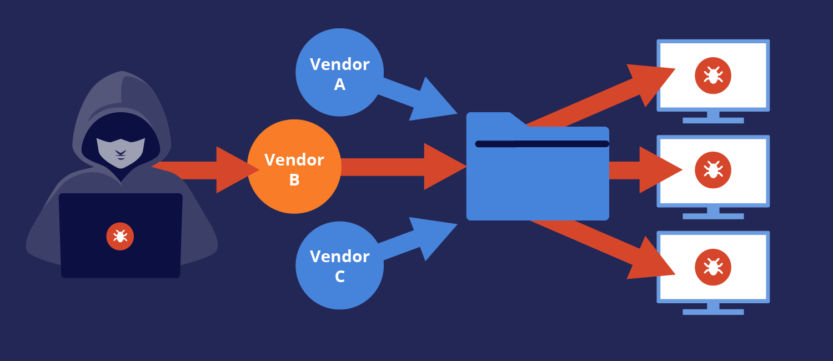
Supply chain attacks have become a huge scare in the industry since the Solarwinds attack. The question is simple … What is the risk of the technology I’m installing or using today based on what occurred prior to my team acquiring the technology. Think about buying a IoT device. It is very likely the manufacture of that solution did not build all of the components. The memory, chips, possibly even part of the software was developed by a 3rd party resource and the primary manufacture is essentially assembling everything into something you buy. What happens if a backdoor or other threat is planted into that device? Does a small IoT company have the skill, tools, or focus to look for these threats? In this example, I’m picking on a small IoT company but the same concept applies to enterprise technology providers. Hence …. the fear of supply chain attacks. This relates to all technology providers and something that is next to impossible to check for across all of the technology within your network.
All is not lost regarding what you can do. The best defense against supply chain is working with vendors that invest in protecting their involvement with 3rd party resources and including methods to validate hardware and software isn’t counterfeit or modified. I find when I compromise a IoT device, it is due to allowing me to modify the code or phish a customer to install a fake software update that I have modified via adding a back door. I find most IoT devices allow any version of software to be installed as long as it is a certain format and file is a certain file size. There isn’t a counterfeit verification hence allowing back doors to be installed by an attacker.
So what can you do? You need to start asking vendors you work with how they are securing their solutions against supply chain attacks. You also need to ask how software updates are validated against modification. If you don’t get a strong answer, you need to assume the risk exists and consider the potential impact. Thats it … clear and simple.
To give an example of what you hope to see when asking these questions, Cisco has a public resource found at https://tools.cisco.com/security/center/resources/anticounterfeit that explains what is done to protect against supply chain attacks as well as how software code is validated before installed. If you attempt to run a back door on a Cisco switch, the software install process validates if the code has been modified prior to allowing install. If you are concerned if the switch has already been breached prior to arrival, Cisco explains how they secure technology from build to delivery. You need to find evidence of these steps and ask for something in writing explaining how it is done from vendors you do business with. You can’t just assume supply chain defense is in place or take a person’s word that it is being done. If there is a failure, you are the one stuck with the impact of the breach.
Many enterprise vendors are offering these resources to help address concerns for supply chain attack. My suggestion is to ask these questions and include supply chain evaluation as part of your risk management program. Hope this helps address your concerns for supply chain attack.