For those that are going to DEF CON this year, I highly suggest checking out the red team village along with wall of sheep and other cool villages. My buddy Omar posted about what will be going down at the Red Team village this year. Here is that post also found HERE.
As one of the co-leads and the co-founder of the DEF CON Red Team Village, I (Omar) would like to invite you to join us next week during DEF CON 31! The DEF CON Red Team Village is gearing up for yet another year of amazing discussions, challenges, and workshops. As the world of red teaming, ethical hacking, and cybersecurity constantly evolves, the DEF CON Red Team Village showcases the latest trends in offensive security.
The workshops and CTFs will take place on August 10–13. The village’s hours of operation during DEF CON 31, as as follows:
- Friday: 11:00–17:00
- Saturday: 09:00–17:00
- Sunday: 09:00–12:00
These are also documented in our website at: https://redteamvillage.io
Let’s unpack some of the most anticipated workshops for this year. The full schedule is posted at: https://redteamvillage.io/schedule
Stories from the Trenches (A Panel)
We will kickoff with a panel with some of the best in the business —@Nahamsec, @_JohnHammond, @lazzslayer, @0dayCTF, &
pwneip. Expect thrilling stories, lessons learned, and a comprehensive Q&A.
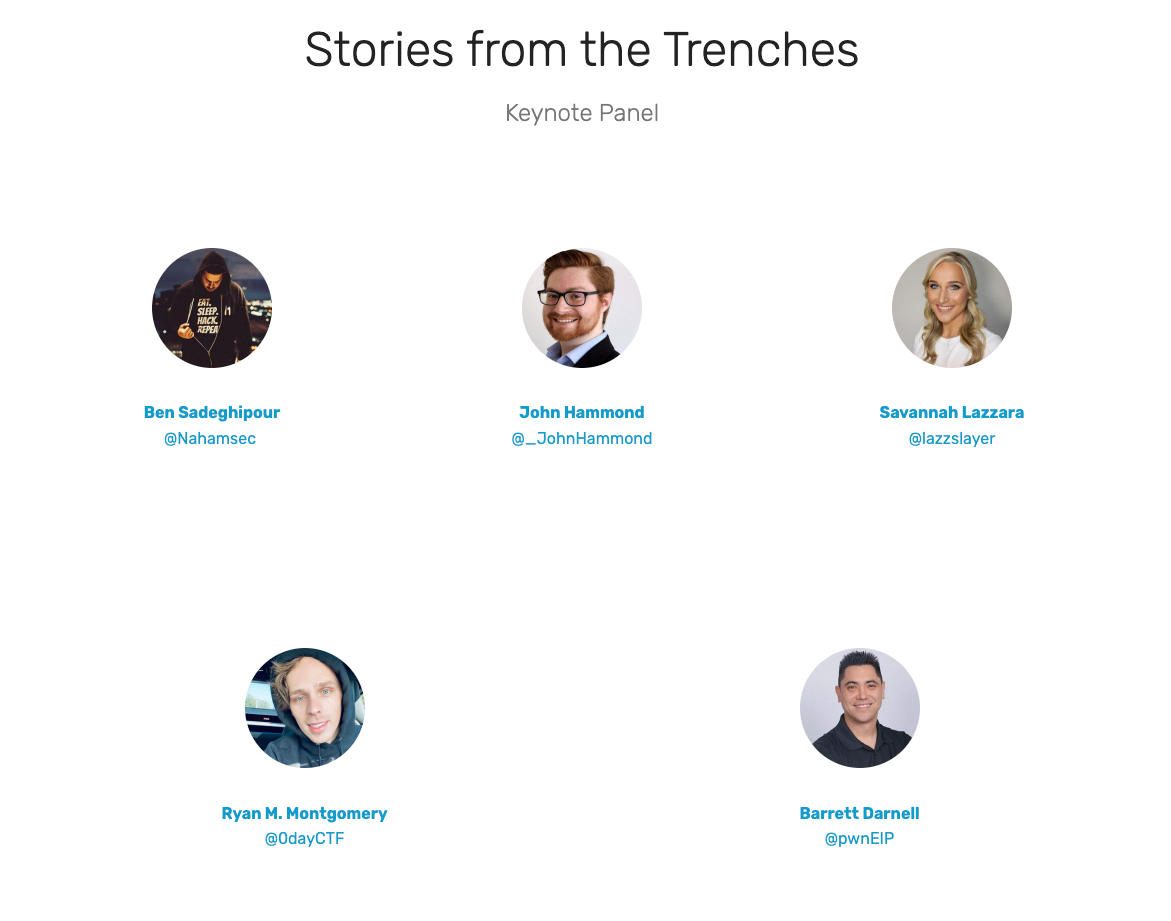
BTW, Savannah Lazzara (@lazzslayer) is one of the leads of the Red Team Village, as well as Barrett Darnell (
pwneip) which leads the CTF with Wes Turner (@NopResearcher).
Scripting OWASP Amass for a Customized Experience
This workshop will be delivered by a good friend, and the creator of the OWASP Amass tool, Jeff Foley (@jeff_foley). This course targets professionals seeking precise visibility in charting an organization’s external attack surface. Utilizing the OWASP Amass Project’s open-source tool, participants will learn to identify exposed online assets. While many have used basic Amass features in red teaming and other security tasks, few have maximized its potential by adding new features and data sources. This hands-on training will familiarize attendees with the Amass Engine, its extensibility, and the project’s future roadmap. Extensions will be coded in Lua, with example scripts provided for those new to the language.
Recon for Red Teamers and Bug Hunters 2.0
By my great friend Jason Haddix (@jhaddix). Dive into a riveting 2-hour workshop with Jason, where he’ll deep dive into tools and tactics aimed at targeting enterprises and their personnel. Delve into topics like email acquisition, technology profiling, and understanding the external attack landscape including cloud, mobile, and beyond. Plus, explore historical endpoint data mining and so much more. Experience firsthand as Jason breaks down each tool from the arsenal live, sharing his insider secrets along the way. Brace yourself as the workshop zooms into live targets. If you’re involved in offensive security, you won’t want to miss this enlightening session. Jason is a recognized leader in bug bounties and offensive security!
Red Hot (Red Team TTPs)
By: Ralph May (@ralphte1) and Steve Borosh (@424f424f ). The ever-changing landscape of Red Teaming is well encapsulated in this session. It promises to shed light on the latest Tactics, Techniques, and Procedures used by modern Red Teams.
Build Your Own Cat-Shaped USB Hacking Tool! (with the Nugget)
By: Alex Lynd (@alexlynd). An engaging, hands-on experience where participants will construct their “USB Nugget” and learn how to deploy prank payloads.
OSINT Skills Lab Challenge
This CTF-like workshop was created by great supporters of the Red Team Village for many years: Lee McWhorter, CTO of Covered 6 and Sandra Stibbards, Owner of Camelot Investigations
An incremental challenge that will test and sharpen your Open Source Intelligence abilities. As you conquer each challenge, anticipate a steady rise in complexity.
Open Source Intelligence (OSINT) for Hackers
This workshop is also created by Lee McWhorter, CTO of Covered 6 and Sandra Stibbards, Owner of Camelot Investigations. The Open Source Intelligence (OSINT) for Hackers workshop, as part of the Red Team Village, provides extensive information and hands on lessons relating to surface and deep web searching along with advanced online search techniques & strategies, online privacy / anonymity tools, counterintelligence techniques used by the criminal element, search techniques of blogs and social networks including social media monitoring, utilize database systems, methods to obtain historical website pages, develop previous domain & website details that no longer exist, geolocating, reverse imaging, transfer of large files, screenshot capabilities, and much more all focused on helping Hackers related to threat hunting, red teaming and information gathering.
Hunting & Exploiting DLL Sideloads
By: Matthew Nickerson and Nick Swink — Offensive Security Consultants @ Layer 8 Security
As captured in their abstract: “This workshop will go through the process of manually identifying applications that can be vulnerable to DLL Sideloading and exploiting them. Attendees will learn how to use Promon to find applications that can be vulnerable to DLL sideloading, identify the correct DLL functions to proxy using CFF Explorer, and write a basic DLL to run shellcode.”
An Introduction to SAML and its Security
By: Louis Nyffenegger (@snyff). Dive deep into the world of Security Assertion Markup Language (SAML), understanding its architecture and inherent security concerns.
AI-Driven Hacker’s Toolkit

I will present this workshop at the village this year. Everyone is Leveraging AI as a Co-Pilot. Let’s do it to learn Python and Scapy for Red Team Operations and offensive security. Artificial Intelligence (AI) has paved its way into many fields, and cybersecurity is no exception. AI can significantly augment red team operations by enhancing the learning process of key tools like Python and Scapy. Let’s delve into how AI can act as an indispensable co-pilot in mastering these crucial tools for cybersecurity tasks. One of the primary benefits of utilizing AI in learning things like Python and Scapy is the technology’s ability to create personalized, adaptive learning pathways. AI systems can analyze a learner’s progress, identify areas where they struggle, and provide additional exercises and resources to bolster understanding. AI provides real-time, interactive feedback, allowing learners to identify and correct mistakes immediately. In red team operations, where precision and accuracy are paramount, such instantaneous feedback can significantly enhance the learning process. This feature is particularly beneficial in learning programming languages like Python and tools like Scapy, where troubleshooting and debugging are essential skills.
This workshop is designed to equip hackers, and IT professionals with advanced techniques and hands-on experience in reconnaissance, exploitation, and post-exploitation operations using Python and Scapy.
Hacking Web Apps and APIs with WebSploit Labs
Every year I release new content in WebSploit Labs for DEF CON. This year, I will be releasing a LOT of new challenges and hands-on exercises.

Uncover vulnerabilities in web applications and APIs, and understand how to exploit them with the convenience of WebSploit Labs.
CRTFSS: Common Red Team Findings Score System Ver. 1.0
By Guillermo Buendia (@bym0m0) one of the core-members of BSides CDMX. This new scoring system promises to bring a unified way of categorizing and prioritizing red team findings, which will be invaluable to cybersecurity experts.
Malware Hunting an Offensive Approach
This workshop was created by our good friend from Brasil, Filipi Pires
@FilipiPires. Enhancing an offensive mindset stands at the forefront of this training. Here, you will master the art of devising varied strategies to launch sophisticated attacks and understand the intricacies of their delivery. This immersive experience will guide you through executing numerous efficiency and detection tests within your lab environment. By coupling a defensive security perspective with an aggressive approach, you will emulate real-world cybercriminal tactics, empowering you to proactively identify and counteract these threats. Dive deep into the mechanics of the Cyber Kill Chain, acquaint yourself with Static and Dynamic Analysis of select file types, and harness the skills to execute your bespoke attacks.
IOCs + APTs = “Let’s play a game!” — Hack Your Way through a Hunt!
By my colleague Leo Cruz from Cisco. To excel in threat hunting and craft insightful threat intelligence, prioritize understanding the “what” before the “where”, the “where” before the “why”, and the “why” before the “who”. Only then might you discern the true identity of your attacker. This CTF-style threat hunt places you in dual roles: as both the attacker and the defender. Along the journey, recognize that you’re also the malware creator, reverse engineer, network analyst, and more. Whatever route you choose, your mission is to pinpoint all the Indicators of Compromise (IOCs) before the clock ticks down, or risk leaving the true adversary concealed.
Hacking Real Web Areas
By: Ilkin Javadov (@IlkinJavadov). Offering a technical demonstration, attendees will witness a live demo mirroring the one presented during Gisec 2023 Global, focusing on the intricate identification and exploitation of Cross-Site Scripting (XSS). In addition to XSS, the talk will explore emerging trends in other potential security pitfalls, such as injection flaws and broken access controls. By the end of this session, participants will gain valuable insights into the hacker’s approach, equipping them with knowledge to preemptively address and rectify potential system vulnerabilities.
SSH Tunneling: Evading Network Detection and Creating Proxies
By one of the core voluteers at the Red Team Village, Cory Wolff (
Cory Wolff). SSH tunneling, when skillfully employed, becomes an indispensable tool for red teamers. However, the complexity lies in fully understanding its nuances — like reverse port forwards, local port forwards, and dynamic port forwards, which can be daunting for many operators.
This presentation will initiate with the foundational elements of SSH tunneling and later shift its emphasis on leveraging these techniques to craft reverse proxies and bypass network surveillance during operations. The goal is to elucidate the distinctions and applications of these port forwards, supplemented by real-world offensive security examples.
Storfield: A Quiet Methodology to Create Attacks in Mature Networks
This one is also presented by our friend Cory Wolff (
Cory Wolff). The Storfield Approach centers on three primary elements: Where am I? Where is the domain controller (DC) located? Where can I find the high-priority targets?
Build Your Own WiFi Hacking Tool with the Nugget!
Also by Alex Lynd (@alexlynd). During the initial part of this workshop, participants are introduced to the art of soldering, its tools, and methods. They are then led through the process of constructing a “Nugget” kit, which includes a cat-themed PCB, display, microcontroller, and a 3D-printed case.
In the workshop’s second half, attendees dive into the basics of WiFi hacking. This segment acquaints novices with prevalent techniques, attack pathways, and practical instances. Participants receive a brief overview of the WiFi protocol and its vulnerabilities. Subsequently, they will assemble a rudimentary CircuitPython-driven network protection device on their Nugget, designed to identify WiFi assault attempts.
Android Applications and APIs Hacking
By: Gabrielle Botbol (@Gabrielle_BGB). In this workshop, attendees will dive into the intricacies of pentesting Android apps and their associated APIs. The presentation demystifies Android pentesting, guiding participants on establishing an Android App pentest lab and walking them through the entire process of testing an Android app and its APIs. By the session’s conclusion, participants will be armed with valuable tips, resources, and a comprehensive toolkit for Android app pentesting, enhanced by hands-on examples using a deliberately vulnerable application. This talk is tailored to benefit those at the beginner level.
The Red Team Village CTF
The Red Team’s Capture the Flag (CTF) challenge at DEF CON this year will be freaking awesome! This CTF’s goal prompts teams to infiltrate the defenses of a mock target network. Designed to mirror real-life attack situations, participants must employ a vast array of hacking methods, tools, and expertise to pinpoint and leverage vulnerabilities. Be in the lookout for a video with Barrett Darnell (
pwneip), Wes Turner (@NopResearcher), and @ippsec talking about the CTF this year. The video should be out in our YouTube channel in the next few days.
The Red Team Village DEFCON 31 Badge
Check out this video by my friend and co-lead, Savannah Lazzara(@lazzslayer) and William (from United Electronics) with a preview of the electronic badge this year. Pick yours up now! https://redteamvillage.square.site/
https://cdn.embedly.com/widgets/media.html?src=https%3A%2F%2Fwww.youtube.com%2Fembed%2FDSHE3wXIkSA%3Fstart%3D379%26feature%3Doembed%26start%3D379&display_name=YouTube&url=https%3A%2F%2Fwww.youtube.com%2Fwatch%3Fv%3DDSHE3wXIkSA&image=https%3A%2F%2Fi.ytimg.com%2Fvi%2FDSHE3wXIkSA%2Fhqdefault.jpg&key=a19fcc184b9711e1b4764040d3dc5c07&type=text%2Fhtml&schema=youtube
The Red Team Village DEFCON 31 Badge is device that’s more than just an identifier. This badge, rooted in ESP32-S2 technology, is pre-loaded with cool challenges. It has a vibrant 2.8″ display, it’s a cool at real-time Wi-Fi network monitoring, and can even track Wi-Fi deauth packets in your vicinity. It operates on just 2 AA batteries and includes a stylish lanyard for easy wear. The badge also features an SAO port, opening up even more avenues for interactive fun. Dive in and explore the myriad possibilities this badge offers! Pre-order and pick it up at the village from: https://redteamvillage.square.site/
This article only provides a glimpse into the wide range of workshops we have to offer at the Red Team Village. Attendees are encouraged to review the full schedule for a comprehensive understanding of the workshops and activities.