There are many SIEM solutions available however I was extremely impressed with recent innovations from Splunk regarding a free Application that can be used to centralize security data from multiple cisco solutions. By definition, a security information and event monitoring system aka SIEM is typically just that; either a good information sorting tool or solution that helps identify and react to events.
One of Splunk’s key market differentiators is their extensive application library developed by customers and Splunk engineering. These applications turn the traditional SIEM into a business enabler to meet specific use cases. Splunk has developed cisco applications in the past however recently face-lifted the cisco Security Application to include Cisco access control (ISE), email security (ESA), web security (WSA), Cisco firewalls, and even SourceFire (both network and only SIEM as of today to support malware aka AMP). This application can link findings with other vendor data such as taking ISE context (IE Joey’s windows 7 laptop on port 1/0/14) and matching it to any captured log by Splunk (For example a McAfee IPS event). This provides a true centralized view of data across a network.
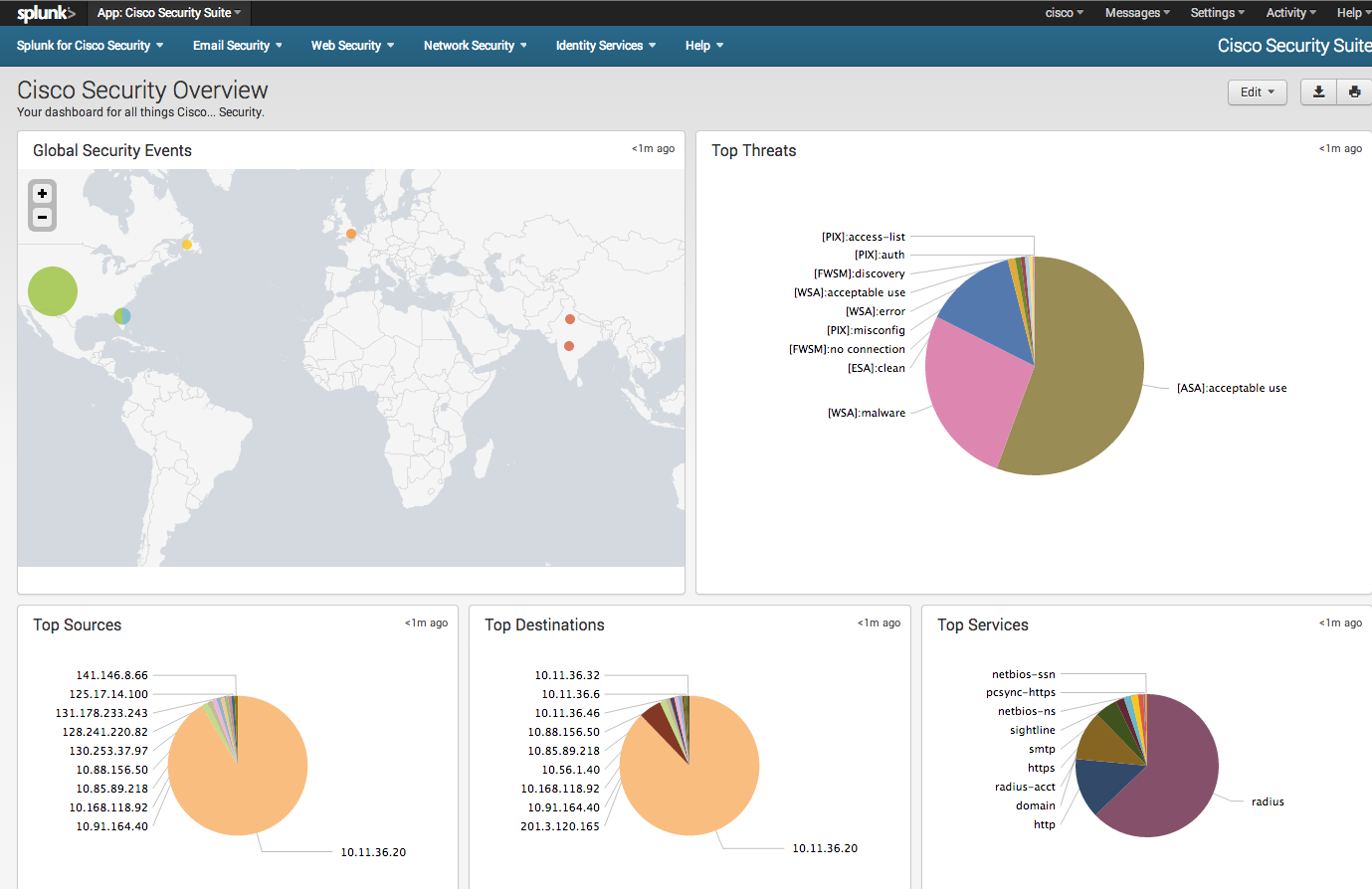
Main dashboard for Cisco Security Application
The screenshot above shows the main dashboards for multiple Cisco security products. The map shows where logs are coming from, which can be clicked to zoom in as shown below. All the event dashboards can also be clicked to dive deeper into the findings.
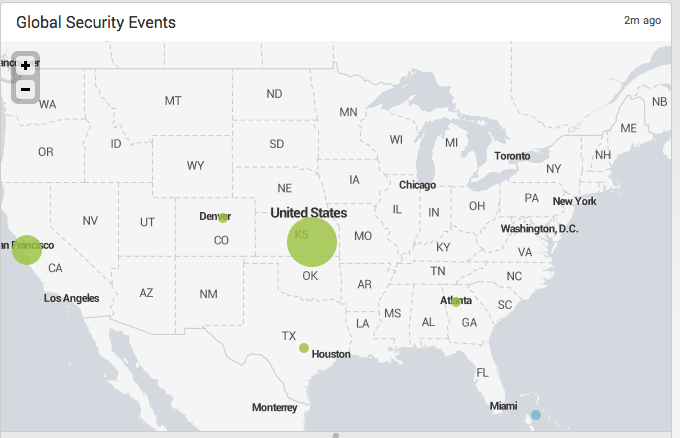
Zooming into events via the MAP
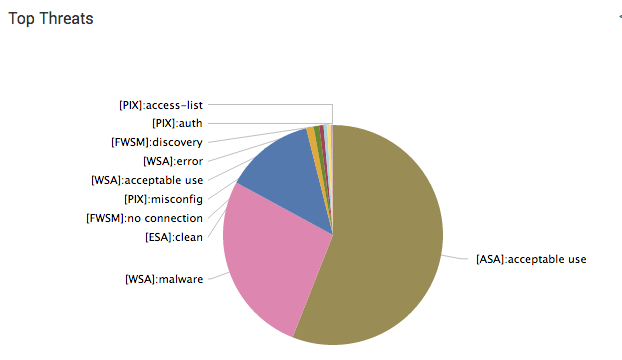
The Top Threats window shows various threats across multiple products such as Malware found by Cisco WSA to general firewall events seen in a Cisco ASA. If an administrator wants to dive into a particular Cisco product, there are tabs at the top for each individual solution. The next few screenshots show a few dedicated Cisco product dashboards that can be launched from the main dashboard.
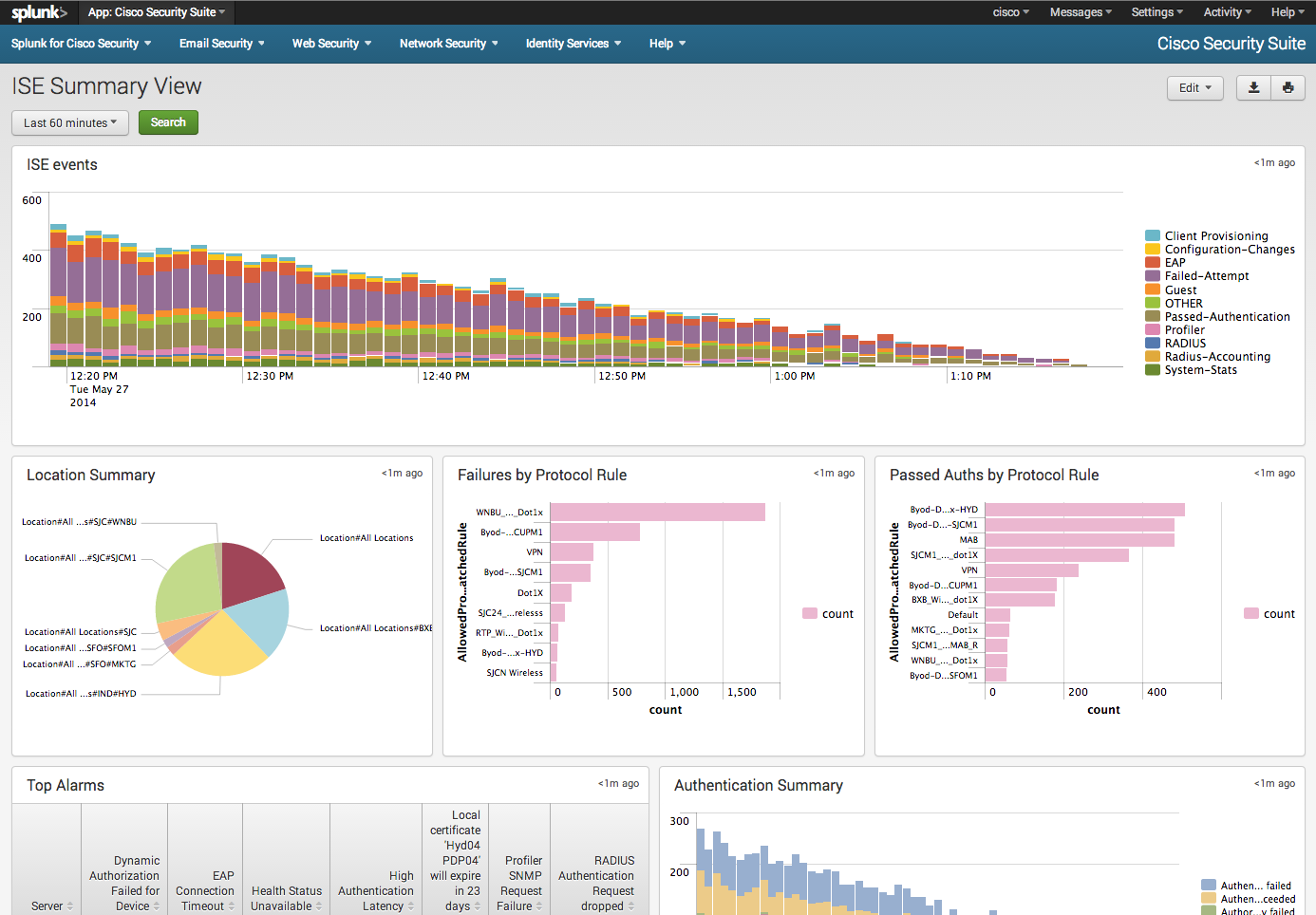
Identity Services Engine ISE dashboard
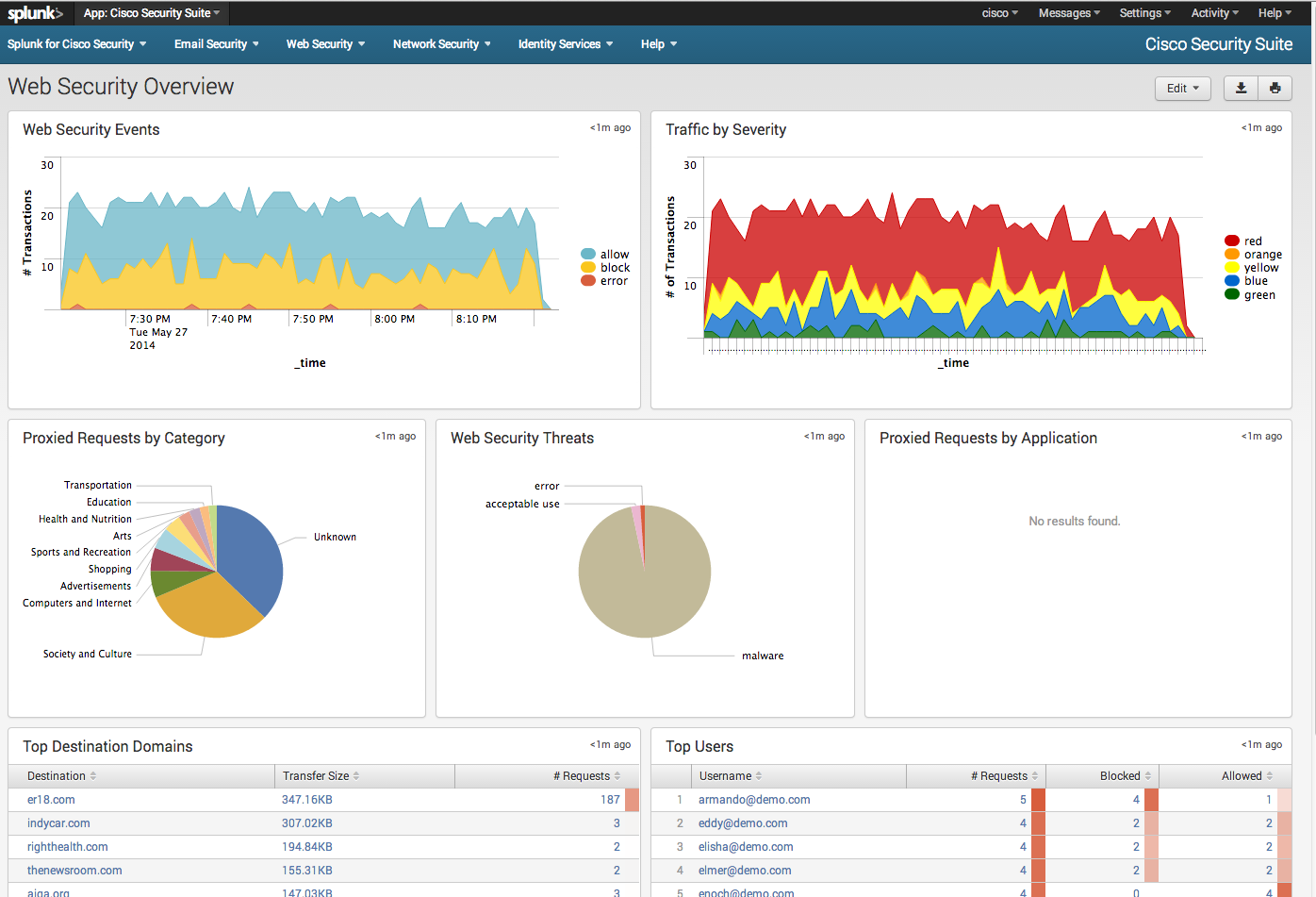
Web Security Appliance WSA Dashboard
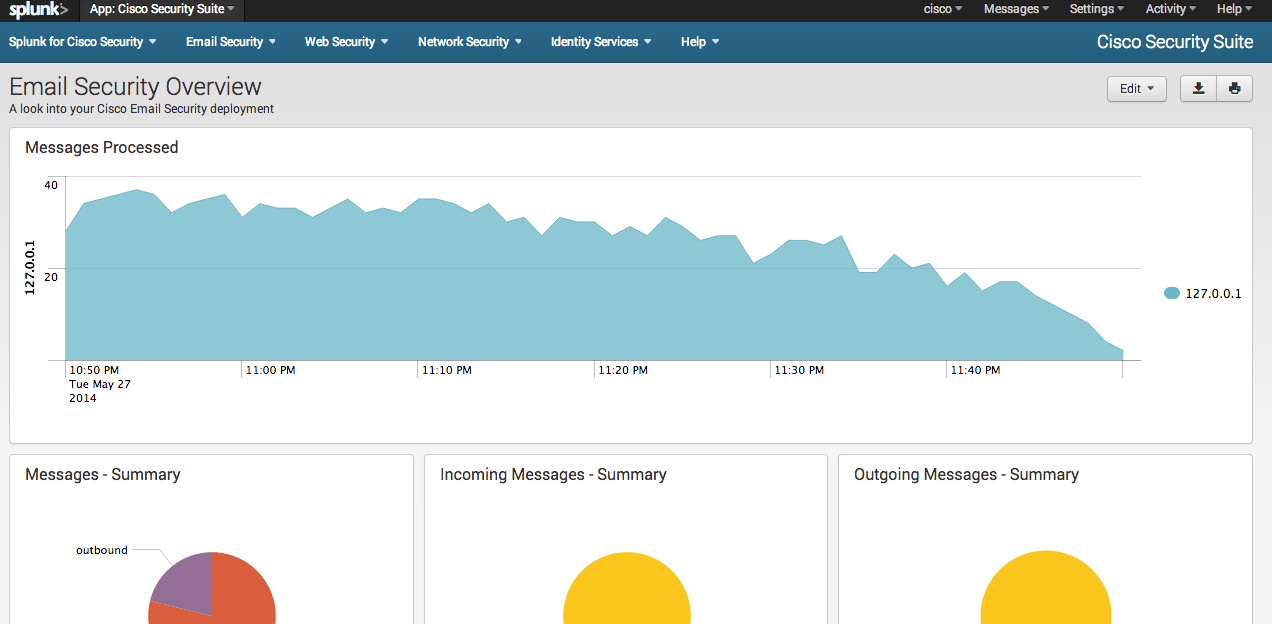
Email Security Appliance ESA Dashboard
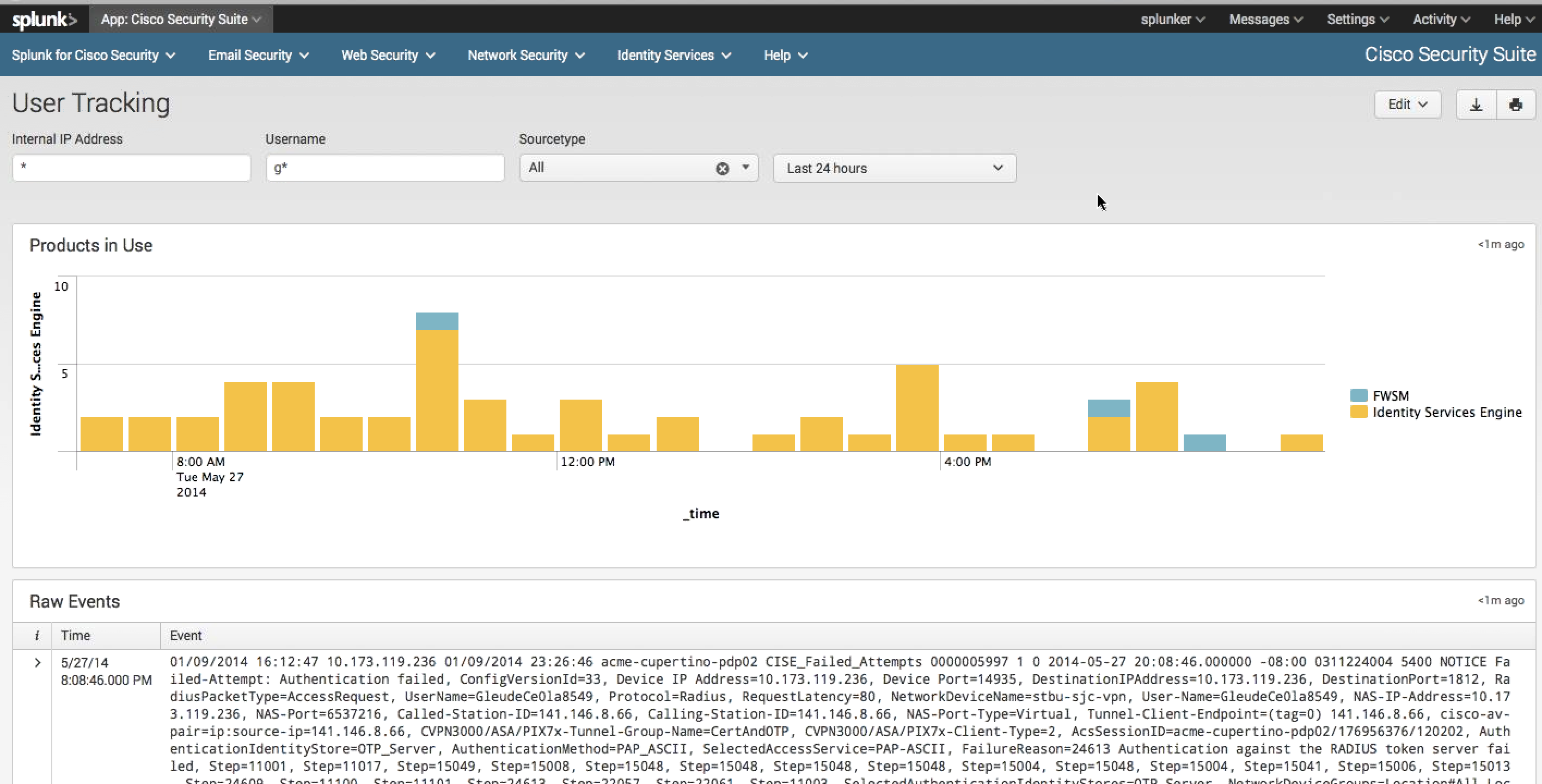
There are also dashboards delivering information typically not found by Cisco tools such as a HOST or IP address looking used to identify people or devices across multiple products. The next screenshot shows a query for any user with a name starting with G across all cisco products. The results show both the Cisco Firewall and ISE solution hits including raw log data under the graphic view.
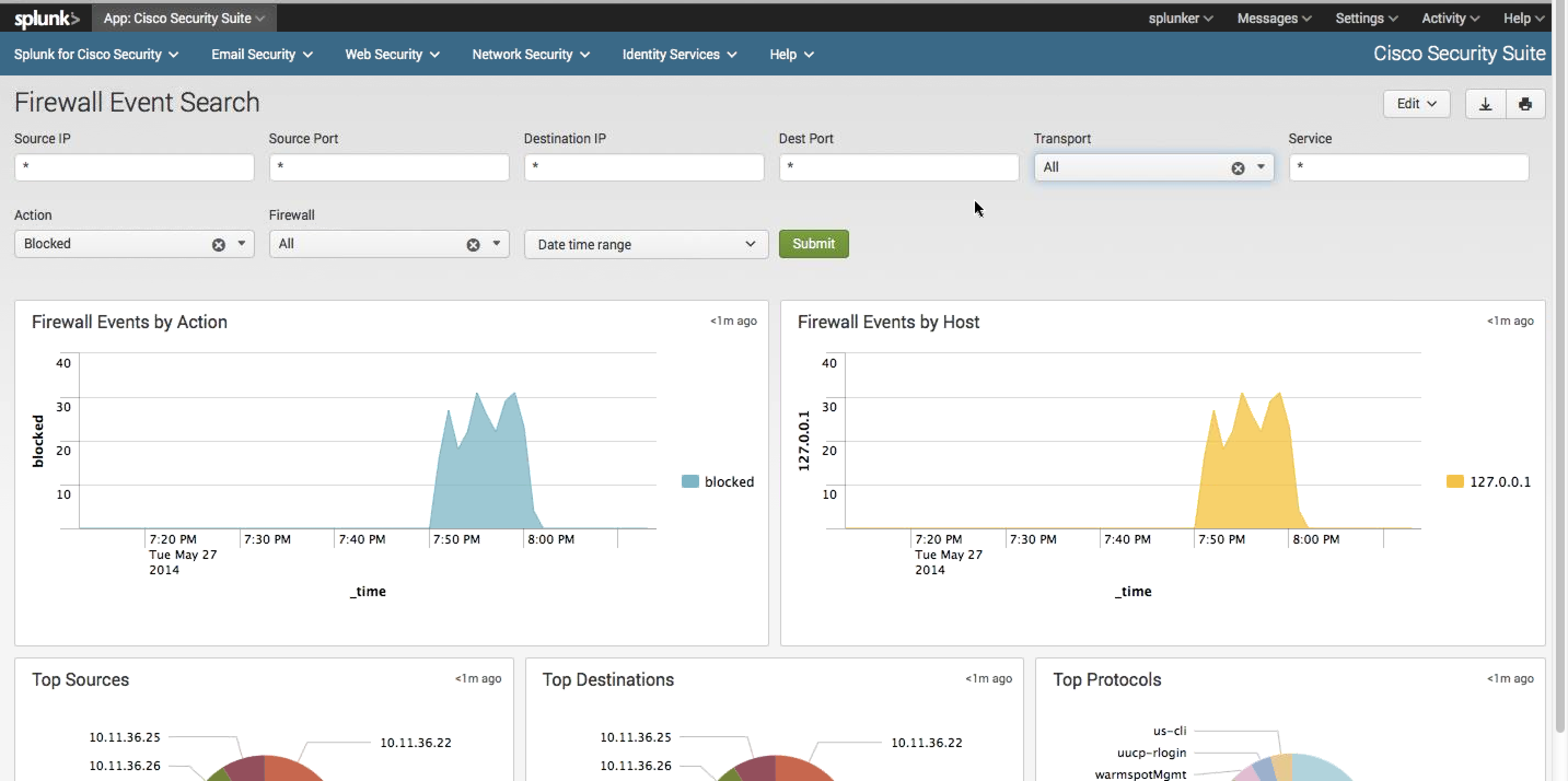
Another example is searching across all firewalls (modules, appliances, etc.) for specific information, which is a event search page within the Firewall dashboard.
This is all cool but the real potential is having dashboards that leverage Cisco and non-Cisco data. Applications in Splunk are a frontend for a series of searches meaning you can search for ANYTHING and develop a dashboard similar to the Cisco ones shown in this post. Applications can be customized so administrators can download the new Cisco Security Application and add other dashboards creating a true customized situational awareness reporting engine.
The next screenshots show top threats from multiple security devices however this could include host anti-virus, NetFlow data such as output from Lancope and so on. All you need to do is search for it in Splunk and tune the dashboard to showcase the desired information. So for example, searching for any hosts named Joey (active directory), running windows 7 (ISE posture or application aware firewall), accessing Facebook (content filter or application layer firewall), with corporate issued Anti-Virus (host security) can be a dashboard regardless of the vendors involved. Pretty powerful stuff
Top threats across multiple Cisco solutions
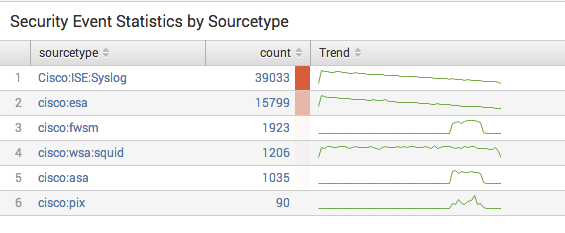
Events Statistics across multiple Cisco Products




I´m having a hard time trying to integrate ASA CX managed by Cisco Prime Security Manager (a VM) with Splunk.
Seems that only WSA are supported and Cisco SEs says that Syslog is only at Roadmap for CX module.
Cisco Website says that ASA CX managed by Cisco PRSM does not support Syslog.
At PRSM WebGui there´s only a download ZIP file but it´s for TAC diagnosis propose only.
Hi Antonio. Yep the syslog is suppose to come in a upcoming release. Splunk also just updated their app to cover ISE, ASA as a firewall, SourceFire, WSA, ESA and others. Expect to see the upcoming releases to have more integration with SIEMs such as Splunk as well as announcements around rest APIs.
Any word on support for REST APIs in Cisco WSA?
they are coming with the next release of ESA (email security) but not sure of the date for WSA as of now