My buddy Aamir Lakhani wrote about how traditional security products such as Stateful firewalls and older IPS/IDS solutions are not cutting it for today’s level of threats. This post covers why the “Next-Generation” of security technology matters. The original post can be found HERE.
Organizations are replacing their Stateful firewalls with Next-Generation firewalls (NGFW) and Next-Generation Intrusion Prevention systems (NGIPS). Most traditional firewalls are nothing more than packet filters that keep track of who initiated the traffic to automatically allow response traffic back to originator. IPS vendors such as Sourcefire and McAfee (Intel Security) are rapidly adding advanced features to protect against insider threats, application vulnerabilities, mobile devices, and malware. One must wonder are the days of traditional perimeter security devices such as Stateful firewalls and single-pass IDS systems numbered?
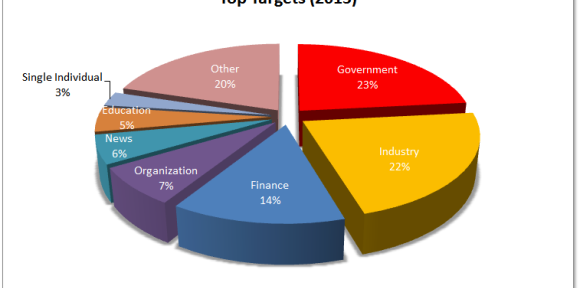
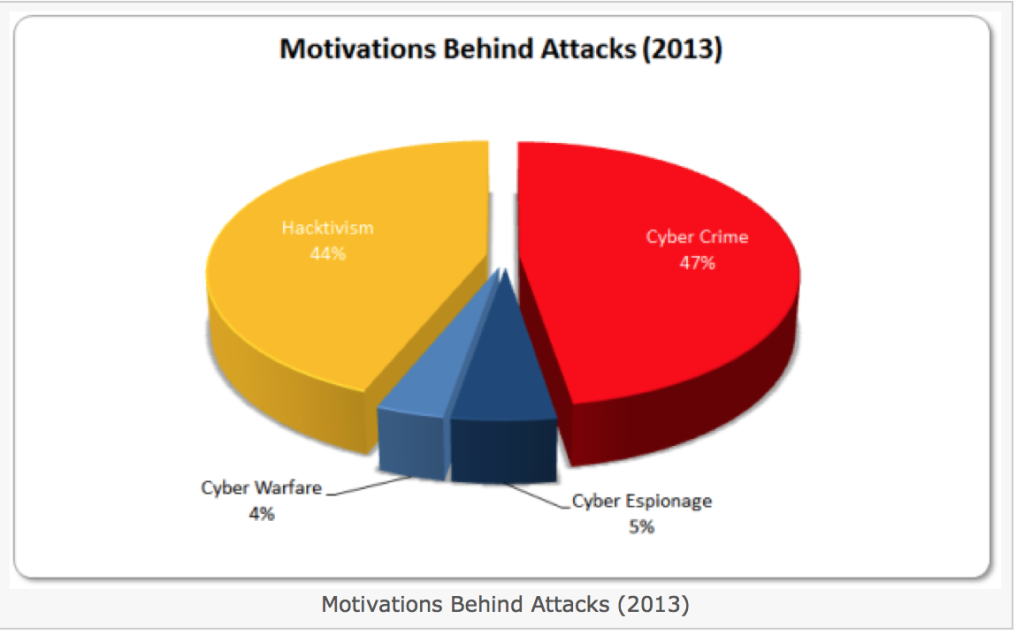
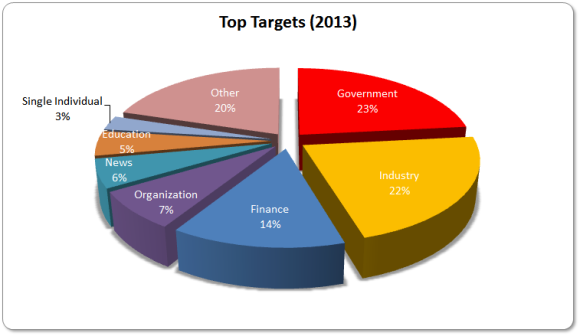
source of graphic: http://hackmageddon.com/category/security/cyber-attacks-statistics/
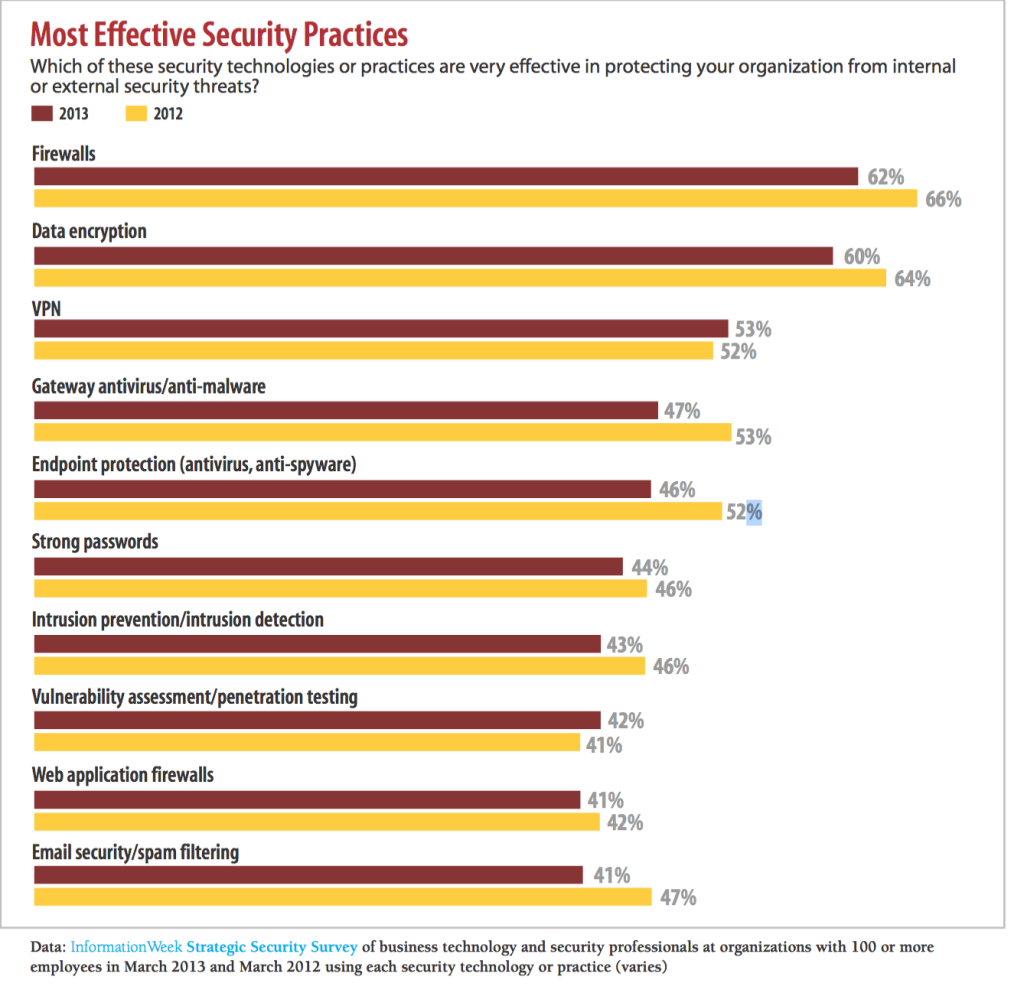
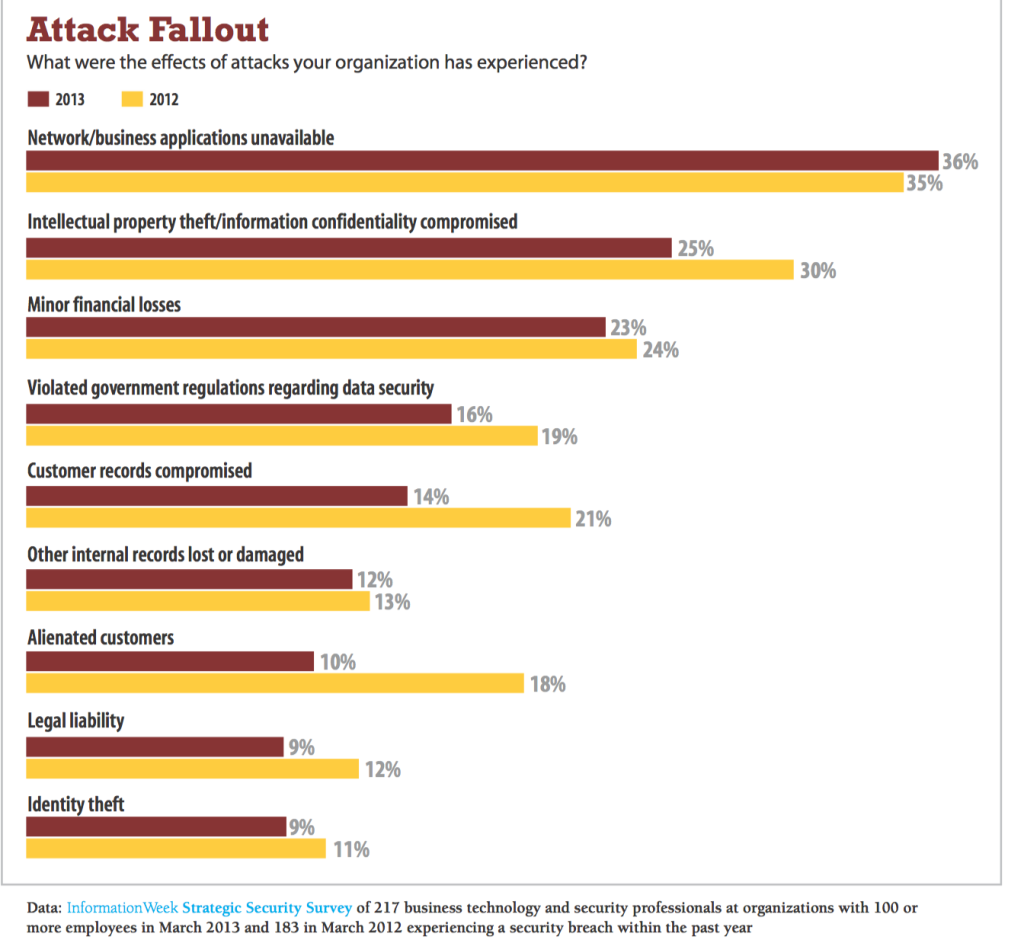
Cisco Systems estimates that the NGFW/NGIPS market will be over $4 billion in the next 2 years. The new ASA-X series appliance combines advanced NGIPS and NGFWs in a single appliance. By Cisco’s own estimates their customers will be replacing and upgrading ASA firewalls to a next-generation appliance in the next 3 years resulting is over a $2.8 billion in opportunities (source:http://www.cisco.com/c/en/us/products/security/asa-next-generation-firewall-services/index.html). The data suggests that the IPS still has relevance, but traditional first generation IPS systems are slipping on how effective they are perceived in stopping attacks. In the 2013 InformationWeek Strategic Security Survey, 43% of security professionals considered IPS to be “highly effective” at securing and stopping advanced attacks. That response rate is down 3 points from the year before according to the same survey. The firewall did better: 62% of security professionals rated their firewalls as highly effective in 2013, though that was down from 66% in 2012. While the two systems stop different types of attacks, it’s clear that IT groups view the firewall as more efficient than the IPS. No wonder vendors are combing products into a single security appliance with next-generation firewalls and next-generations IPS systems.
IPS systems have generally been deployed as a perimeter defensive solution; usually sitting inside the firewall to detect attacks that have made it past the firewall. In some cases IDS/IPS systems are deployed outside the firewall as part of a honeypot project. They allow organizations to gauge the effectiveness of their firewalls in working to stop traffic, and determine what type of attacks are being blocked by their firewalls. Most IPS systems block known attacks by using signatures to detect attacks. The problem is today’s attack’s are unknown, sophisticated, and have some sort of social engineering component that IPS systems cannot detect.
source of graphic: http://hackmageddon.com/category/security/cyber-attacks-statistics/
NGFWs with NGIPS systems add the ability to inspect applications, not just packets. They understand what the behavior of applications and protocols are supposed to be according to their published standards. If traffic behaves outside this standard, it will mark this traffic as suspicious. These next-generation security appliances are taking the best feature sets of web filtering, anti-malware, firewall, and IPS technology and putting them in a single appliance.
Most critics will argue that the problem with integrated appliances is you get poor performance compared to individual dedicated appliances. I recently took a small enterprise class UTM (unified threat management) firewall, and turned on web filtering to block around 20 different categories of web traffic ranging from SPAM, Bots, and Web Advertisements, enabled malware scanning, and enabled IDS detection. My performance and usability of my outbound Internet connection dropped significantly. I went from 100Mbs download speeds, to under 2Mbs. This was not a scientific test, but after several configurations, I could confidently say the drop of performance was due to my configuration. My Internet traffic only returned to normal, when all advanced features were turned off. The top next-generation appliance vendors have found ways around the performance drop by providing clear guidelines on what features have what kind of performance impact, and producing specialized hardware that can handle the complexities of deep packet and application inspection.
Vendors such as Sourcefire, McAfee (Intel Security), and others are pushing “next-generation IPS” products that go beyond signature-based blocking. They are combining advanced features at performance rates above 40Gbs. They are also eliminating false positives or the reporting of incorrect vulnerabilities by learning about your network. This makes the tools much more valuable, because the data they report is much more accurate. Additionally, they not only still support a large number of signature detection protocols, they also understand content and can analyze applications and files such as java code or PDF documents.
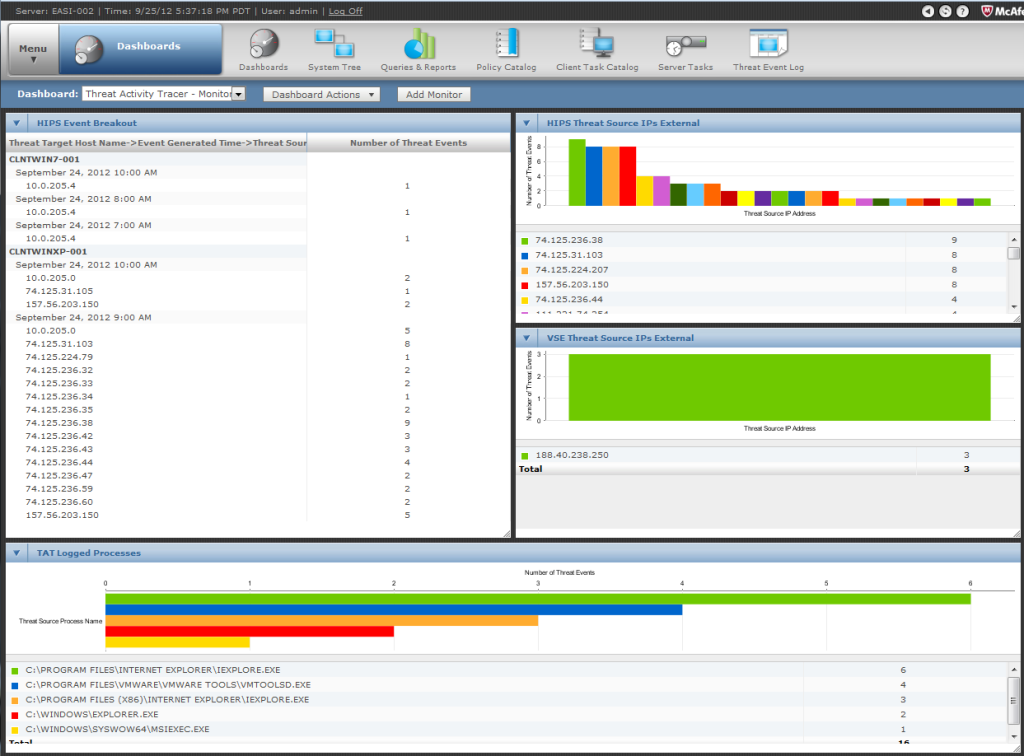
The value of next-generation IPS systems is that they are the modern next-generation monitoring tools. If you look at the top IPS vendors such as Sourcefire and McAfee (Intel Security), you can easily see the value they provide is their integrated dashboard, which provides a quick barometer of the current state of security in an organization. Intel Security’s EPO product provides reporting from several different security products into one dashboard that gives a 360 degree view of security posture for the entire organization. Sourcefire’s unique network trajectory system will let you traceback where attacks, malware, and insider threats originated from, and where possible sleeper cells or dormant malware may be residing on one’s system.
The powers of NGIPS systems are that they are modern day network monitoring and SIEM tools. They provide correlation of log and packet data, and integrate with vulnerability assessment tools. The naysayers who say the days of IPS systems are numbered may be right, but the days of next-generation threat management and detection are just beginning.