many other applications for Windows and other operating systems, including OpenSSL VPNs that are vulnerable since they use the OpenSSL libraries.
The Heartbleed bug was introduced in OpenSSL 1.0.1 and is present in
- 1.0.1
- 1.0.1a
- 1.0.1b
- 1.0.1c
- 1.0.1d
- 1.0.1e
- 1.0.1f
Check if you are vulnerable. “openssl version -a” will return the version information. You should be running version 1.0.1g, which is NOT vulnerable. Older major versions before 1.01 (0.9x, 1.0.0 …) are not vulnerable either.
Additionally, there is a Metasploit module for the attack that can be found here:
https://github.com/rapid7/metasploit-framework/pull/3206/files
Cisco ASA Firewall customers are protected
The Cisco ASA is one of the most popular firewall and VPN devices in the world. With the ASA you can determine the version of OpenSSL implemented from the ASA release notes. Examine the “Open Source” notes that are located in the release notes of the particular ASA image you are concerned with.
For example, from the ASA 8.4 release notes, you will find a section titled “Related Documentation”, which has a link that points to “ASA Series Documentation”. From there, you will find a link for “Open Source License”. That will take you to an “Open Source” page which reveals that the OpenSSL version that runs on the ASA 8.4 code is “0.9.8f”
Due to this 8.4 as well as 9.1 are not vulnerable as they are using parts of the OpenSSL version 0.9.8f (source:
If you are using the Cisco ASA for SSL VPNs, it appears you are not vulnerable to the bug (I am assuming the product had been implemented correctly, with proper architectural design, and mitigating controls). Most VPNs that implement IPSEC VPNs should not be vulnerable as well.
F5 Customers are Protected
F5 Big IP solution is used to protect, load-balance, and provide other advanced features to public facing websites. If your organization has been using the F5 solutions, you are protected from attackers against this vulnerability (I am assuming the product had been implemented correctly, with proper architectural design, and mitigating controls).
BIG-IP platforms support NATIVE and COMPAT SSL stacks. Each SSL stack supports a different set of SSL ciphers. The COMPAT stack is a variant of OpenSSL 0.9.7. The COMPAT stack supports the ciphers that the NATIVE SSL stack supports, in addition to ciphers from the OpenSSL suite.
Source:
http://support.f5.com/kb/en-us/solutions/public/13000/100/sol13163.html
Please note, this list is not inclusive, these are just two very popular products.
What should you do
- There is no current forensic method to test if your system has been exploited. If you are using OpenSSL, update OpenSSL, and re-key or re-issue your SSL certificates. Patching and updating alone are not enough.
- If you are user that goes to SSL protected sites, change your passwords. Yes, change all your passwords. for services like Gmail, Yahoo etc, there is no telling how long the criminal underground or attackers have had this vulnerability.
OpenSSL is by far the Internet’s most popular open-source cryptographic library and TLS implementation. It is the default encryption engine for Apache, nginx, which according to Netcraft runs 66 percent of websites. (Source: http://news.netcraft.com/archives/2014/04/02/april-2014-web-server-survey.html)
- Don’t use OpenSSL or connect to untrusted, open, or public networks or hotspots until you can confirm your VPN client is not vulnerable.
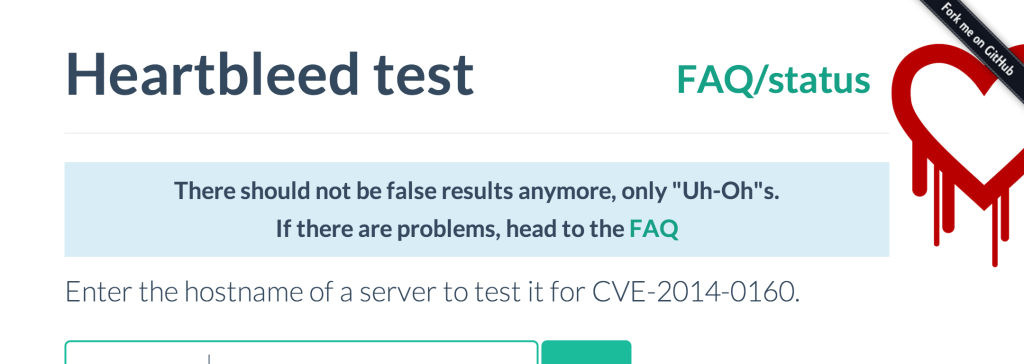
- Do not visit, or use websites that are vulnerable to the attack. You can check if a website is vulnerable to bug by going to http://filippo.io/Heartbleed
Tools and IDS Detection
- On-line service to verify vulnerability: http://filippo.io/Heartbleed/
- Code to above tool: https://github.com/FiloSottile/Heartbleed
- Python script to verity exploitability: http://s3.jspenguin.org/ssltest.py
Detecting with Snort – v1
NCCGROUP has also posted some signatures for Snort and Suricata. The following signature can be used to detect the use of the ssltest.py script and maybe other using TLS 1.1. No warranty is implied or otherwise etc…
|
1
|
alert tcp $EXTERNAL_NET any -> $HOME_NET 443 (msg:"Potential Heartbleed attack with ssltest.py";flow:to_server,established; content:"|18 03 02 00 03 01 40 00|"; rawbytes; isdataat:!1,relative; reference:cve,2014-0160; sid: 6000000; rev:1;) |
Please note the following caveats to this detection string:
- This will only detect ssltest.py specifically
- The attack can use TLS 1.1 or 1.2 (filippo.io uses 1.2)
Detecting with Snort v2
NCC group has developed a further Snort signature that is more generic that will likely catch attempts to exploit the vulnerability that do not use the publically available script:
|
1
|
alert tcp $EXTERNAL_NET any -> $HOME_NET 443 (msg:"Potential Heartbleed attack";flow:to_server,established; content:"|18 03|"; rawbytes; depth:2; byte_test:1, &, 3, 0, relative; byte_test:2, >, 200, 3, relative, big; reference:cve,2014-0160; sid: 6000001; rev:2;)<br><br> |
Detecting use Suricata
Details can be found on blog.inliniac.net
Ubuntu patching
Ubuntu 1.0.1-4ubuntu5.12 of OpenSSL resolves the issue. However it is important that if you wish to resolve this vulnerability for an Apache install that you also upgrade libssl specifically e.g. apt-get install libssl1.0.0 or you run the risk of upgrading OpenSSL but not actually resolving your exposure.
Source: https://www.nccgroup.com/en/blog/2014/04/heartbleed-openssl-vulnerability/