Wired.com posted about how two hackers found a way to plant a trojan on Tesla cars. The original post can be found HERE. There has been a ton of press on car hacking. Maybe its time to buy a classic verses something new.
TESLA CARS HAVE one security advantage that a lot of other cars don’t: the electric vehicles are impervious to hot-wiring, so a thief can’t just break into your $100,000 vehicle, pop open the steering column, futz with some cables and drive off. But if he has a computer with him, he could “hot-wire” it another way.
Two researchers have found that they could plug their laptop into a network cable behind a Model S’ driver’s-side dashboard, start the car with a software command, and drive it. They could also plant a remote-access Trojan on the Model S’ network while they had physical access, then later remotely cut its engine while someone else was driving.
Kevin Mahaffey co-founder and CTO of mobile security firm Lookout and Marc Rogers, principal security researcher for CloudFlare, discovered the vulnerabilities after digging through the architecture of a Tesla Model S over a period of about two years and will be discussing their findings at the Def Con hacker conference on Friday in Las Vegas.
Both of these hacks require physical access to the car, at least initially, and they require control of the car’s infotainment system, which has the ability to start the car or cut power to it.
But they also found that the car’s infotainment system was using an out-of-date browser, which contained a four-year-old Apple WebKit vulnerability that could potentially let an attacker conduct a fully remote hack to start the car or cut the motor. Theoretically, an attacker could make a malicious web page, and if someone in a Tesla car visited the site, could gain access to the infotainment system. “From that point, you’d be able to use a privilege escalation vulnerability to gain additional access and do the other stuff that we described,” Rogers says. The WebKit vulnerability is a well-known and well-documented hole that has already been used by previous attackers to gain privileged access to other systems. Rogers and Mahaffey didn’t test this method of intrusion on the Tesla, but Rogers notes that finding a privilege escalation vulnerability isn’t out of the question. Tesla recently patched one in the Model S’ Ubuntu Linux operating system.
The researchers found six vulnerabilities in the Tesla car and worked with the company for several weeks to develop fixes for some of them. Tesla distributed a patch to every Model S on the road on Wednesday. Unlike Fiat Chrysler, which recently had to issue a recall for 1.4 million cars and mail updates to users on a USB stick to fix vulnerabilities found in its cars, Tesla has the ability to quickly and remotely deliver software updates to its vehicles. Car owners only have to click “yes” when they see a prompt asking if they want to install the upgrade.
“Tesla has taken a number of different measures to address the effects of all six vulnerabilities reported by [the researchers],” a Tesla spokeswoman told WIRED in an email. “In particular, the path that the team used to achieve root (superuser) privileges on the infotainment system has been closed off at several different points.” She also noted that the effects of some other vulnerabilities have been mitigated. “In particular, the browser has been further isolated from the rest of the infotainment system using several different layered methods.”  Hijacking the ethernet connection from the IC, the instrument cluster screen, in order to bypass the network security and access the car’s network.
Hijacking the ethernet connection from the IC, the instrument cluster screen, in order to bypass the network security and access the car’s network.
The researchers’ primary goal in examining the Model S was to determine what Tesla did right or wrong with the car in order to figure out how the wider car industry could better secure vehicles.
Though the Tesla hacks highlight some of the dangers around digitally connected cars, the researchers’ findings are not as serious as those demonstrated two weeks ago against a Chrysler Jeep. In that case, the vehicle had no separation between its infotainment system and the critical drive system, so once researchers compromised the infotainment system they could communicate with the drive system and cut the brakes or control the steering if the car was in reverse. Tesla, however, has a gateway between the infotainment and drive systems that is intended to prevent a hacker, remote or otherwise, from reaching critical functions like these.
“Early in the industry you have this kind of weird lemming effect, that if nobody does security well, they all kind of jump off the cliff simultaneously,” says Mahaffey. “And if there are one or two companies that are actually doing it well, then shining the light on them … helps raise the overall bar for the entire industry.”
The company also engineered the car to handle sudden power loss in a graceful way. If power to the car were cut while the vehicle was in motion, the hand brake would kick in, and the car would lurch to a stop if it was traveling 5 miles per hour or less. It would go into neutral if traveling faster than this. But the driver would still retain control of the steering and brakes and be able to pull the car over. The airbags also would still be fully functional.
“That in itself I think is a huge achievement that I’d like to call Tesla out for,” says Rogers. “This is a directly contrasting story to the Jeep story… Tesla had actually thought about the ramifications about what might happen and had designed the car to handle it gracefully and be safe… in such a way that catastrophic [failure] would not happen.”
Mahaffey also commended the company’s over-the-air patching. “If you have a good patch process, it can solve a lot of problems. If you look at a modern car, it’s running a lot of … software and it needs to be patched as frequently or sometimes even more frequently than a PC, and if you have to bring your car into a dealership … every week or every month, that’s just a pain in the ass. … I think every car in the world should have [an OTA process] if they’re connected to the internet.”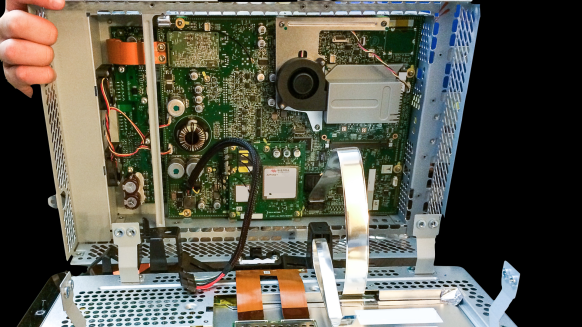 Inside the CID, the 17-inch touchscreen, where the researchers found the SD card with the car’s VPN keys.
Inside the CID, the 17-inch touchscreen, where the researchers found the SD card with the car’s VPN keys.
But there are still unanswered questions about how strongly Tesla’s gateway protects its drive system from a hacker seizing total control of a car.1
The Model S has a 17-inch touchscreen that has two critical computer systems. One is an Ubuntu server responsible for driving the screen and running the browser; the other is a gateway system that talks to the car. The Tesla gateway and car interact through a vehicle API so that when a driver uses the touchscreen to change the car’s suspension, lock the doors, or engage its parking brake, the touchscreen communicates with the gateway through an API, and the gateway communicates with the car. The touchscreen never communicates directly with the car. “At least so our research has found so far,” Mahaffey says.
Rogers likens it to the way avionics and Wi-Fi systems are configured on commercial airliners. The Wi-Fi is able to get GPS location data about the plane from the avionics system, but a gateway implements tight controls over what data can pass between the two. In the same way, Rogers says, “we know [the Tesla gateway] stops the obvious stuff. But I haven’t tested it to see what happens if I hack the gateway. If we were able to hack the gateway, then we could control any part of the car just like the Jeep hackers.”
The researchers in fact were able to get past the Tesla gateway, although they say it took a lot of effort. What they could do after this is still a question. So far they haven’t concluded what could be done to the car’s CAN bus. “Is this gateway system secure enough to stop someone from injecting [malicious] CAN messages? I can’t answer that,” says Rogers. “We didn’t go as far as to get CAN frames into the car, although we found evidence that this would definitely be possible.” View of the connectors from the back of the CID, the 17-inch touchscreen, during removal from the car.
View of the connectors from the back of the CID, the 17-inch touchscreen, during removal from the car.
They say the security of the Model S was generally good, but it was focused primarily on perimeter security, with the internal security less robust. Once an attacker got in, he could leapfrog from one component to another.
“As you gained some kind of foothold, you were able to gradually leverage that with additional vulnerabilities to increase your access,” Rogers says. “We took a bunch of relatively innocuous vulnerabilities you wouldn’t think very much about and by chaining them together and by using each one of them to leverage our ability to gain a bit more access, we were able to go deeper and deeper and deeper into the car until eventually we gained full control of the entertainment system…. Stringing all of these together was enough for us to gain user-level access and then ultimately superuser level access to the infotainment systems.”
At that point they could do anything the entertainment system could do. This included opening and closing windows, locking and unlocking doors, raising and lowering the suspension and cutting power to the car.
They could also subvert a small screen that provides the driver with speed readouts by either altering the speed the driver sees or displaying distracting pictures on it. “If you’re sitting in a car that’s traveling at high speed, and suddenly there’s no speed information, that’s actually pretty scary.”
To remotely cut the Model S engine, they installed a remote Trojan on the car’s network, then used a mobile phone to telnet into the car and cut the power.
The vulnerabilities they found to achieve all of this were fairly basic, such as having the ability to telnet or use simple network protocols to connect to services inside the network and gain intelligence about the car. The Model S has anEthernet cable for diagnostic purposes and by connecting to this they were able to get access to the car’s LAN. This allowed them to uncover information about the firmware update process, such as the configuration of the VPN the car used to obtain updates as well as the URLs from where the updates were downloaded. They also found four SD cards inside the car that contained keys for the VPN structure, and they found unsecured passwords in an update file that allowed them to gain access to the Tesla firmware update server. “By using the VPN credentials we got from the SD card, we were able to configure and open VPN clients to go and talk to Tesla’s infrastructure and mimic the car.”
The firmware updates are downloaded as compressed files over an open VPN connection, and because the VPN connection is mutually authenticated between the car and the server, no one could upload rogue firmware to the car from an unauthorized location.
The researchers plan to continue to work with Tesla on hardening its vehicles further. The car company has also recently hired Chris Evans, a highly respected security engineer who used to lead Google’s Chrome and Project Zero security teams, to head its own security team.
Mahaffey says other car companies should follow Tesla’s lead.
Regardless of the issues found with the Model S, he still considers it “the most secure car that we’ve seen.”
Correction: Though the researchers contended that Tesla does not sign its firmware updates, Tesla has informed WIRED that it does sign its updates. The story has been updated to reflect this.