Like many of you, I’m really looking forward to things returning back to how they use to be prior to COVID. This includes returning to live events such as RSA. My buddy Aamir Lakani and I will be presenting June 8th at 8:30am on our BotNet research. You can find info on our talk HERE. I’ll also be DJing at Microsoft’s tuesday party and around the event all week. Please say hello if you are out there and see me. Say “whats up security blogger”.
I want to give a primer for our talk. I’ll also follow this post with details about what we cover next week. The topic is on resurrecting Botnet. I assume most readers know what a Botnet is aka an attacker controlling multiple victim systems remotely. I also assume it shouldn’t be shocking to most people that when a Botnet is taken down, the victim systems are still infected, but just not being abused anymore. The thought is could somebody like me identify victims of a dead botnet and resurrect them for my own evil deeds???
The first concept to understand before answering this question is understanding the components in a botnet. For simplicity purposes, I’ll break a Botnet into four parts.
- Command and Control (CnC): This is the management planform for the Botnet.
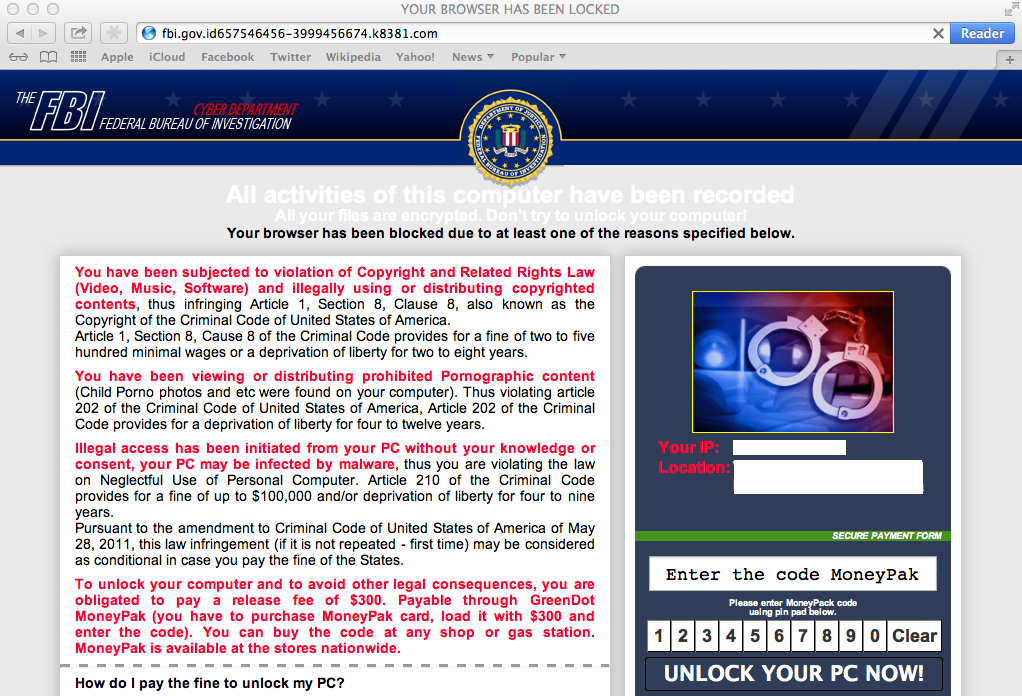
- Exploitation Technique: This is how the adversary gets the botnet software onto the victim’s system.
- Botnet software: This is what is the result of the exploit that is installed on the victims system to allow commands to be sent (beaconing type system) or full control of the system (such as a remote access tool RAT).
- Communication protocol(s): This is how the CnC speaks with compromised systems running the botnet software
When a Botnet is taken down, usually it means the CnC is disrupted. Maybe a government agency has taken over the CnC’s domain. Maby the threat actors shut it down. Maybe the CnC is compromised but when the CnC goes down, the infected systems stop receiving commands. Our interest is in the fact that those infected systems are still infected with the CnC goes down. So could somebody step in and take over those systems? Imagine your organization has hundreds of systems infected years ago by a older botnet and tomorrow somebody uses that old botnet software to gain access to the system acting as a new master.
The focus for our research is not on the CnC or exploitation techniques. We are not attacking CnCs and want to use our own new system. We are not interested in how the botnet spread as we can use more modern exploitation if needed to gain system access. We need to reverse engineer the botnet software to understand how it communicates and where it communicates so we can speak its language and send new commands. This means we are interested in the software installed and communication protocols used.
There are other topics such as modern botnets vs older botnets, the risk you put yourself in the mix of things when doing this, challenges with modern security tools and so on that we ran into and will address at the talk. In short, we were successful but not exactly like you are probably think. I’ll explain those details after our talk in a part 2 post. We learned a ton and hope you enjoy the talk. Look out for Part 2 after RSA / next week.