My buddy and coauthor Aamir Lakhani and I are very proud to present our second book … “Penetration Testing With Raspberry Pi“. This book can be found on Packt’s website HERE and should start being seen on most online stores such as Amazon, Barns and Noble the next few days.
 Our first book talked about web penetration testing with Kali Linux (found HERE and new Chinese version found HERE … I also posted the Chinese cover above). This new book focuses on penetration testing using the low cost Raspberry Pi form factor. Why use a Pi? Well some advantages are purchasing a Pi is cheap, they can be shipped anywhere and are easy to hide at a target’s location. This gives you a insiders advantage verse the traditional hiding a laptop or remote attack. The next shows hiding a Pi in a cat clock that is powered via USB battery for wireless pen testing.
Our first book talked about web penetration testing with Kali Linux (found HERE and new Chinese version found HERE … I also posted the Chinese cover above). This new book focuses on penetration testing using the low cost Raspberry Pi form factor. Why use a Pi? Well some advantages are purchasing a Pi is cheap, they can be shipped anywhere and are easy to hide at a target’s location. This gives you a insiders advantage verse the traditional hiding a laptop or remote attack. The next shows hiding a Pi in a cat clock that is powered via USB battery for wireless pen testing.
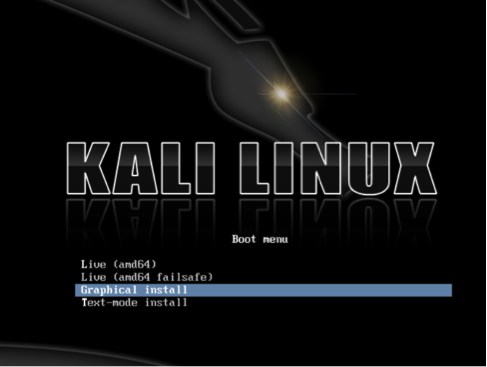
We cover how to install Kali Linux as well as other attack arsenals on a Raspberry Pi, how to launch various attacks, covering your tracks and techniques to deliver professional penetration testing reports. The is smaller than our last one since its very focused on hacking with a Pi.
Here is the basic information about our book. Hopefully you enjoy it as much as we did writing it!
About This Book
- Learn how to turn a Raspberry Pi into a Kali Linux hacking toolkit for onsite, physical, and remote penetration testing
- Understand the capabilities, limitations, and features of Kali Linux on Raspberry Pi
- Build and develop methodologies ideal for Raspberry Pi penetration testing using real-world cases
Who This Book Is For
If you are looking for a low budget, small form-factor remotely accessible hacking tool, then the concepts in this book are ideal for you. If you are a penetration tester who wants to save on travel costs by placing a low-cost node on a target network, you will save thousands by using the methods covered in this book. You do not have to be a skilled hacker or programmer to use this book. It will be beneficial to have some networking experience; however, it is not required to follow the concepts covered in this book.





One thought on “Penetration Testing with Raspberry Pi – Book Now Available!”