Cisco has finally released Identity Services Engine ISE 1.2 aka the BYOD release.
You can find more about it at www.cisco.com/go/ise
The ISE 1.2 release notes can be found HERE
Here is a list of the new features found in Cisco ISE 1.2:
* Mobile Device Management Interoperability with Cisco ISE – This is the big feature everybody has been waiting for. Cisco now can interoperate with Mobile Device Management MDM servers creating a real Bring Your Own Device BYOD solution. Prior to this release, ISE and the MDM solutions operated separately meaning you could onboard a new mobile device user however you could not verify their posture status as seen by a MDM solution. All you could do was “assume” the MDM vendor was doing its job of keeping that device secure. Now with ISE 1.2, you can verify and act upon what the MDM solution sees with ISE.
The supported MDM vendor list is Airwatch, Good Technology, Mobile Iron, Zenprise, SAP Afaria, FiberLink Maa360 and Cisco Mobile Collaboration Management services.
Another interesting thing to look at is Cisco offers Smart Solutions. Cisco Smart solutions such as BYOD covers Cisco Wireless, Identity Services Engine ISE and MDM vendors from the support list. What this means to you is
1) TAC will support the entire solution. That means they will troubleshoot Wireless, ISE and the 3rd party MDM vendor if its listed on the Smart Solution website.
2) These solutions have been tested to work together by Cisco
3) There is documentation on how to make it all work.
More on the BYOD smart solution can be found HERE
* Support for UCS Hardware – Cisco ISE now supports the Unified Computing System UCS C220 hardware aka SNS-3415 and SNS-3495
* Improved Performance and Scalability – ISE 1.2 is now a 64-bit architecture. This increases the overall performance scaling to 250,000 concurrent endpoints per ISE deployment. 1.1.x and older maxed out at 100,000 concurrent endpoints per ISE deployment.
* MAB from Non-Cisco Switches – Now non-Cisco switches are supported for Machine Authentication Bypass (MAB). MAB is key for devices that don’t support 802.1x.
* Support for Universal Certificates – ISE 1.2 supports wildcard server certificates for HTTPS and EAP protocols that use SSL/TLS tunneling. This means you don’t have to generate a unique certificate for each Cisco ISE node *cheers*. Another benefit is avoiding populating the SAN field with multiple FQND values to prevent certificate warnings. being able to use a asterisk in the SAN field with
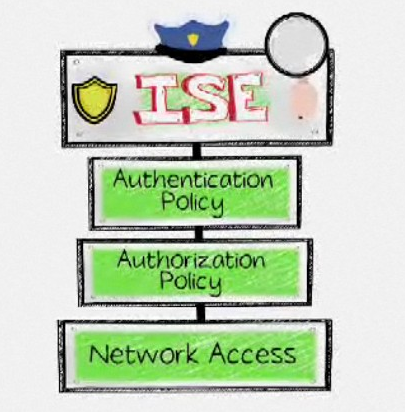
* Policy Sets – ISE 1.2 allows you to create a set of authentication and authorization policy for various use cases.
* Profiler Feed Service – This is really cool. Cisco is finally publishing new profile definitions, updates to definitions and new OUI databases posted.
Cisco ISE, Release 1.2 provides a profiler feed service for publishing new profile definitions, updated profile definitions, and new OUI databases posted from IEEE. My assumption is this will be based on profiles created by Cisco, Customers and manufacture releases (IE a new gaming system comes out and Cisco matches a profile). Here is a summery of this straight from the release notes:
“You can retrieve new and updated endpoint profiling policies and the updated OUI database as a feed from a designated Cisco feed server through a subscription in Cisco ISE. You can also receive email notifications at an administrator email address that is configured for applied, success, and failure messages. You can also provide additional subscriber information to receive notifications. You can send the subscriber information back to Cisco to maintain the records and they are treated as privileged and confidential.”
* Logical Profiles – Cisco ISE profiles can now be grouped in logical profiles IE container for a category of profiles or associated profiles. I need to test this but assume you could do something like group MOBILE DEVICES, which contains adroit, apple ios, etc devices. This makes it easier to apply changes to a massive group of profiles. Again, I need to test this to be sure.
* Enhanced Guest and Sponsor Pages – Cisco added more default themes in ISE 1.2. My guess is these are built around BYOD making it easier to understand the on boarding of guest and sponsored users. I’ll post images once I get my lab up.
* RADIUS Authentication Suppression – This allows you to configure RADIUS settings to detect the clients that fail to authenticate and to suppress the repeated reporting of successful authentication. Cool … less log noise!
* Collection Filters – You can configure collection filters to suppress syslog messages being sent to the monitoring and external servers. The suppression can be performed at the Policy Service Node level based on different attribute types. Again .. cool … less log noise.
* Support for Secure Syslogs – ISE 1.2 can be configured to send secure syslogs to Monitoring nodes and between Cisco ISE nodes, by enabling TLS-protected syslog collectors.
* Support for Windows 2013 Active Directory – Self explaining
* Global Search – I really like this feature. Now you can do a system-wide endpoint search for endpoints and users on the network. I’m surprised this wasn’t a 1.0 feature to be honest.
* Session Trace – Self explaining. This will be very useful for future troubleshooting.
* Enhanced Reports and Alarms -Self explaining. I’ll dig into this more once I get it up in my lab. My assumption is based on customer feedback, they have made things easier to use.
* Enhancements to Live Authentications Page – Cisco ISE dashboard shows the details corresponding to authentication entries. This sounds like now we don’t have to go to the monitor page to see live authentications. It should be nice having that on the main dashboard.
* Enhancements to Cisco NAC Agent – Supports windows 8, Log package option for log collection, and MAC acceptance use policy.
* External RESTful Services – External RESTful Services (ERS) is a new Cisco ISE component that allows you to perform Create, Read, Update, and Delete (CRUD) operations on Cisco ISE resources. ERS also allows you to run advanced queries against the Cisco ISE database and perform bulk operations such as mass updates or deletions.
I’m personally temporary between labs at the moment (just took a job with Cisco) but will be downloading and building an official ISE 1.2 lab after I get back from the Blackhat / Bsides / Defcon conferences. Sorry for the lack of screenshots and testing. I’ll get some more information up shortly.