
Wireless Network Security is important. Wireless networks are the way of the future. People don’t want to run cables through their homes and mobile devices are becoming common tools for surfing the Internet. If you live in a populated area, you will find many wireless SSIDs broadcasted. How secure is your wireless network? How much should you spend on a wireless router? Can you get by with a basic password or should you utilize Wireless Network Security features? Here is my answer.
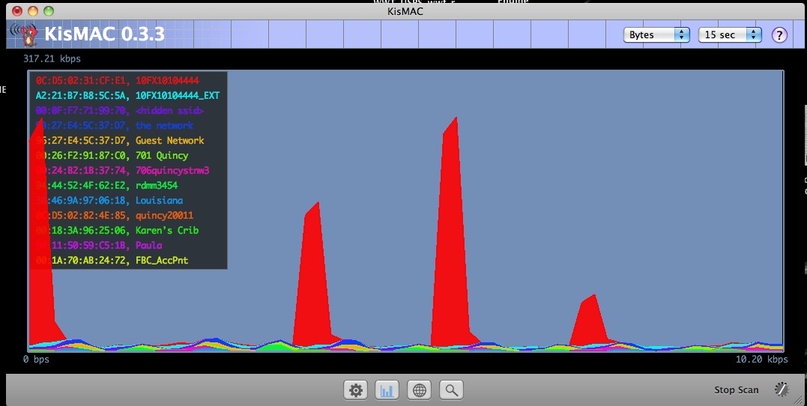
The first Wireless Network Security feature many people believe is important is not broadcasting the service set identifier or SSID. Regarding security, this is equivalent to putting up a four-foot high wood fence to keep burglars out. The fence may stop dogs or children but the average person can step right over it. Anybody looking to access your wireless network can scan for networks regardless if the SSID is advertised. Here is a scan from KisMAC showing all networks regardless if the SSID is broadcasted.
The next important Wireless Network Security concept is passwords. The majority of the population today understands it’s important to add a password, which is good considering it took enough hacker movies and scary credit card stories to make it happen. What the average wireless administrator doesn’t understand is using a weak password is like locking the front door. See my post on how secure that is How The Bad guys Break In.
Make sure your wireless security passwords use at least 10 characters that include numbers, special characters, and mix of capital and lowercase letters. Don’t get lazy with your password thinking other security features will protect you. See my post about how computer speed is making brute force methods easier regardless of what type of encryption you use Passwords Are Doomed. Also make sure to create a new administrator name and delete the “admin” account. This will make hackers have to compromise both user name and password before accessing your network.
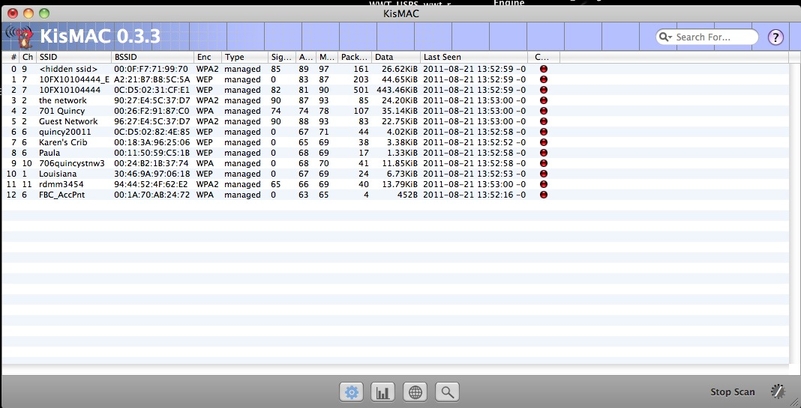
The next Wireless Network Security concept is encryption. The default encryption for many low-end wireless routers is WEP, which is a WEAK algorithm. Password cracker programs such as John the Ripper or Aircrack-ptw can break WEP in under a minute. If you look at the screenshot below, you will notice the majority of the networks are secured by WEP. This will only keep the honest people out. Most routers offer WPA2, which will dramatically increase your defense against wireless hackers.
Another security concept is not using wireless or locking down device access to your wireless network. I find many people use wireless to add one desktop in another room. Consider using your power grid utilizing solutions like the Linksys power line adapter. Basically you plug two hubs in the wall and they transfer traffic over the power lines. Some solutions include encryption. I use it for my desktops and swear by it. If you need to go wireless, you can lock down the MAC address of all approved devices and blacklist everything else. This will increase the work to add new devices but is more secure than having an open wireless network.
One final tip for purchasing wireless routers is not spending money on bogus features. I’ve seen some routers offer a built in Intrusion Detection / Prevention (IDS/IPS) component however the routers I tested with this feature were garbage. I would click “update signatures” and it would display “updated and secure”. Static signatures are worthless and home use routers never offer a way to test it. Other features I’ve seen are built in Anti-Virus and Content Filters, which are also worthless. Invest in a solid host based Anti-virus / IPS solution for your endpoints and consider content filtering applications such as netnanny if you are concerned about children surfing to inappropriate websites. Focus your router as being a wireless provider and capitalize on its wireless network security features. Don’t get lazy or you will eventually be owned.


Nice piece of writing. You should mention the new WPS vulnerability.