If you are responsible for testing security capabilities or just have an interest in red team / pen testing, you need to check out Hak5. They make inexpensive nifty pen testing tools. Thier claim to fame is the wifi pineapple simplifying performing man-in-the-middle attacks against mobile devices (I’ve posted about this HERE) but they have so much more. You can search my blog for Hak5 posts to learn more as well as check out their catalog at https://hak5.org/. I don’t pitch vendors often, but when I do … its something cool.
Many of you probably know hak5, but do you know they also continuously release payloads? Bookmark this page – Payloads – Hak5 …. its where they post payloads that work with their products (but you can also use them for any open-source tool. For example, I’ve turned a raspberry pie into a wifi pineapple. Was it worth the time … nope but it was fun to do). For example, there has been a bunch of recent exploits that create a fake login screen … some even creating fake browser windows (IE a pop up that looks and feels like a browser but really a man-in-the-middle attack). How do you test this? Hak5 has a fake login screen payload you can use.
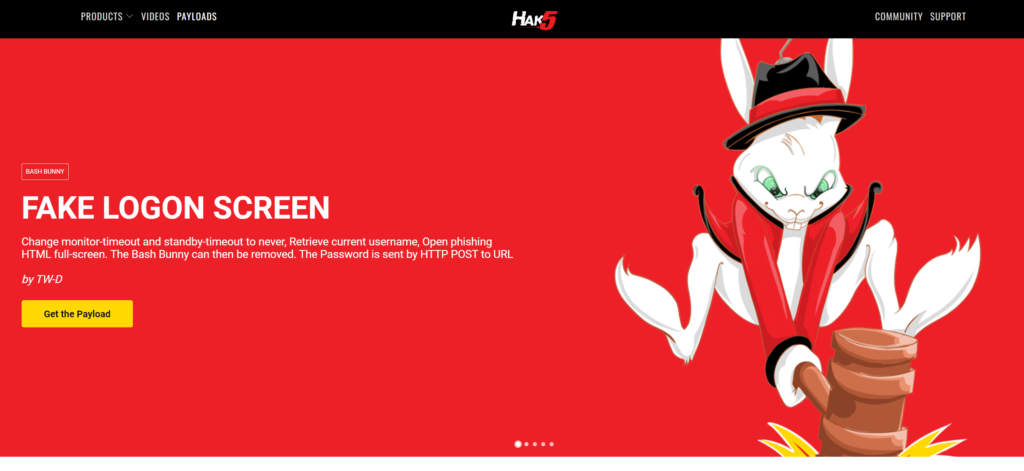
Check out the payloads. They are pretty good