For those have been following the various forms of Ransomware in the wild (more on exploit kits and ransomware HERE), TelsaCrypt was one that came out a while back. Cisco’s security team Talos created a decryption tool for a few variants of TelsaCrypt (found here) however later versions used a form of asymmetric encryption preventing decryption. Well it seems the people behind TelsaCrypt have moved on to bigger and worst things closing shop and posting the master decryption key. They even said SORRY! Bleepingcomputing posted about this. The original post can be found HERE. Funny thing is somebody asked for the master key and they said yes! Many of us found this shocking.
In surprising end to TeslaCrypt, the developers shut down their ransomware and released the master decryption key. Over the past few weeks, an analyst for ESET had noticed that the developers of TeslaCrypt have been slowly closing their doors, while their previous distributors have been switching over to distributing the CryptXXX ransomware.
When the ESET researcher realized what was happening, he took a shot in the dark and used the support chat on the Tesla payment site to ask if they would release the master TeslaCrypt decryption key. To his surprise and pleasure, they agreed to do so and posted it on their now defunct payment site.
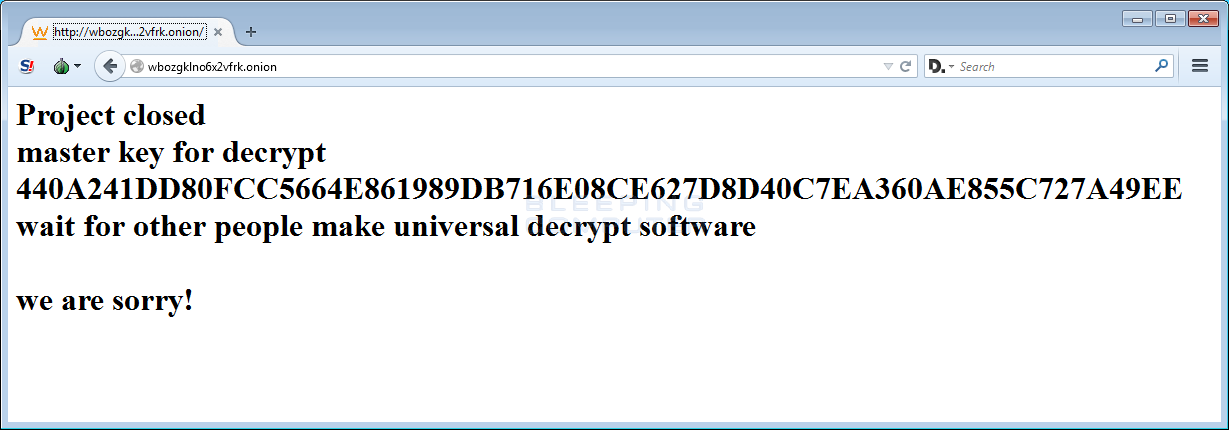 Payment site showing Master Decryption Key
Payment site showing Master Decryption Key
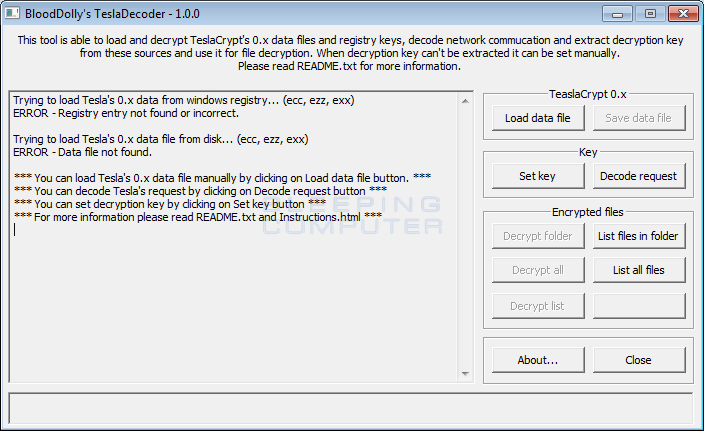
Now that the decryption key has been made publicly available, this allowed TeslaCrypt expert BloodDolly to update TeslaDecoder to version 1.0 so that it can decrypt version 3.0 and version 4.0 of TeslaCrypt encrypted files. This means that anyone who has TeslasCrypt encrypted files with the .xxx, .ttt, .micro, .mp3, or encrypted files without an extension can now decrypt their files for free!
How to use TeslaDecoder to decrypt Teslacrypt Encrypted Files
With the release of the master decryption key for TeslaCrypt, victims can now download TeslaDecoder to decrypt files encrypted by TeslaCrypt. Simply use the download link below and save TeslaDecoder to your desktop.
TelaDecoder is downloaded as a zip file, so you need to extract it and then double-click on the TeslaDecoder.exe file. This will launch TeslaDecoder as shown below.
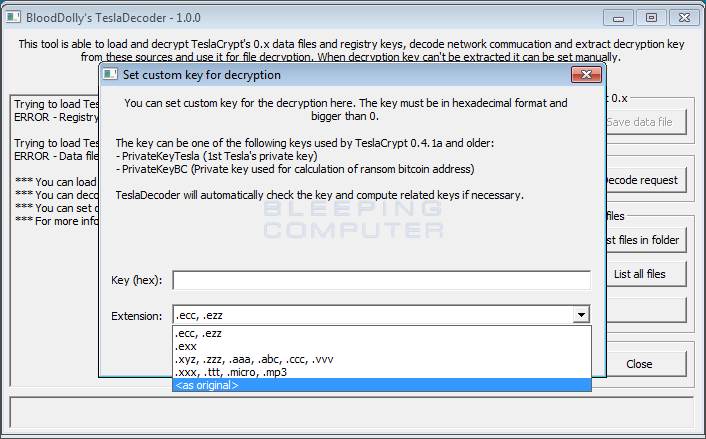
 Now click on the Set Key button and select the extension used for your encrypted files.
Now click on the Set Key button and select the extension used for your encrypted files.
If your encrypted files have the same name as the original files, select the option.
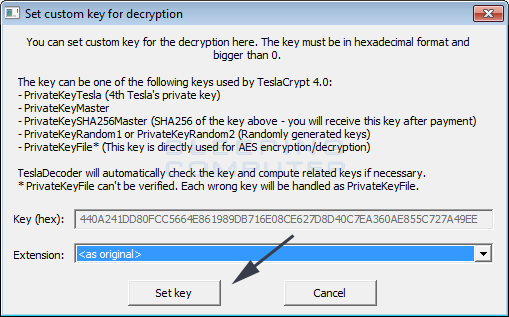
Once you have selected your encrypted file extension, click on the Set Key button as shown in the image below.
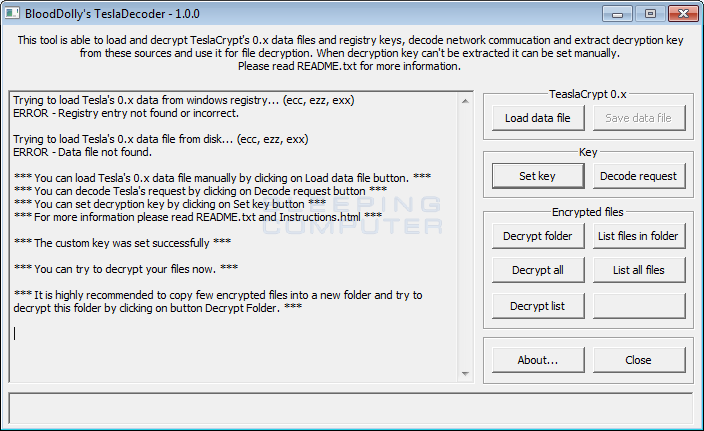
You will now be at the main screen with the correct decryption key loaded into the decryptor as shown below.
Now that the correct decryption key is loaded into the decryptor, you can either decrypt a certain folder or have it scan your entire drive. To decrypt only a specified folder, click on the Decrypt folder button. To decrypt the whole computer, click on the Decrypt all button. When you click on this button, TeslaDecoder will ask if you want to overwrite your files with the unencrypted version. To be safe, I always suggest that you do not do this in case something fails with the decryption.
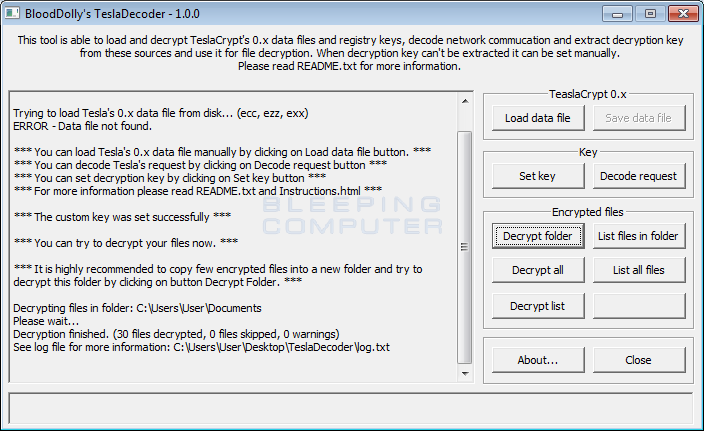
When TeslaDecoder is done decrypting your files, it will show a summary in the main window.
All of your files should now be decrypted and if you did not choose to overwrite your files, there will be backups of the encrypted files with the .TeslaBackup extension added to them.
A big thanks to ESET and especially BloodDolly who has monitored every version of TeslaCrypt that was released. He has done a tremendous amount for the fight against ransomware and for helping TeslaCrypt victims all over the world!