One common question I’ve received is what open source tools are available that I can download now. The answer to this question is simple: LOTS! I will point out however, there are reasons why organizations don’t just run only open-source products within their security operation center. There are costs and benefits to open source, which I’ll address this this post. I’m also asked if opensource is better or not than certain tools, which my reply is “it depends on what you are looking to accomplish”. I believe there are some misunderstanding regarding open-source tools in the security community and I aim to address those now in this post.
In this post, I’ll address the cost and benefits of using open-source tools as well as provide recommendations for various types of open-source tools. I’ll first start off with explaining when it does and does not make sense to use open source or free tools
Cost / Benefit of Open Source
When a program is labeled as open source, that means the program’s source code is openly published for use and modification free of charge. When you purchase a program, the code that was used is not published hence you can only modify what the creator permits as well as you don’t get to view how the program was created. This is a key point since this means you can’t debug the code or determine if there are certain types of security risk associated with non-open source tools. When software is open source, everybody has access and can beat up the code. When it’s not, you have to rely on the vendor to secure the code.
What are the benefits of having access to the code of the program you want to use?
These are the top benefits you could obtain.
- Community: Open source tools tend to have a thriving community meaning you can search for help and find various users or contributors willing to support you at no cost.
- More Ideas: Since more people are involved with full access to the code, talent from around the world can help innovate verse limiting innovation within a specific vendor.
- Full Transparency: Viewing the code means nothing is hidden. If a bug appears, you have access to everything and are not limited to only a user interface.
- Avoid vendor lock-in: Open source means there is no vendor. With open-source, the question becomes can other tools support the open source tool since open source is vendor neutral.
- Hardware and License Savings: Open source means you don’t have to buy anything outside of required components to support the open source tool. For example, you will need to acquire a system to run the open source tool but the tool itself will not have a cost.
In contrast, there are some concerns you need to have regarding taking on an open-source tool. Such concerns include the following
- Risk of compromise: Since anybody has access to the code, malicious parties can develop attacks if vulnerabilities are identified.
- Limited support: I mentioned that community is an advantage of open source however, a community is not required to support you. If you run into a mission critical problem, you do not have a number to call like you would if you had a support contract commonly included with enterprise tools. Open source tools will not have this option unless a 3rd party service provider is acquired to fill your support needs.
- Often not user friend: Enterprise tools have a cost and there is value that comes with that cost. The most common value is ease of use meaning offering a more simplified deployment and management process than a competitive open source option. This is not always the case however, I often find open source tools requiring much more work to install and maintain than enterprise options.
My thoughts on the pros and cons of open source are you should not use open source if you are not prepared to invest in the proper resources to use them. Enterprise tools are typically easier to use and come with better support. Open source tends to require more time in learning how to work with a open source platform, effort managing and supporting the tool and sometimes have hidden costs such as required components for the open source tool to function properly.
Open Source Security Tools
Next, let us move to focus of this post, which are what is available that is open source for you to use right now. There are tons of open source security tools you can access now to learn more about security concepts or deploy within your network. I’ll break each of my recommendations down by topic. Each recommendation will have more than one option available however, I’ll give at least one recommendation for each industry security capability.
Security Tool Distributions
There are operating systems that contain a ton of tools. Here are a few you can access now. I picked one for a different use case but know there are many alternative distributions for each use case as well. The following image is an example of Kali Linux’s tool categories to give you a feel of the breach of options available.
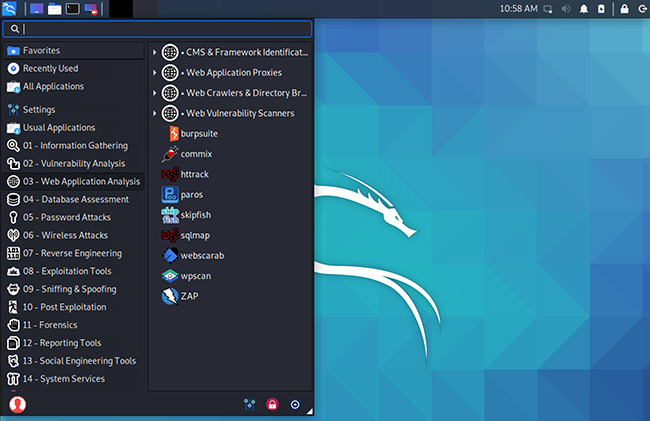
- Kali Linux – Penetration testing focus distribution with a boat load of security tools ranging from exploitation to digital forensics. If you have any interest in red team / penetration testing, you need to know about Kali Linux. https://www.kali.org/ (Links to an external site.)
- Security Onion 2 – Another fantastic distribution that is focused on defense. Tools are designed for threat hunting, enterprise security monitoring and log management. https://securityonionsolutions.com/software (Links to an external site.)
- DFF (Digital Forensics Framework – For those with a need for digital forensics, DFF comes packed with dozens of tools to help with your investigation. There are tools for disk duplication, dumping memory, enabling write block and managing your investigation process.
Breach Detection
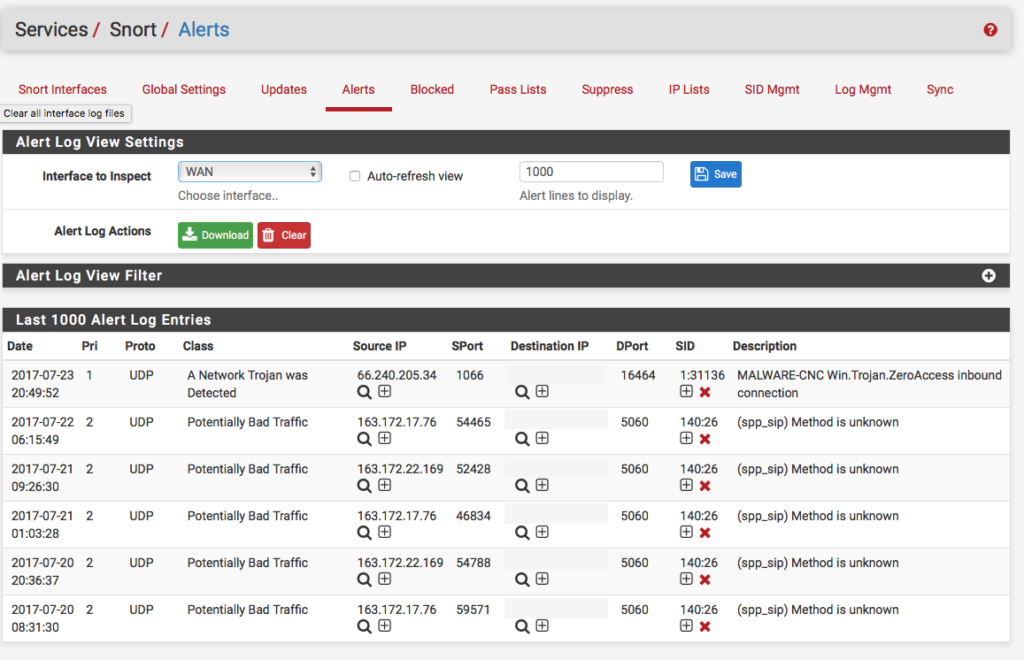
If you have a need to detect if your network has been compromised, you will be looking for something that can detect malicious behavior such as a honeypot, IDS or packet capture tool. These are some tools that can help. The following image is the Snort dashboard.
- Honeypots – There are so many free options to name. Maybe you want to simulate a vulnerable Windows Laptop? Maybe you want to simulate a vulnerable IoT device? Smokescreen listed a ton of options here https://www.smokescreen.io/practical-honeypots-a-list-of-open-source-deception-tools-that-detect-threats-for-free/ (Links to an external site.)
- Intrusion Detection – Two very popular opens are Zeek (formerly bro) and Snort. Both offer the abilty to create customized rules or download rules from different sources. Traffic must find its way to the IDS for it to be able to evaluate traffic hence multiple IDS will likely be needed to cover a network. https://zeek.org/ (Links to an external site.) or https://www.snort.org/ (Links to an external site.)
- Packet Capture Tool – A third option to detect threats is analyzing traffic within the network using a packet capture tool. One of the most popular open source packet capture tools available is Wireshark. Pretty much every security distribution will have wireshark preinstalled. https://www.wireshark.org/
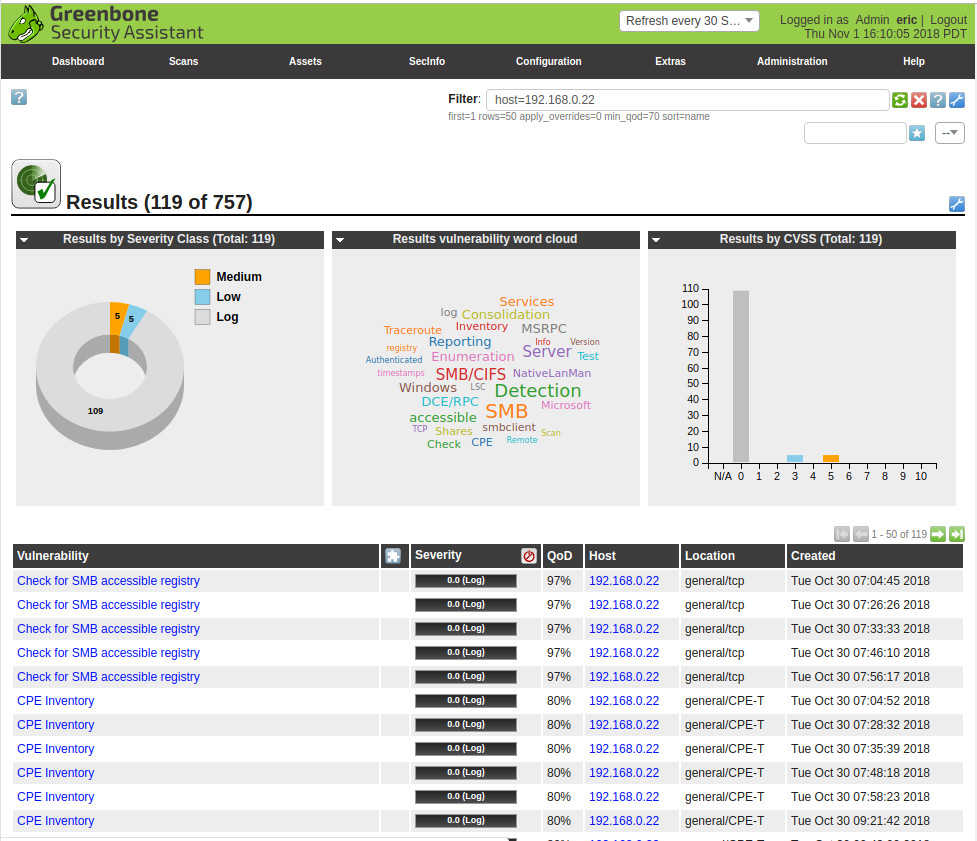
Vulnerability Scanning
Every organization needs a way to determine if there are vulnerabilities within its systems and services. OpenVAS is a free open source option you can use right now. It also comes installed in distributions such as Kali Linux. https://www.openvas.org/download.html.
Host Security
Everybody from the home network to enterprise will have end user systems using the network. This brings the need for security tools that can be installed to secure host systems. The following is a image from immunet.
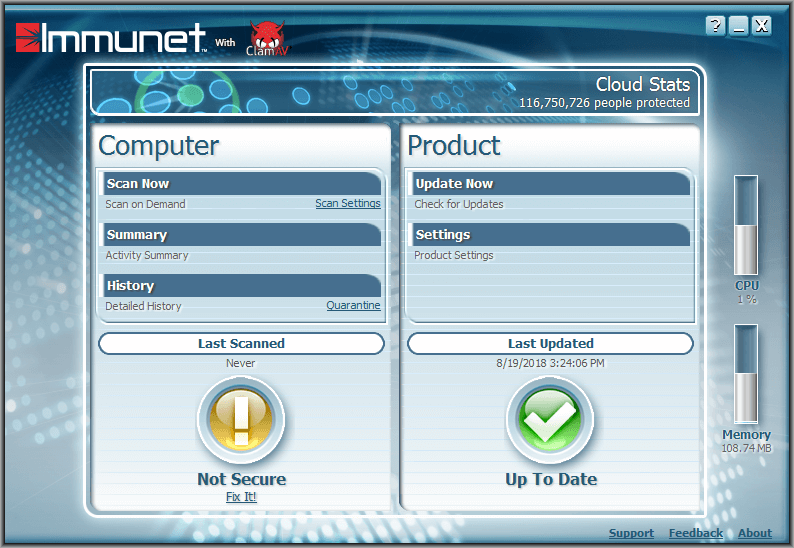
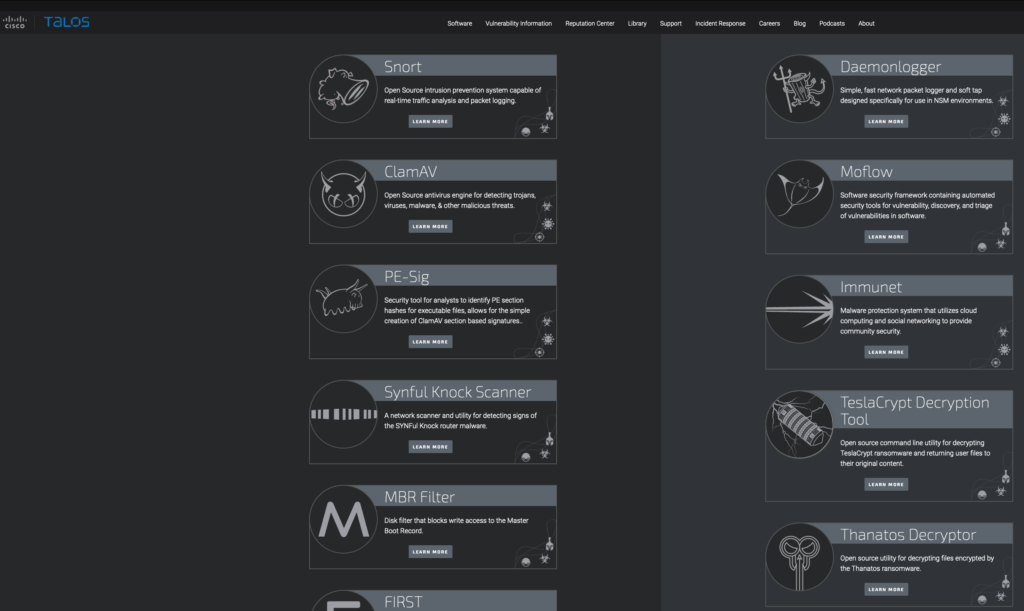
- Antivirus /Antimalware – Cisco Talos offers both free linux and windows antivirus/antimalware known as Immunet and ClamAV. These tools include both signature and behavior capabilities. Find them at https://talosintelligence.com/software (Links to an external site.)
- Disk Encryption – If you are concerned that somebody can take your device and recover data from it, you will want to deploy a disk encryption technology. VeraCrypt is an open source option found at VeraCrypt
- VPN – If you are concerned about parties snooping on your network communications, you will want to deploy a VPN to encrypt your host traffic. OpenVPN is an open source option that can serve this purpose. https://openvpn.net/ (Links to an external site.)
Centralized Identity and Data Management
A mature security operations center (SOC) will have a centralized place to collect data and enable orchestration when simple tasks can be automated. Also, concepts such as centralizing identity management are also part of the mix ensuring only the right people and systems gain access to resources.
- SIEM – A security information and event management (SIEM) tool is the common solution for centralizing security events and data. Elk / Elastic is one open source option you can use for this purpose. https://www.elastic.co/siem (Links to an external site.)
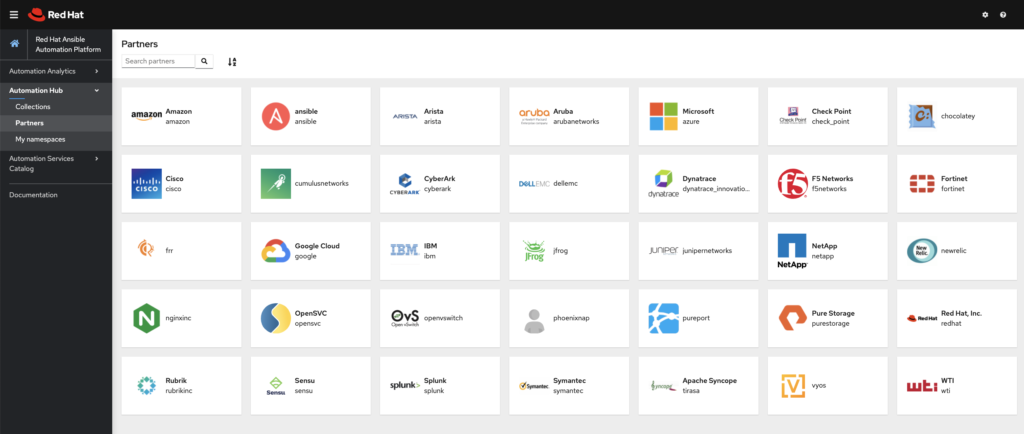
- SOAR – A traditional SIEM does not permit the SOC to take any action on events. This is why the security orchestration, automation and response (SOAR) market was crated. Making things work with things commonly referred to as DevOps is becoming a huge need in the security industry. Ansible is a free open source SOAR you can use to learn DevOps and eventually apply automation within your organization. Developer.cisco.com is also a fantastic resource for free DevOps training. https://www.ansible.com/ (Links to an external site.)
- Identity Management – As any organization grows, user management becomes a challenge. This is why identity management tools are important. They allow to develop groups and provision access across those groups simplifying the user management challenge. Such tools also allow for monitoring access as well as revoking access across multiple systems when a user is no longer authorized to access such systems. Open Identity offers different identity management tools that can solve this need. https://www.openidentityplatform.org/ (Links to an external site.)
Other Open Source Tools
There are many other open source projects available to access now. For example, Cisco’s research team Talos continuously publishes new open source tools ranging from plug-ins for enterprise tools to decryptors for certain forms of Ransowmare. Find those tools at https://talosintelligence.com/software
Next Steps
Open source is a fantastic option when you have the resources to invest into a open source project. If you have a specific need for a tool and don’t have the budget for it, tools from this list can help. For example, you can secure a personal device using free antivirus/antimalware and consider a free breach defense tool for your network. If you want to evaluate something for vulnerabilities, you could download Kali Linux and use many of the tools built in for that purpose.
I recommend checking out any of these tools as well as learning more about DevOps as it is a way for open source tools to work with other tools. You can learn more about DevOps at developer.cisco.com.




When bot attacks become rampant, bot mitigation tools are in great need nowadays. It should be cost efficient, responsive and easily visualized.