I like the Zomato app. I use it to find restaurants that are near by when traveling. I never ordered food through it and now very happy about that. Thehackernews just posted that Zomato suffered a major breach leaking millions of user account data. They claim the passwords are the hash so the attackers wont know the original password but this is still pretty bad. The original post can be found HERE.
If you ever ordered food from Zomato, You should be Worried!
In a blog post published today, the company said about 17 Million of its 120 Million user accounts from its database were stolen.
What type of information?
The stolen account information includes user email addresses as well as hashed passwords.
Update: As shown in the above screenshot taken immediately after they updated their blog post, Zomato has changed its statement from “your password can not be converted/decrypted” to “can not be easily converted” back to plain text.
The updated statement now reads:
“We hash passwords with a one-way hashing algorithm, with multiple hashing iterations and individual salt per password. This means your password cannot be easily converted back to plain text.”
Also, Zomato stressed that the breach did not impact or compromise any payment card data, as the financial information of its customers is stored in a separate database different from the one illegally accessed.
“Payment related information on Zomato is stored separately from this (stolen) data in a highly secure PCI Data Security Standard (DSS) compliant vault. No payment information or credit card data has been stolen/leaked,” the company claims.
17 Million Zomato Accounts Sold on Dark Web
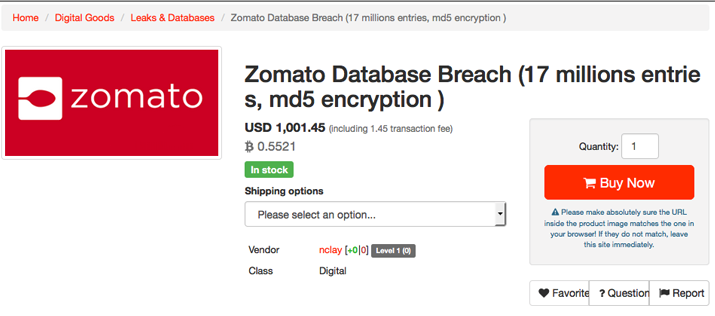 According to HackRead, a user going by the online moniker of “nclay,” who claimed to have hacked Zomato, is selling data of 17 Million registered Zomato users on a popular Dark Web marketplace.
According to HackRead, a user going by the online moniker of “nclay,” who claimed to have hacked Zomato, is selling data of 17 Million registered Zomato users on a popular Dark Web marketplace.
The company believes that someone from inside its organization is responsible for the security breach.
What should Zomato Customers do?
Customers should particularly be alert of any phishing email, which are usually the next step of cyber criminals after a breach to trick users into giving up further details like financial information.
For the obvious reasons, all customers are highly recommended to change their passwords for Zomato accounts as soon as possible, along with other websites that are using the same passwords, and choose unique passwords for different accounts.
If you can’t create or remember complex passwords for different sites, you can make use of a password manager.
We have listed some good password managers for Android, iOS, Windows, Linux and Mac platform that could help you understand the importance of password manager and choose one according to your requirement.