Last year Aamir Lakhani and Joseph Muniz developed a fake identity known as Emily Williams with the purpose of compromising a specific target using social media. We created Emily Williams based on research from Robin Sage, which showcased how a fake identity could obtain sensitive information from social media resources. We wondered if a similar approach could be used for targeted attacks and developed Emily Williams for that purpose. More information on developing Emily Williams via Part 1 of this project can be found HERE.
Emily Williams and Robin Sage
This Part 2 post explains WHY the Emily Williams project is important to understand. Yes, it was humorous watching people endorse a fake person’s technical abilities and receive job offers based on a posted IT background (or possibly just because Emily is attractive) however those are not the worst outcomes from social media threats. Part 1 concluded with our lovely Emily Williams having friends with multiple parties from our target such as Human Resources, IT Support, Engineering and Executive Leadership. People were sharing information and considering Emily Williams an employee based on the profile we created. The information alone was very valuable however that was just the beginning.
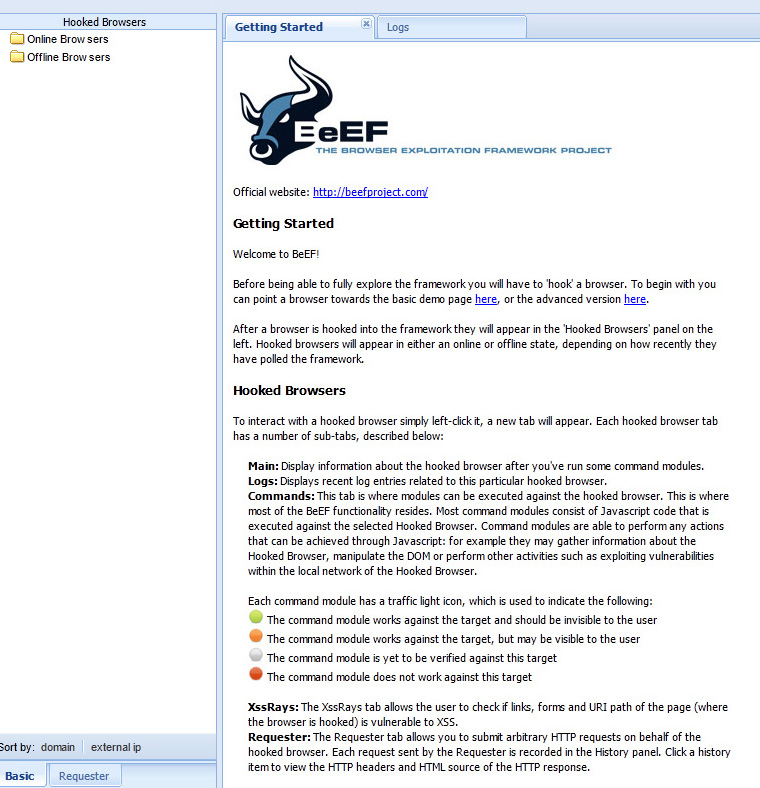
Stage 3 focused on obtaining access to host systems through social media. There are many options to do this such as the very popular Blackhole exploit kit however we did not want to use any method that could potentially harm our target’s system based on personal ethics. Blackhole is the most prevalent web threat seen today leveraging a malicious payload that we felt wasn’t safe for our target’s systems. We chose to use The Browser Exploitation Framework (BeEF) based on our feeling that compromising browsers was not as evil as using malware.
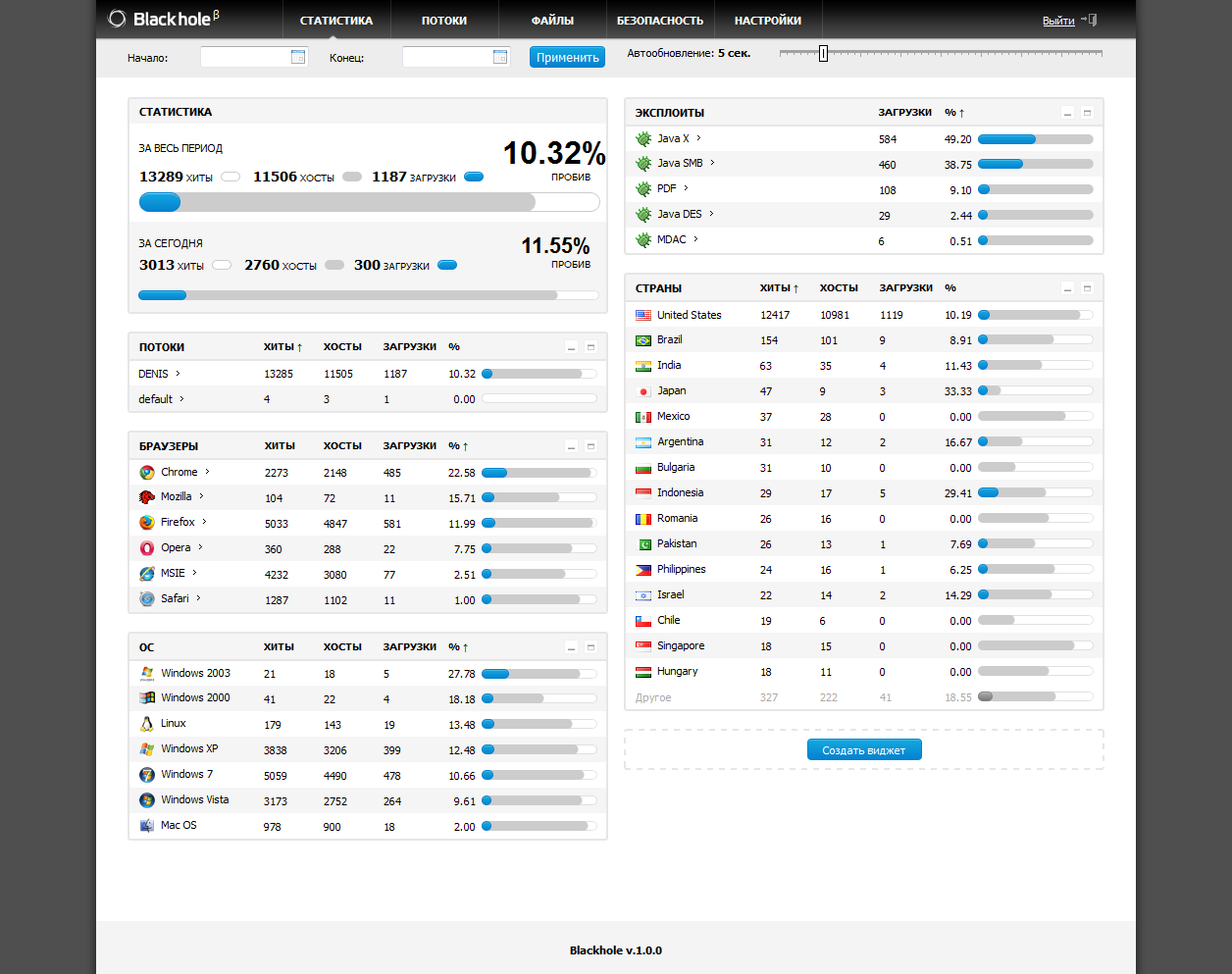 Blackhole Exploit Kit Screenshot
Blackhole Exploit Kit Screenshot
Browser Exploitation Framework (BeEF) Screenshot
BeEF leverages browser vulnerabilities to assess the security posture of a target. BeEF “hooks” targets as beachheads for launching direct command modules. Different browsers have various vulnerabilities, which means the more vulnerable a browser is, the more unique attack vectors become available to the hacker. We installed Backtrack 5R3 on a server and developed a BeEF hooking server that was public facing. We tested systems by accessing our BeEF server, hooking systems and launched commands such as taking a screen shot capture. More on building a BeEF system can be found HERE.
The next step was luring employees of the target to our BeEF system. There are many methods hackers accomplish this such as offering free media sites (IE download music, movies, etc. … see more on why this is risky behavior HERE), phishing emails and fake URLs designed to look and feel like something else. We decided to post virtual holiday cards on Emily William’s social media pages and direct invites to specific targets. The goal was having a user click the holiday card, wait for the card to pop up and have our system probe the browser for vulnerabilities during the waiting period. Once we hooked the target, we would look for passwords and insider information to gain access to the target agency. We launched three campaigns targeting systems during Thanksgiving, Christmas and New Years. We were able to figure out domain credentials to create an inside email address for Emily Williams, VPN passwords to gain internal access and other methods to compromise our target.
Our research demonstrated a few points. First off, people are trusting and male dominated industries like IT are even more trusting of women. Second, social media can be used as a means to compromise targets if users are not educated on common attacks and proper use of public facing network resources. The risk extends beyond data leakage since many people that use social media also use the same systems for internal use while at work. Finally, we demonstrated how easy it is to carry out what many consider an advanced persistent threat (APT) meaning we chose our target and bypassed standard security technology. We believe our methods were not very sophisticated compared to the real threats that target people using today’s public Internet yet we were very successful with our goal of compromising a specific target. Security is an extremely important investment and needs to include education around proper use of social media (more on this HERE) as well as protection from insider threats.
I hate to drop a plug however I recently took a job at Lancope based on their technologies’ ability to detect insider threats.



We have so many computers come into our shop, with viruses & spyware, by users being silly and clicking on things that they shouldn’t, i guess i shouldn’t complain as their stupidity keeps me in business eh?