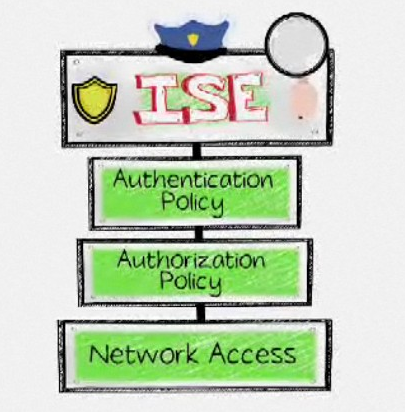
There is a lot of interest in enabling 802.1x for access control. Certificate based security is an industry standard and mandated by many federal agencies. Cisco’s first 802.1x based access control solution started with ACS and currently is enforced by their flagship access control solution Identity Services Engine ISE .
We have heard some administrators heard 802.1x is almost impossible to enable and something they don’t have the staff to maintain. The truth is 802.1x is like most technologies, which requires a basic understanding of core concepts and must be designed correctly in order for a project to be successful. Here are some concepts to take into considering while looking at Cisco or other 802.1x solutions for your network.
1) MONITOR ONLY – 802.1x can be deployed in a Monitor Only mode meaning you can turn it on and not impact the network. This is huge because it dramatically reduces the risk of 802.1x deployment issues by troubleshooting error messages before going live. Unlike many technologies, you don’t have to “cut over and troubleshoot”.
2) PROFILING – Cisco ISE offers network profiling, which has two key benefits. ISE can identify all devices on the network so you can plan for how access control can be handled for device types prior to enforcement. ISE can also maintain monitoring of those devices meaning if a hacker spoofs a printer, the spoofed IP will act differently on the network and be blocked. This is a more secure option than white listing devices. Best practice is planning device security via VLANs, ACLs, etc. prior to moving from 802.1x monitor mode.
3) SUPPLICANT – 802.1X authentication involves three parties: a supplicant, an authenticator, and an authentication server. The authenticator acts like a security guard while the supplicant (example laptop) is not permitted access through the authenticator to the protected side of the network until the supplicant’s identity has been validated and authorized. The supplicant provides credentials, such as user name, password or digital certificate, to the authenticator, and the authenticator forwards the credentials to the authentication server for verification. The most common used supplicants are built into windows operating systems meaning you don’t have to distribute any new software or clients. Some devices don’t support 802.1x which best practice is using a combination of MAC address and profiling to provision and maintain credibility of those devices.
4) SYSTEM MANAGEMENT – A common question is “how many people does it take to maintain a Access Control solution such as 802.1x?”. The answer varies on the size, level of desired security and other factors. Regardless, the goal of an Access Control solution is to automate and enforce existing security infrastructure. For example, port security is a form of access control that typically requires manual efforts to maintain. Access Control solutions should reduce the required management hours by automating user and device access. The same concept goes for troubleshooting and locating rouge devices.
5) CONFIGURATION – 802.1x is an industry standard and uses switch level commands. Best practice is to build a template in a network management tool and push out the 802.1x Access Control configurations to switches to reduce the chance of misconfiguration.
Here is a line-by-line example of configuring a switch for monitor only 802.1x
//Enable =AAA, Enable Port-based authentication, VLAN/ACL and 802.1x / MAB
Switch(config)# aaa new-model
Switch(config)# aaa authentication dot1x default group radius
Switch(config)# aaa authorization network default group radius
Switch(config)# aaa accounting dot1x default start-stop group radius
//Specify the IP and Ports of RADIUS server, pre-shared key, attributes, and RADIUS request source interface
Switch(config)# radius-server host ise-1.demo.local auth-port 1812 acct-port 1813
Switch(config)# radius-server key thesecurityblogger
Switch(config)# radius-server attribute 6 on-for-login-auth
Switch(config)# radius-server attribute 8 include-in-access-req
Switch(config)# radius-server attribute 25 access-request include
Switch(config)# radius-server dead-criteria time 5 tries 3
Switch(config)# ip radius source-interface g0/24
//Test 802.1x
switch#test aaa group radius usertest password new-code
Switch(config)# dot1x system-auth-control
//port level commands
Switch(config)# interface range g0/1-3, g0/5
Switch(config-if-range)# switchport mode access
Switch(config-if-range)# authentication port-control auto
Switch(config-if-range)# dot1x pae authenticator
Switch(config-if-range)# mab
//ISE monitor only mode config.
Switch(config-if-range)# authentication open
Switch(config-if-range)# authentication host-mode multi-auth
Switch(config-if-range)# switchport access vlan 10
switch(config-if-range)# authentication order mab dot1x
switch(config-if-range)# authentication priority dot1x mab
Hopefully this helps with the confusion around considering 802.1x and Cisco ISE.



Hi,
If I dont ever want to 802.1x – Will ISE work for me?
Do I need 802.1x with ISE – I only ever seem to see the two in references. Working with ISE what do I lose if I dont want to use .1x or MAB? can I still implement NAC and prevent devices joining my network and threatening my data centre? Someone at Cisco told me that without .1x I cannot use ISE and I would need to use their old NAC Appliance…
All the best,
Sam
Hi Sam,
Great question. Today ISE uses 802.1x, MAB or redirection for guest users. The older NAC appliance users secure SNMP to talk to switches or in-band / layer 3 that acts like a bump in the wire. Eventually ISE will include the NAC appliance approach which will cause NAC appliance to go end of sale. We see a few use cases for NAC appliance however most people are going 802.1x Its a industry standard, being called out in many mandates (older government stigs use to say automated access control but now ask for 802.1x), and exists in many switches. The only switches we see this being a issue is brocade that doesn’t support 802.1x COA. Same goes for wireless (IE cisco, aruba, etc all support 802.1x).
Hope this helps
Joey
Joey,
Thanks for your reply but I am old and still not completely sure of the answers to my specific questions…8-)
1. If an organisation just will not ever implement 802.1x does this mean that ISE cannot be deployed effectively?
2. If I deploy monitor mode (Audit mode according to Cisco documentation) can I leave things indefinately like this – say have 250,000 devices operating in this way? Does ISE work just as effectively – are there any concerns around this?
3. If ISE is in monitor mode and there is no 802.1x is this a default state for the switches or do I actually have to configure monitor mode on each switch?
4. If in Monitor mode can I still prevent or control access to my network environment effectively – do I lose something or create an overhead elsewhere?
I am in a discussion about whether ISE requires 802.1x or not? If so then there is an associated project of work that needs to be done. I spoke to a Cisco man and he said that yes 802.1x is required to implement NAC with ISE. However, other people are kicking back and telling me that you don’t need it (you can use monitor mode). I am just trying to find the answer and the implications of Monitor mode.
All, and I mean all, the Cisco documentation on ISE assumes the customer is moving towards an 802.1x environment (either Low impact mode or closed mode) but what about those who cannot foresee the time when they have 802.1x? Even Low impact mode documentation states that by this stage most devices are using MAB or 802.1x.
Any insight you can give me is extremely helpful,
All the best,
Sam
Hi Sam,
1) ISE best practice is using 802.1x. If you don’t want to go that route, what are you considering? Pure in-band (IE layer 3 / pointing all devices to a specific choke point)? Using another means to put people into the trusted network such as SNMP? Are you looking at a host based method such as microsoft NAP? Are you looking at certificate or MAB only? Please elaborate on what you are trying to accomplish. Most likely ISE will be best for a 802.1x deployment however there are other use cases.
2) We have many very large customers who are using ISE in monitor only mode for the first year before considering access control. The idea is they can get data on what is on the network and start to develop polices. Its a good idea to go this route if you don’t know what policies make sense for your organization. Knowing what is on the network is just as important as deny devices. The only concern is you may see threats on the network however with monitor only mode, you are permitting them on regardless. You could built a blacklist policy and manually kick off devices that are high risk however best practice is to automate that with ACLs, VLANS or STGs.
3) ISE requires some global and interface level configurations to enable specific profiling probes as well as 802.1x. For example, you need to tell the switch globally where to send the radius data (IE the IP of the ISE server). ISE also can pull some information by sitting on the wire as well. For example, I had ISE on a MACMINI running ESXI 5. I plugged it into my home network switch with no ISE config and it identified my printer, the MACMINI, the virtual servers running, iPAD and laptop. See my profiling focused post. The more you give ISE, the better it profiles meaning you may need to add a DHCP helper address or point radius information to get the most value. Another example is if you don’t enable netflow, you won’t get any value out of that probe. Anything access control related will require some radius commands (AKA testing in open mode people passing and failing authentication and authorization)
4) To prevent access, you will need either 802.1x, MAB or guest redirection. Monitor only mode doesn’t prevent or control access … it just monitors / profiles who is on the network and handles 802.1x for access control however doesn’t enforce anything (IE places all devices that pass and fail in the same network segment). If you are looking to just monitor, you can get away with ISE not using 802.1x however it will be more of a profiling tool rather than access control technology. If you want to start viewing who is attempting to access your network, monitor what would happen if somebody passes / fails police, control different device type access levels, etc … you will need to start looking at either 802.1x, MAB or guest redirection.
Hope this helps
Joey
Joey,
Many thanks for your thoughts thus far. I have some further questions…sorry.
1. If I am not using .1x for access control and I am running ISE/TrustSec can just use ACLs and prevent access that way – achieving the same result?
In the ISE documentation it suggests that user/device control is achieved in 2 parts:
Authentication and Authorisation. If I dont bother with Authentication can I still block unexpected/unwanted user/devices with Authorization policies?
I am trying to gauge whether 802.1x is a pre-requisite for ISE, or is this something that is purely optional. As I said in my last post all the Cisco documentation mentions 802.1x and a Cisco member of staff explained that I needed it if I was using ISE. Now I am trying toi understand whether as part of an ISE/TrustSec delivery I need to develop and fund an 802.1x delivery plan (with all the associated negotiations around authentication types etc within the organisation).
2. You mentioned NETFLOW with regards to profiling – are you saying that the ISE Policy Definition Point sits at the centre of the infrastructure and receives NETFLOW from all the switches and carries out device assessment. What are the switch templates for that I have read about?
All your comments are greatly appreciated,
All the best,
Sam