Aamir Lakhani from drchaos.com wrote a good article on how chaining together social engineering tactics compromised a highly visible twitter account. The original post can be found HERE.
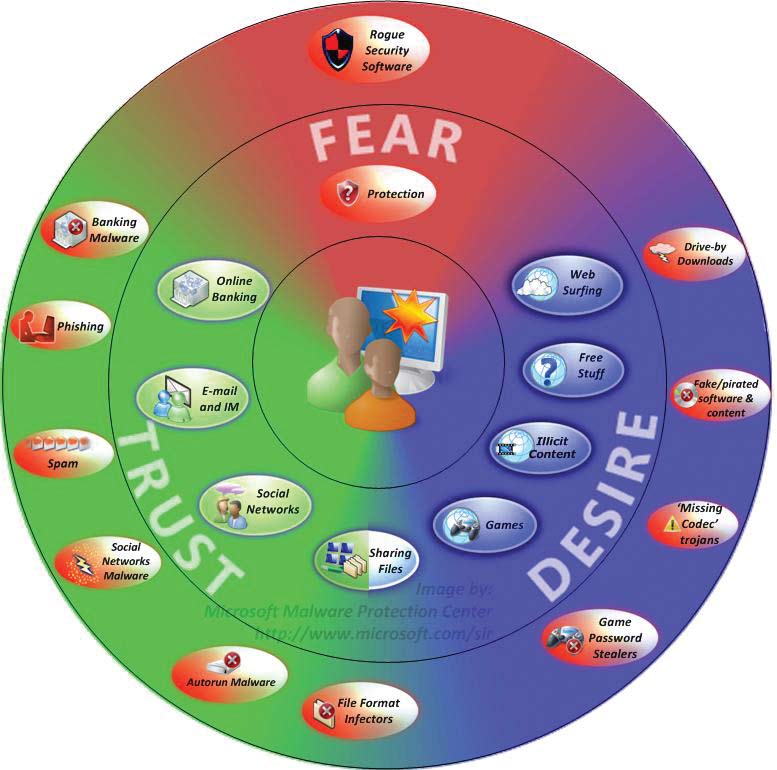
Who can we trust? It’s a tough question. We think we can trust our friends, co-workers, mentors, and colleagues because they are people we see and interact with often as frequently as we do with our family members. Unfortunately, there is risk in trusting others, particularly when those we trust have privileged access to our accounts and sensitive information. When our trust and exposure extends to those who we work with, and incorporates intimate knowledge of our business concerns, corporate cultural developments, and technology secrets, we must face the reality of insider threats. Unlike external attackers, those we consider to be on the inside of our trust circles do not need to hunt for valuable information, nor do they need to exploit strong perimeter defenses; insiders already know what is valuable and where it is stored.
Of course, corporations are not individuals, but like people, corporations also have privileged insiders, including system and database administrators, and users such as these, and others, have unusually high levels of access to information, and can target the heart of the enterprise. Additionally, these privileged individuals can often erase all traces of their activities.
According to the Office of the National Counterintelligence Executive, attacks originating from insider threats are perpetrated by employees who have been with the organization for many years, and are normally in non-technical positions. (Source: http://www.ncix.gov/issues/ithreat/).
Naoki Hiroshima, creator of @Cocoyon, Developer for @Echofon, had his Twitter account stolen last week. The Twitter handle of @N once brought Mr. Hiroshima $50,000.00 USD. Mr. Hiroshima details exactly what happened on: https://medium.com/cyber-security/24eb09e026dd
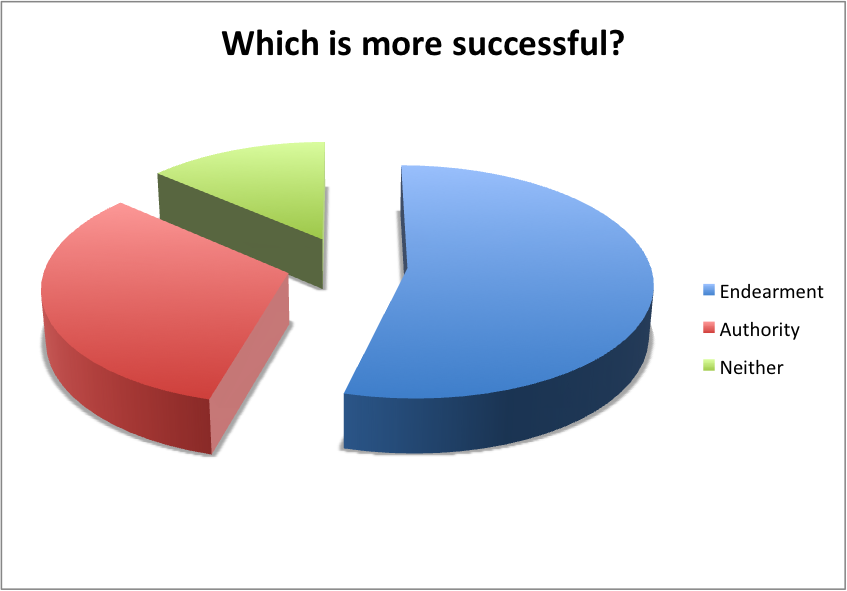
Attackers conducted a classic chained exploit. A chained exploit means that multiple methods were used to gain access to private or privileged information.
In this case attackers were able to call PayPal and use social engineering skills to obtain the last 4 digits of the credit card on file. Rumor is they acted as a PayPal employee. This may seem trivial, after all the last 4 digits on most credit cards are widely distributed, left on receipts, and used for verification. NOTE: You can call PayPal and ask them to note your account not to give this information out over the phone.
The attackers than used this information to change Mr. Hiroshima’s GoDaddy domain information. The attackers described what they did, “I called godaddy and told them I had lost the card but I remembered the last four, the agent then allowed me to try a range of numbers (00-09 in your case) I have not found a way to heighten godaddy account security, however if you’d like me to recommend a more secure registrar i recommend: NameCheap or eNom (not network solutions but enom.com)”
The attackers recommended to Mr. Hiroshima that he not use GoDaddy. Once the attackers had control of Mr. Hiroshima’s domain, they were able to easily gain access to email, reset Twitter accounts, and take it over.
A couple of classic mistakes were made here. Two-factor authentication was turned on PayPal. I would go further and use a strong authentication method such as Yubi Key (http://www.yubico.com/applications/internet-services/paypal-ebay/).
It is shocking that even with these secure methods, the same attack would work because PayPal released the last 4 digits of the cardholder’s credit card. If you use PayPal, call them and put a note on your account to never release this information.
The attacker used this to try and take over domain accounts from GoDaddy. The attacker described in an exchange with Mr. Hiroshima:
Yes paypal told me them over the phone (I was acting as an employee) and godaddy let me “guess” for the first two digits of the card
But guessing 2 digits correctly isn’t that easy, right?
From: <[email protected]> SOCIAL MEDIA KING
To: <*****@*****.***> Naoki Hiroshima
Date: Mon, 20 Jan 2014 20:09:21 -0800
Subject: RE: …hello
I got it in the first call, most agents will just keep trying until they get it
He was lucky that he only had to guess two numbers and was able to do it in a single call. The thing is, GoDaddy allowed him to keep trying until he nailed it. GoDaddy does not at this time offer any Yubi Key authentication, or any other type of two-factor authentication.
Mr. Hiroshima last mistake was, all his accounts were linked to the same email address, using his domain. He had his MX record TTL set extremely low, so when the attack occurred, he almost immediately lost access. Mr. Hiroshima would have been much better if he used different email accounts for Twitter, GoDaddy, and PayPal. Even more so, if he used widely used email domains such as Gmail, he could have turned on two-factor authentication for each one o his accounts.
Mr. Hiroshima was not the only victim last week. The Syrian Electronic Army(SEA) hacked into the MakrMonitor account managing the Ebay and Paypal domains. (http://www.ehackingnews.com/2014/02/ebay-and-paypal-uk-domains-hacked-by.html#sthash.8OjqjQX1.dpuf). This attack used spear phishing techniques and multiple chained exploits to compromise the systems.
Data is difficult to protect, and becoming more valuable to attackers as they narrow their targets. They key to protecting data will not be about prevention, but more about detection and how fast you can response and react. No doubt, this will be difficult to achieve, but if information security specialist continue to focus on prevention tools and solutions, they will leave their systems extremely vulnerable and exposed to attacks.