I recently stood up a Cisco 4345 Intrusion Detection / Prevention (IDS / IPS) appliance and documented the configuration process. Here is a simple guide to setup a next generation Cisco 4345 IPS appliance.
Overview
Cisco offers various forms of threat detection options that range from modules in firewalls to dedicated appliances such as the 4345 IPS. Regardless of platform, the underlying technology is similar using a mix of threat reputation described as identifying attackers and various forms of scanning for stopping attacks. An example of stopping an attacker is blocking websites with “bad credit scores” based on how long they have been up on the Internet, the content of the site, traffic seen from the site and so on. So a website claiming to be a American bank may get flagged based on being seen from a foreign country, recently registered as a new site and flagged for SPAM. The majority of attacks on your organization can be prevented by dropping obvious malicious traffic using this method. This leaves a security solution’s resource intensive detection processes the ability to focus on the remaining 5-10% of attacks that make it through credit scoring based detection rather than scanning everything.
Identifying attacks is made up of a combination of looking for specific matches for threats, structure data to identify polymorphic behavior, behavior associated with known threats and meta data. This layered with updates from the cloud based on what the rest of the world is seeing from an attack perspective gives the IPS its ability to catch threats regardless of how they attempt to bypass standard security detection technology. Cisco now owns SourceFire meaning all the open source projects such as SNORT and ClaimAV also contribute to attack prevention research.
Cisco 4345 IPS Configuration
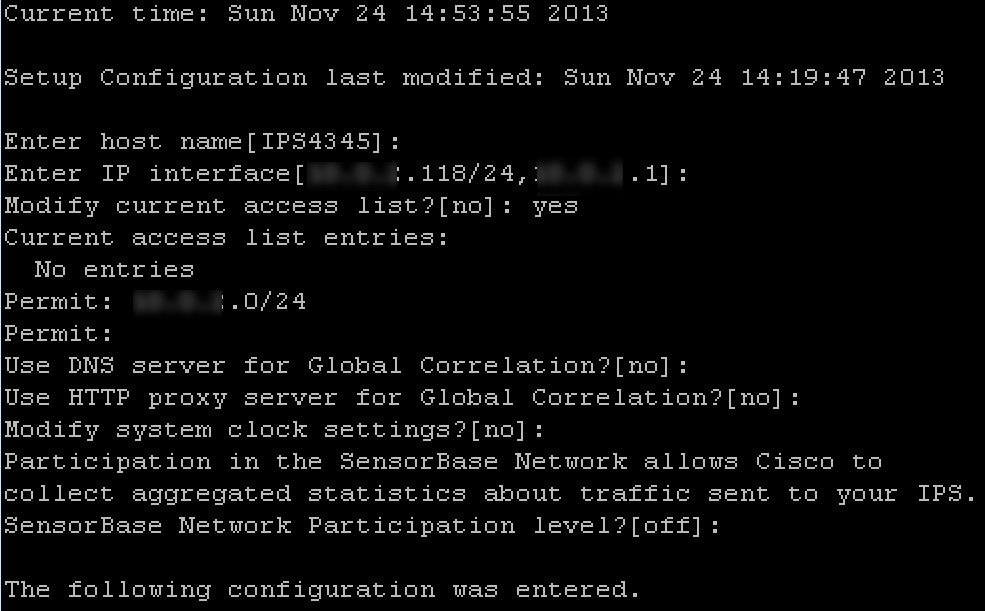
The first step to configure the 4345 is accessing the command line using the Console port. The default login is cisco / cisco. It will ask you to change the default password at the first login. Once in, type setup to enter the basic configuration. The key items are entering an IP address with /subnet followed by a comma for the default gateway. So for example, 192.168.1.44/24,192.168.1.1 would be a device with .44 on a /24 network with .1 gateway. Another key piece is modifying the access lists, which are what is permitted to access the GUI. So you can do the entire scope by doing 192.168.1.1/24 or pick specific IP addresses.
NOTE: If you don’t add a device to the access list, you will not be able to access the IPS GUI.
Basic Cisco IPS 4345 CLI Configuration
Confirming Basic Cisco IPS 4345 CLI Configuration
Once complete, select option 2 to save and exit. You should now be able to plug in a cable to the Management port of the appliance and access the 4345 IPS GUI using https://IpAddressOfAppliance. This will permit you to download IPS Manager Express (IME) to manage your appliance.
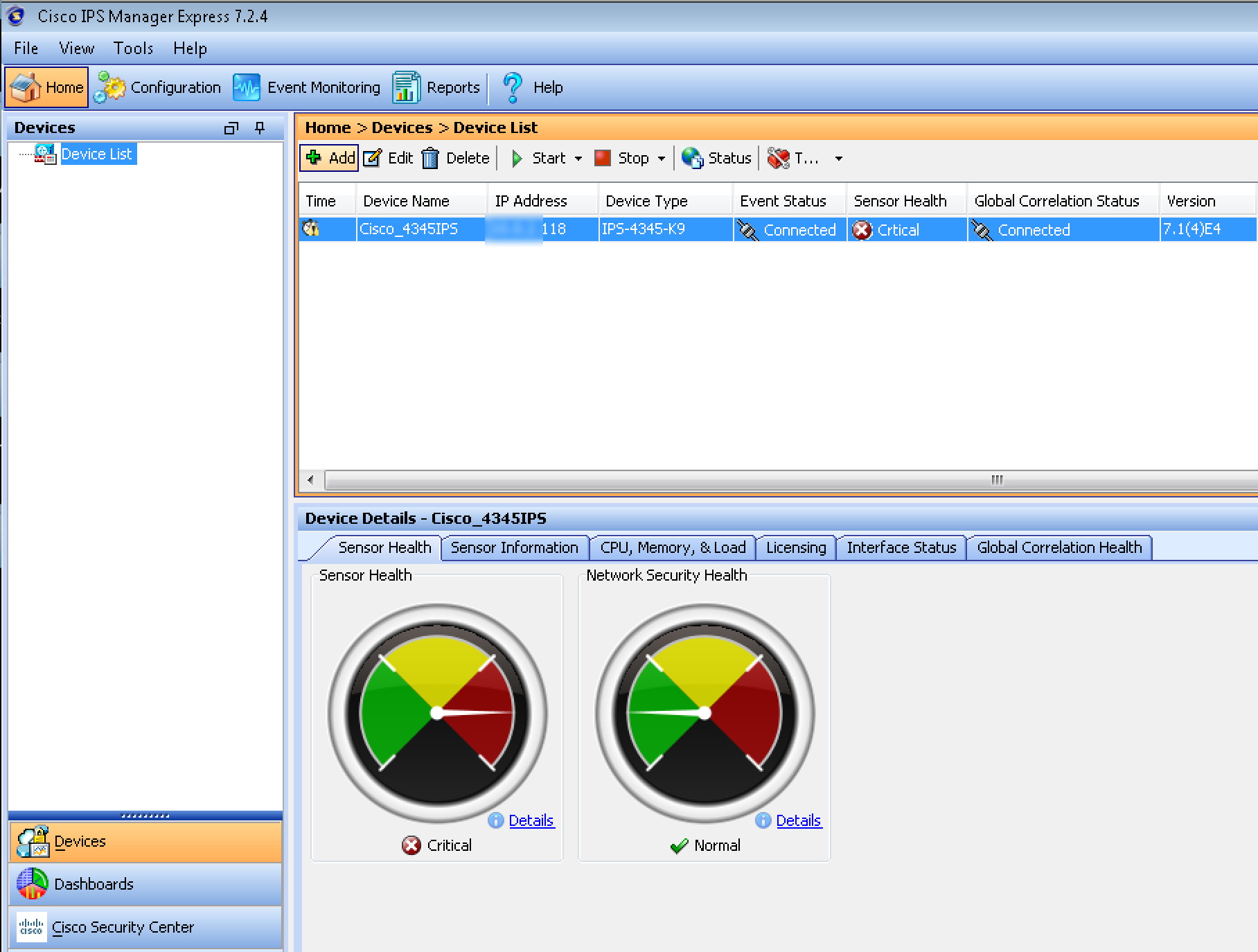
Cisco IPS Manager Welcome Screen
Once you open IME, click the Add button to add your IPS. You will be asked to fill out the basic information about your IPS. When you click next, there will be a prompt asking if you trust a certificate being pushed prior to the device being added. If the IPS and system running IME clocks are off by more than 5 minutes, there will be a warning about timing. At this point. You should see your sensor’s information in IME.
Adding a Cisco IPS 4345 to IME
Cisco IME showing a recently added 4345 IPS
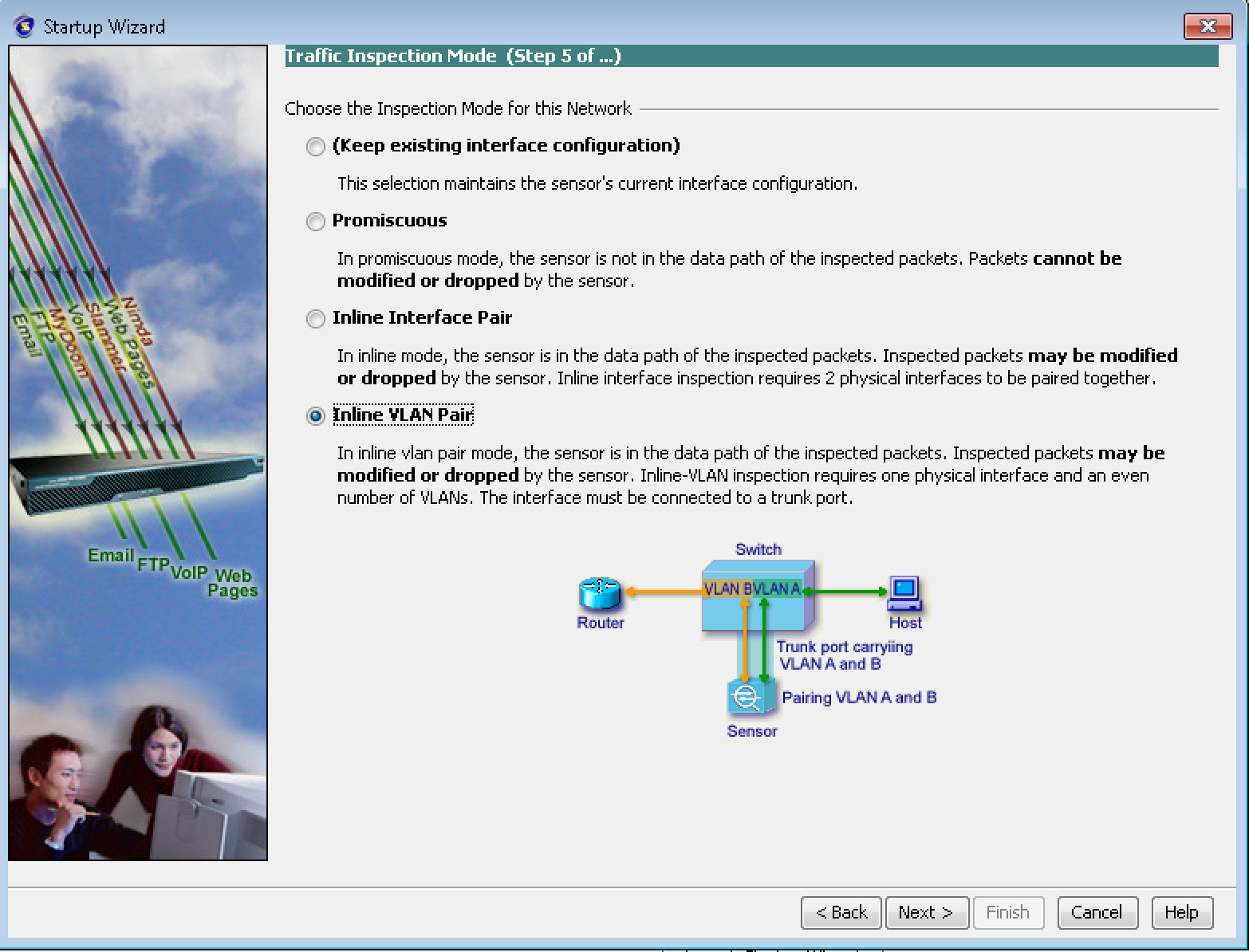
Now that you are managing your 4345 IPS in IME, you can configure the IPS to a specific security mode using the setup wizard. Modes are Promiscuous aka IDS (detection only), Inline IPS via Interface or Vlan. The image below explains the differences. The configuration wizard is found under configuration, sensor setup on the left tab and select the setup wizard.
Cisco 4345 IPS deployment options in Wizard
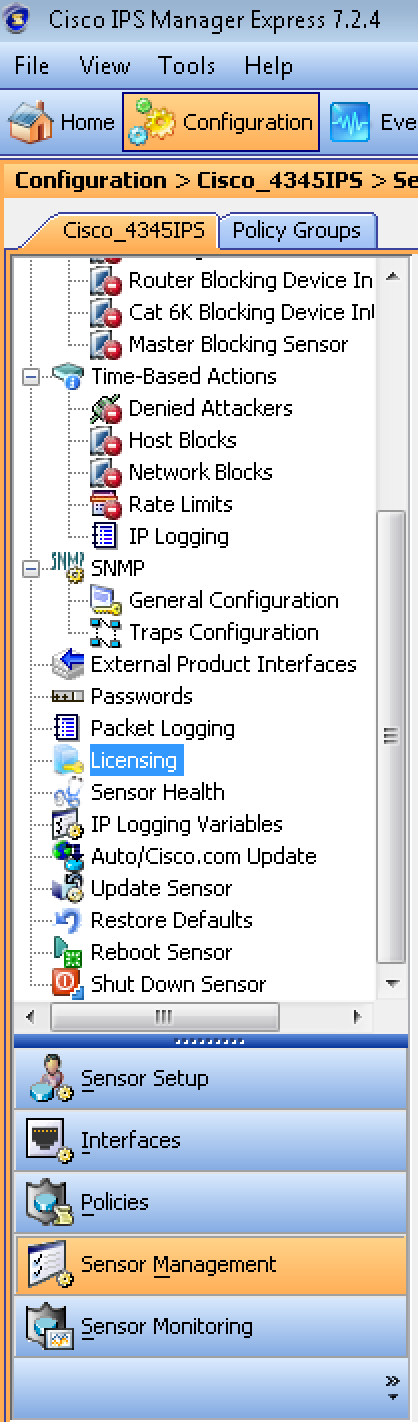
You will need to license your 4345 IPS appliance. Licensing can be found under Configuration, selecting the Sensor Management on the left column and clicking the Licensing icon. You should have received download instructions upon purchasing your 4345 IPS.
Adding a licenses to the Cisco 4345 IPS
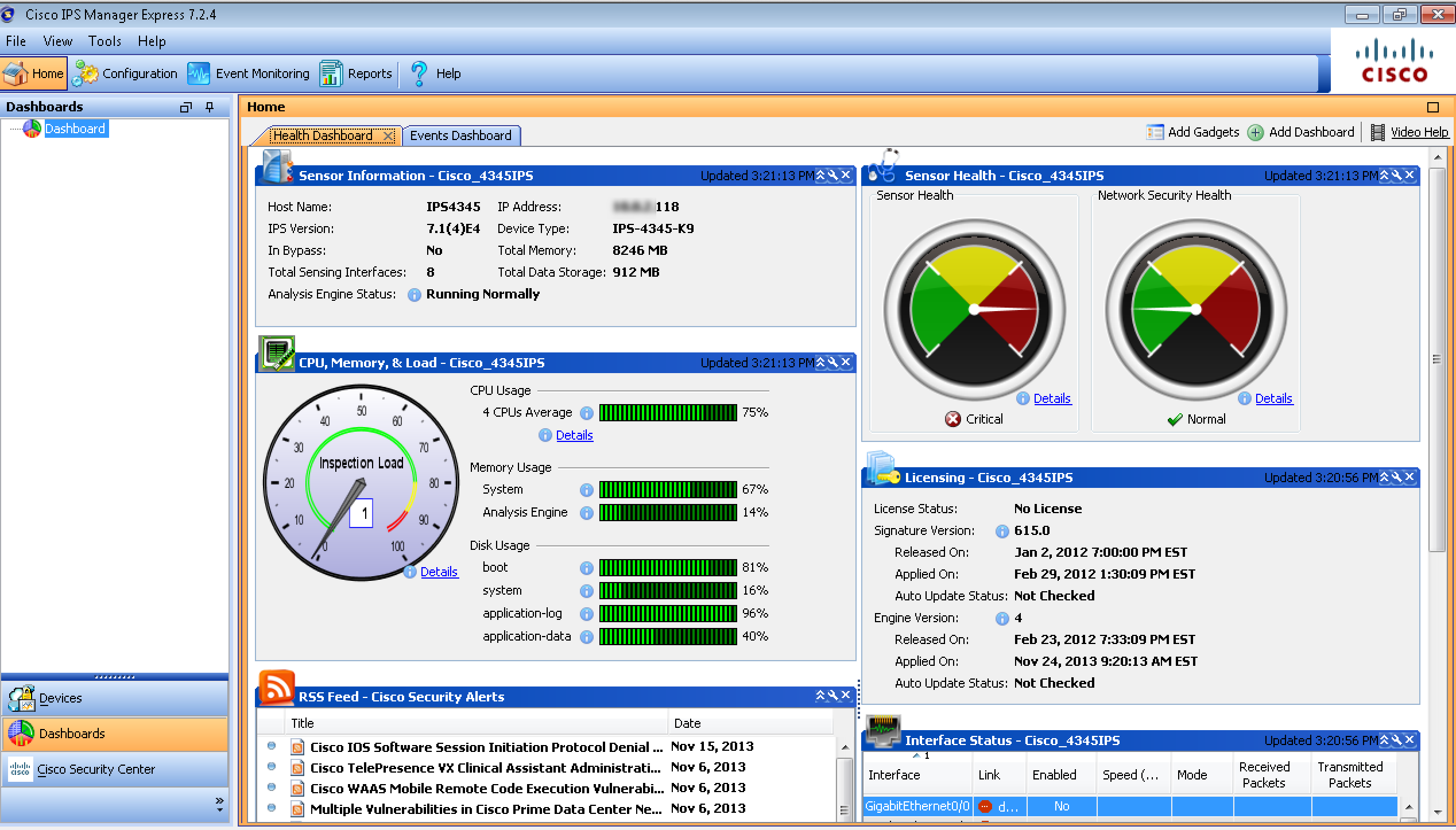
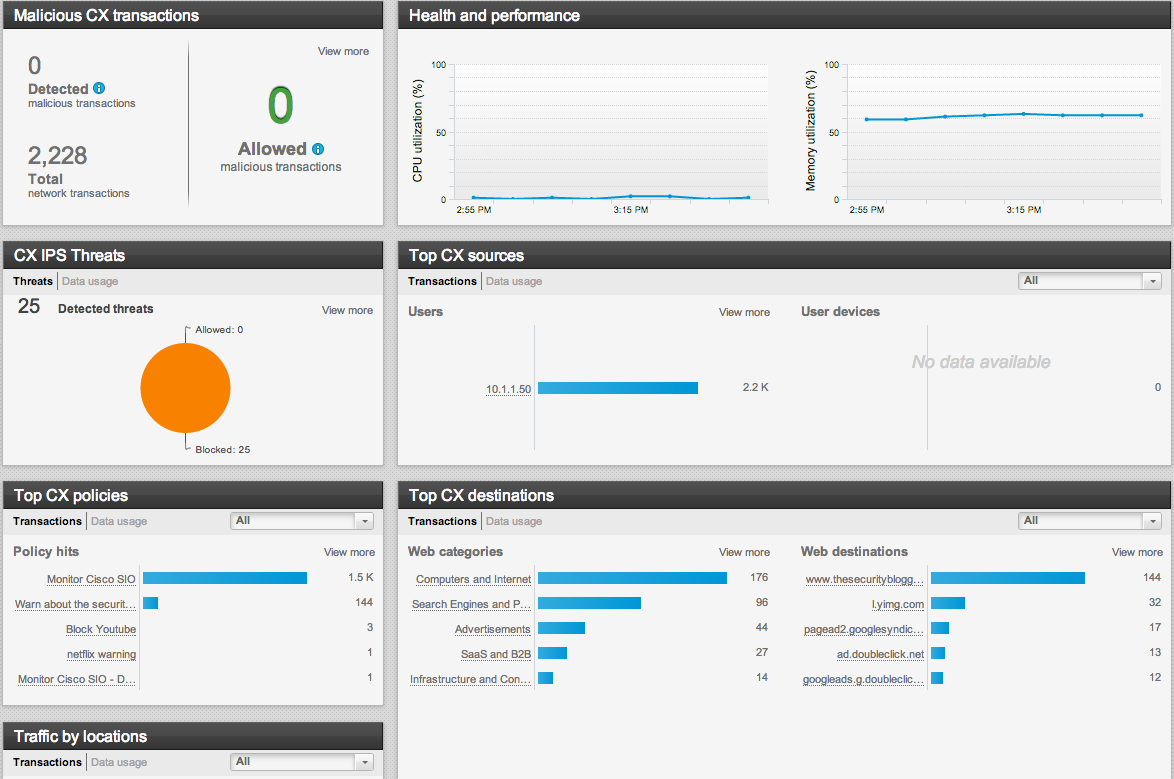
Once licensed and configured, you can view threats under Event Monitoring and adjusting the timeframe to view realtime or recent alerts. The 4345 IPS main dashboard should also start displaying traffic based on the widgets that are selected to display. Widgets are added to the main dashboard by clicking the Add Gadgets button on the top right corner. I’ll write another post focusing on tuning a cisco IPS in the near future covering these and other details.
Cisco 4345 IPS main dashboard