Comparing the meraki MX60 to meraki Z1
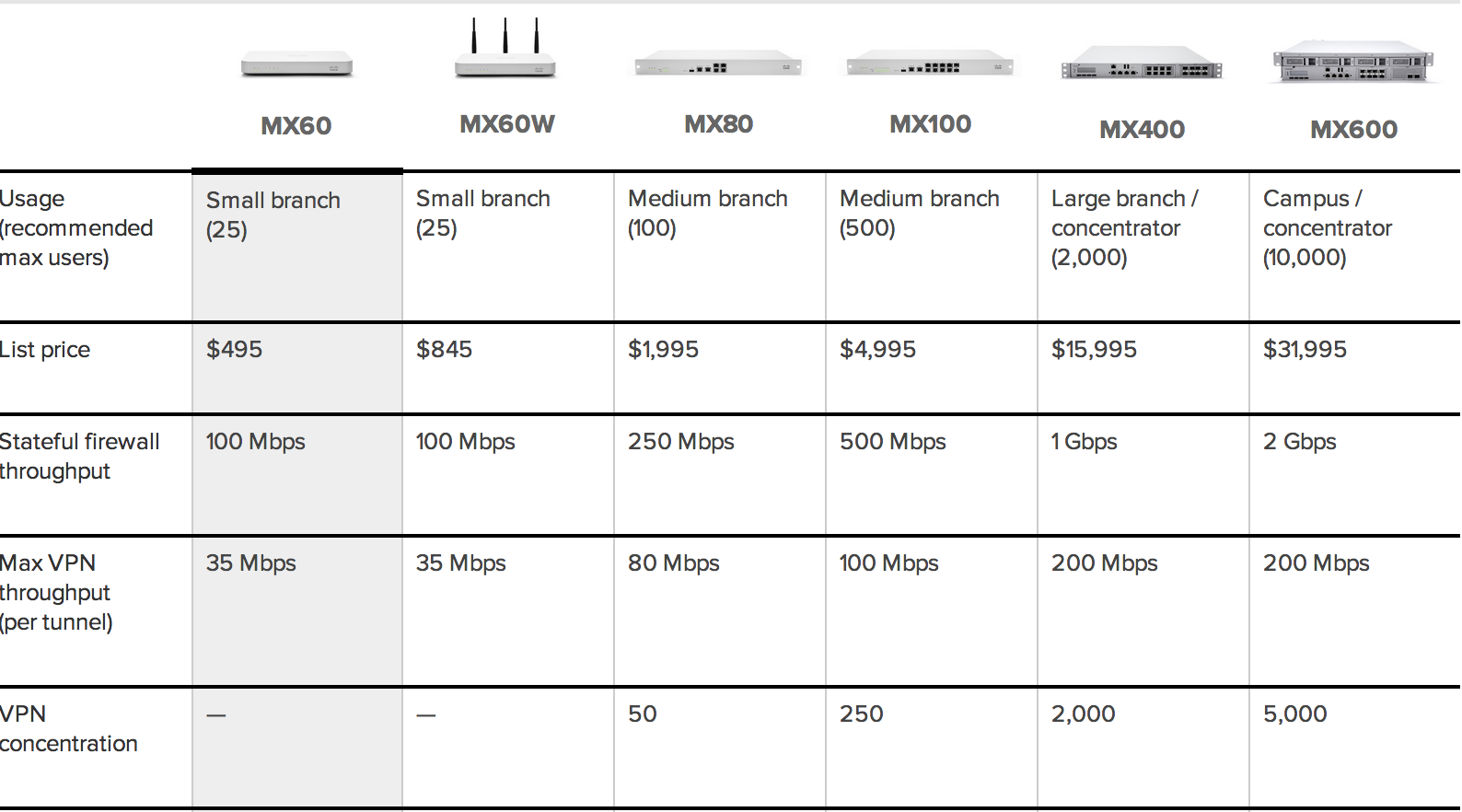
Every once in a while I like to do a product review. Next up is the meraki MX60 (shown above on the left next to the Meraki Z1). The official MX60 data sheet can be found HERE. The MX60 comes with or without wireless capabilities hence the MX60W means wireless while the one used in this post is a MX60. Outside of that, both models are the same and considered the low end / home model as shown in the next image.
Meraki Network and Security Product line
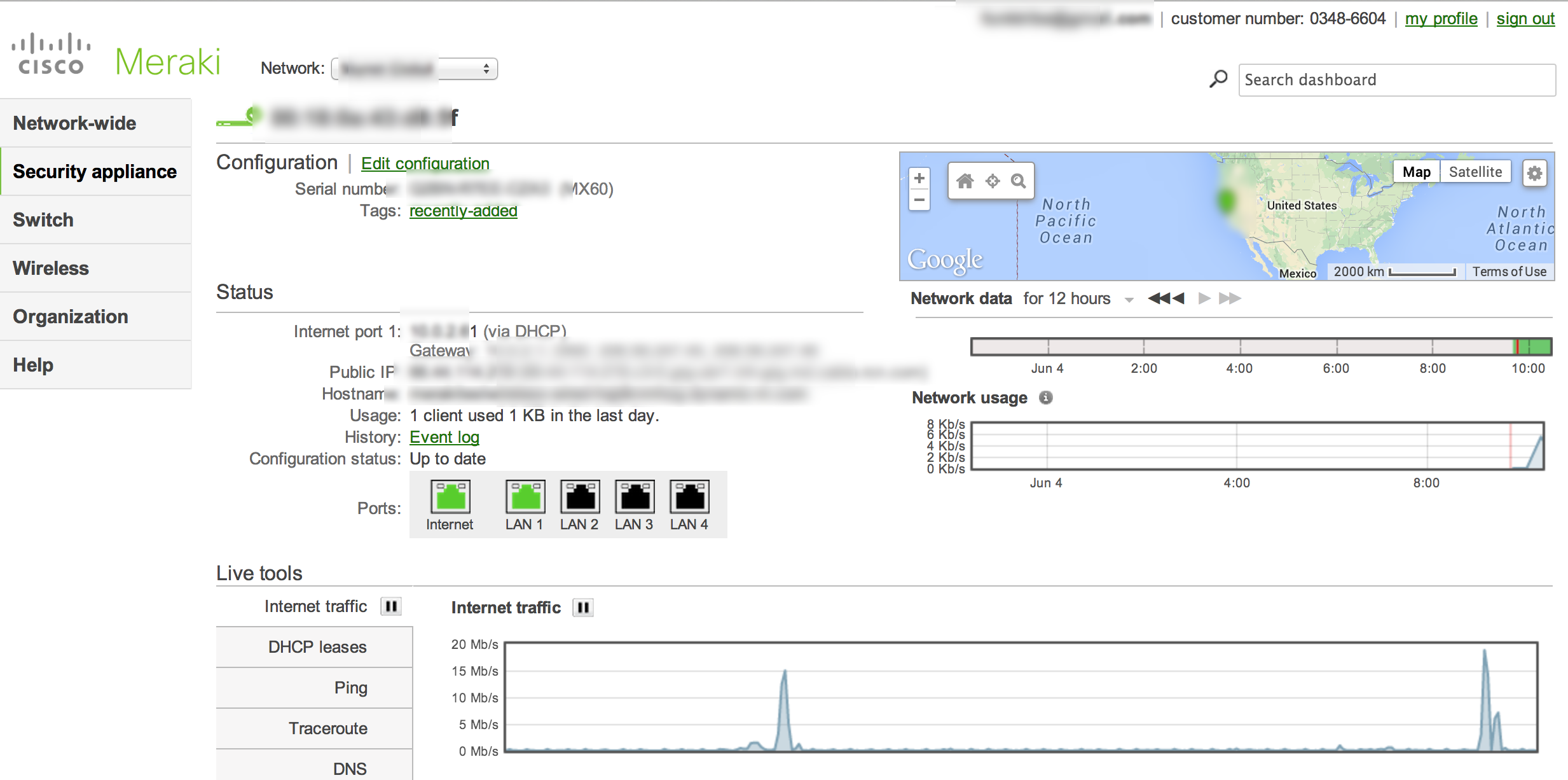
Like other Meraki solutions, the MX60 is managed using a cloud-based framework rather than accessing the appliance directly. Below is an example of me logging into my Meraki network featuring various devices. I access the main dashboard using https://meraki.cisco.com/.
Meraki main dashboard example
Once logged in, I can review the health of my entire network, dive into a particular device configuration and license other devices. The cool part about the cloud approach is a administrator could configuration devices prior to a deployment without having to console into each device. All that has to be done with the hardware is ship it and plug it in since everything configuration wise comes from the cloud. Also things like managing updates are done via the cloud so I randomly will see messages about my system being updated via email or when I log into the GUI making overall management super easy.
For the cost, the Meraki MX60 has a many features expected from a enterprise security solution. Examples are content filtering, VPN, Active Directory integration, Traffic Shaping and some access control capabilities.
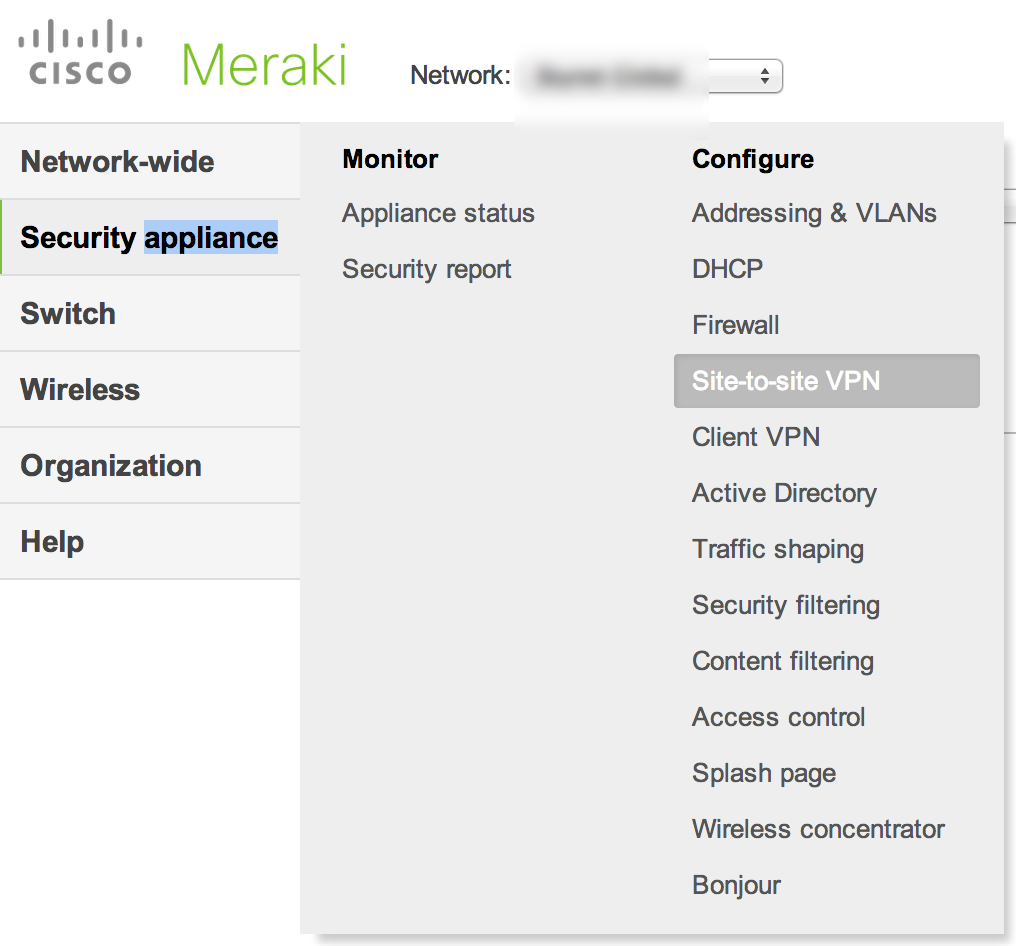
Meraki MX60 configuration areas
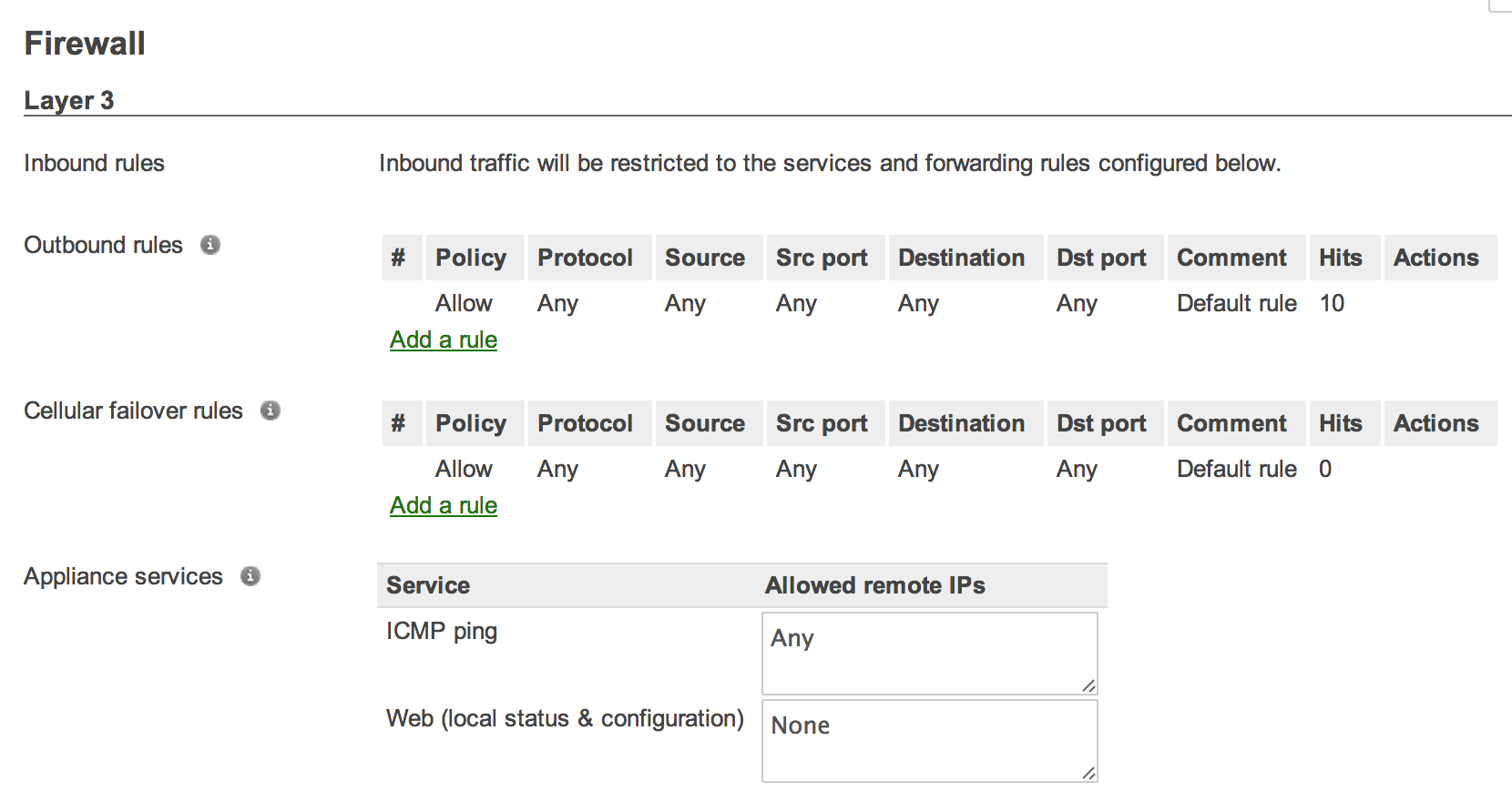
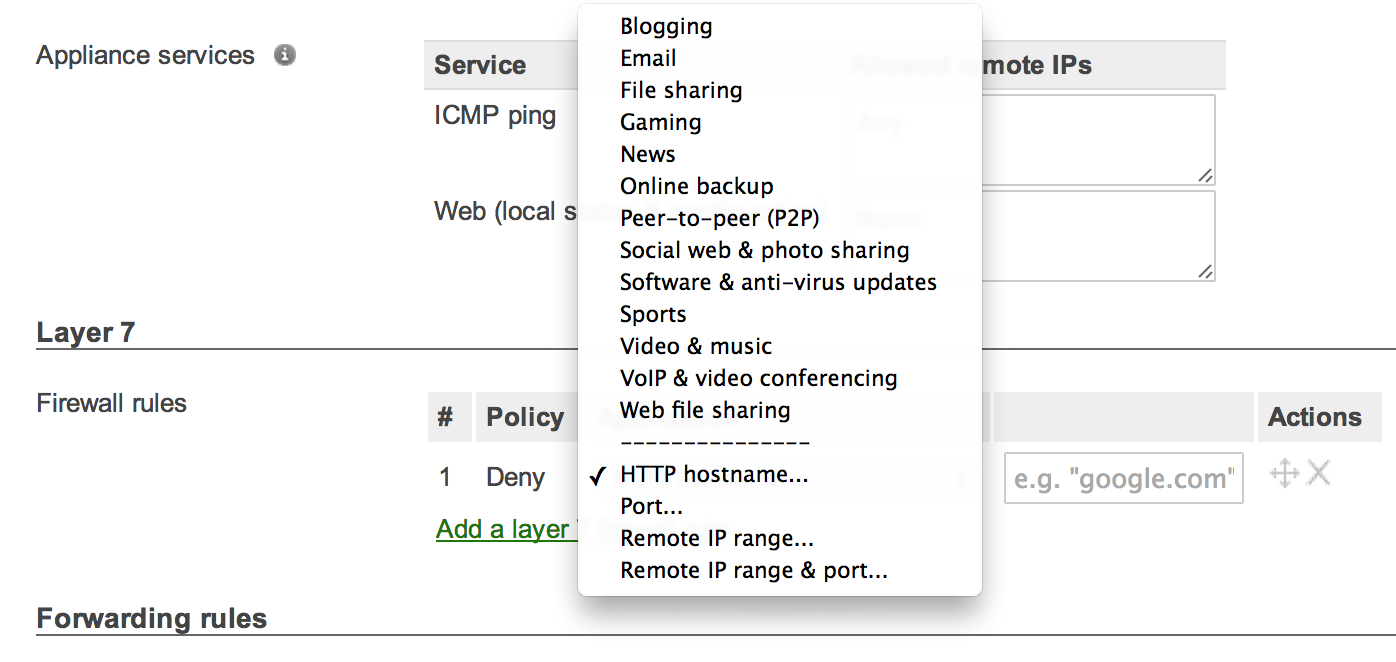
As a firewall, the MX60 offers standard access rules as well as layer 7 application layer controls. The next images show the default configuration pages for firewall rules.
Basic Firewall Rules
The content filter is pretty easy to use and based on categorizes. For example, an administrator could deny Gambling websites but white list Lottery websites. All the standard stuff is there plus known high risk sites such as Bot Nets as shown below. There are also popular functions such as YouTube for schools and clean search engines meaning cleaning up what can be accessed (example is a search for “chicks” would bring up chickens rather than ladies).
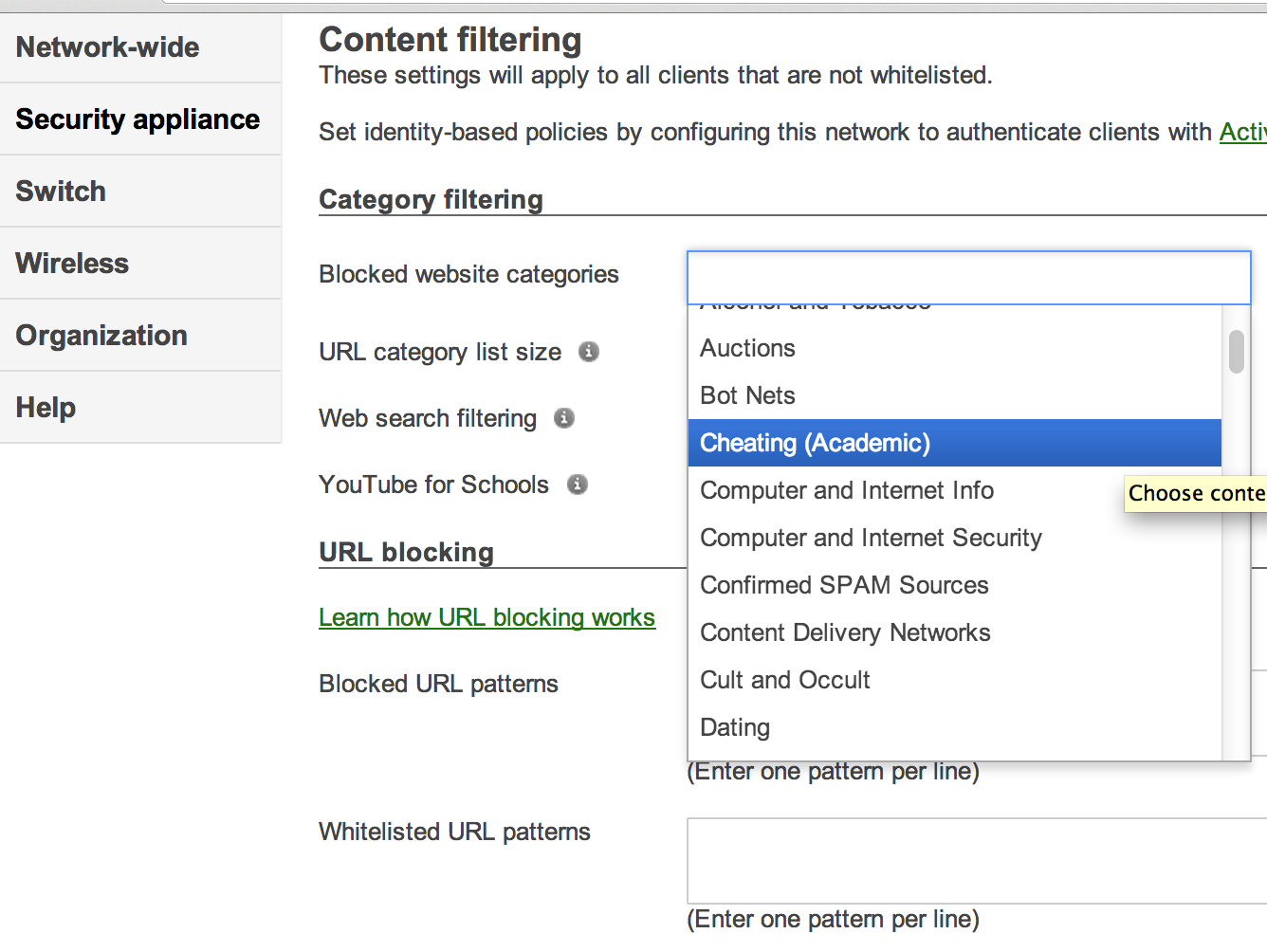 Meraki MX60 Content Filtering Options
Meraki MX60 Content Filtering Options
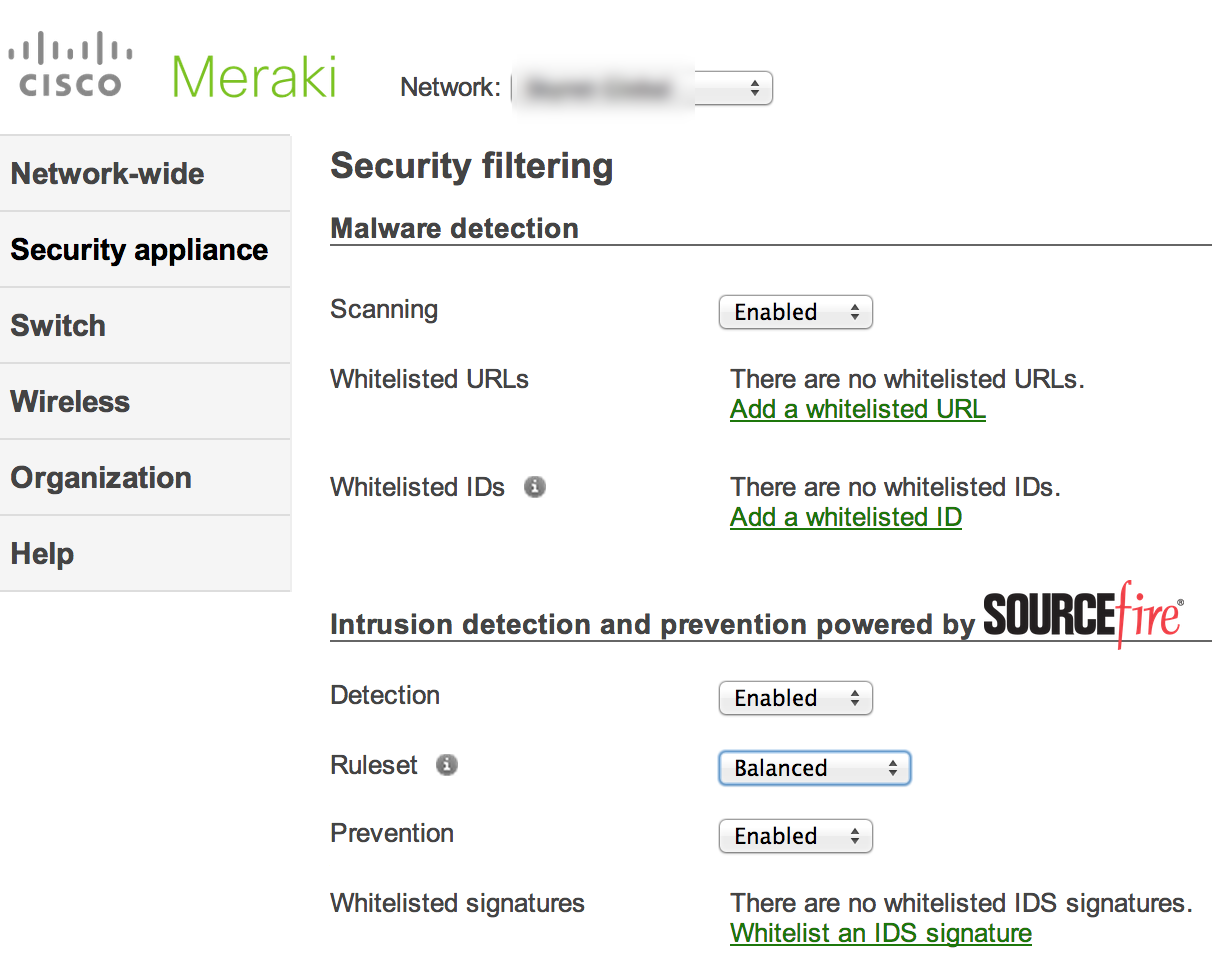
The Meraki MX60 uses SourceFire / SNORT rules for the IPS. Its explained as “Security filtering is comprised of the Kaspersky® SafeStream anti-virus / anti-phishing engine and Sourcefire SNORT intrusion detection engine.” There isn’t a lot of tuning options regarding the available signatures however whitelisting is pretty easy to do. There are only a few ruleset options such as secure or in the next example, balanced. What each security setting really means is explained HERE.
Malware Detection and IPS For The Meraki MX60
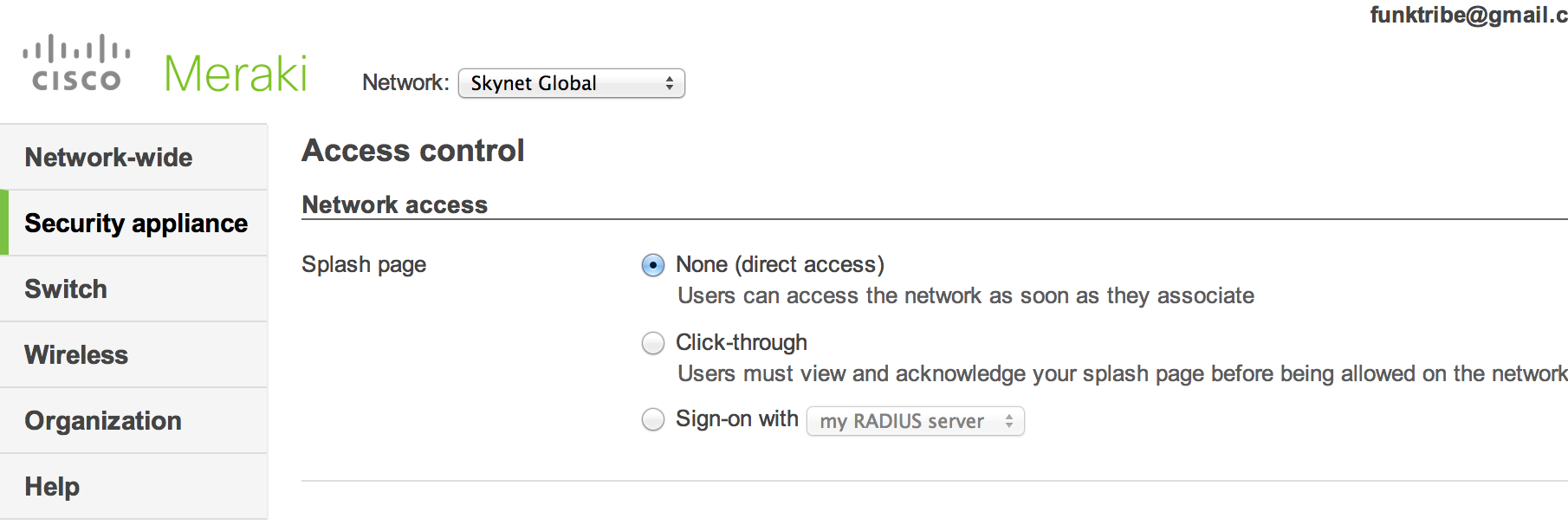
The MX60 offers decent VPN and access control options. Both are pretty easy to setup. Regarding access control, users can authenticate using single sign on or prompted to enter credentials such as a Active Directory login. Administrators can also enforce a acknowledgment page with spooky legal information prior to permitting access.
Overall, the Meraki series is easy to use and very feature rich for the price. The MX60 list price is $495 giving you Firewall, IPS, VPN, Application Layer Controls, Traffic Filtering, WAN optimization and more. Many of these features are only found on mid market to enterprise level security solutions making this series a great value for those seeking high in security for small breach office or home use. Check out Meraki’s website as well as attend a weekly webinar to get a free access point. Most people I know that get an Maraki AP convert their home networks once they see how easy it is to setup and use.
Also check out my post on free Meraki mobile device management MDM HERE.



The problem I have with Meraki’s devices, is that when these security services are turned on the throughput is atrocious. I bought an MX60W to try out, as I was considering a change in my preferred hardware vendor, and the throughput is so bad I ended up unplugging it after just a few days’ use. Todays broadband internet connections at remote users’ homes (what this device is aimed toward) are sometimes as high as 150 mbps. If you send one of these home with a user and they don’t get over 10, they are not going to be happy.
Just curious, what model do you have? I had a older small one (z series) and it was slow so went back to my old network. I have a newer Meraki mx and the performance is much better. I’m also not doing things like content filtering, etc to slow things down because … well … I’m not going to limit my own traffic so performance seems fine. Thats my experience with it thus far
The meraki are great for cloud based and vpn management but as an enterprise product they are far from it. The biggest failing they have in my books is their Traffic Shaping and bandwidth management. Their whole design works off creating traffic shaping rules at a user level and have no global control at a link level, i.e. 10 users can each have 2Mb/s download and 1Mb/s Upload, you can then add rules to say voip has priority, facebook is limited to 50% of that bandwidth, BUT you can’t give your 10 users each 2/1 and then set a global limit of say 5/2 on all HTTP/HTTPS traffic as not to saturate your link with people surfing the net and leave bandwidth for other applications like voip and video conferencing.
In a real world situation a remote site with a MX60, but due to technology limitations you can only get a 2M/2M link and you have 20 remote users that all need to be functional. The Meraki fell on it’s face with constant complaints from users and slow usage, I couldn’t give them all 100/100kb/s link speeds and reserve some for voip, smtp and dns sync, thats not a useable environment.
I loved the cloud management and vpn setups so I wanted to keep using the Meraki, my solution which is working like a dream. Turned off all traffic shaping in the Meraki and brought a $120 Mikrotix (Routerboard) RB450G and set it up as an invisible bridge and put it between the Meraki LAN port and the local Network. It does all the traffic shaping before handing off to the Meraki, no more user complaints.
Meraki assumes you will always have huge links with more than enough bandwidth for all your users, this is not real world thinking and will limit their roll out beyond urban and industrial business centers and really can’t be used in multinationals with branch offices in less technologically advanced countries.
As for the limitations of the Z1, 5 user limitation for a satellite office in a world where almost everyone has a PC/Laptop/smart phone/ tablet/ network printer with scan to email devices, then you throw in VOIP, real world test of this had my user getting kicked off randomly when everything was turned on (tablet and phones polling the internet), let alone the satellite office gets a work visitor. Set it up for a user to take it home as their satellite office and you have the wifes & kids phone/tablet, smart tv’s and PVR for net streaming. The Z1 should be 10 user at a minimum.
Meraki have some real world design and implimentation thinking to do.
Hi James. Yes I would agree that Meraki has its place. For large enterprises, I would recommend a Sourcefire appliance or Ironport WebSecurity Appliance over Meraki. There are some good fits for Meraki however such as small to medium businesses. Also, some use cases such as a large retail chain needing security at multiple locations would be ideal for Meraki. Reason why is they can purchase a ton of MX appliances, configure them before they ship so when they arrive, they are plug and play ready.
There are some enterprises using Meraki so your points are valid for certain use cases while others may make sense for Meraki. Hope this helps. Thanks for the feedback.
We are a small/medium business…. The ONLY thing going for Meraki is the pre config before shipping.
The only thing I could do to actually use the investment in our Meraki equipment (before they turn into paperweights when the subscription ends, unless I can resell them). Is to turn them into dumb IPSec Managers and put another router in front of them acting as a bridge and do traffic shaping and add additional links to manage and load balance bandwidth.
Hi, we are looking into a mx80. The mx range is 4 years old unless they have silently updated the hardware. Does anyone know if they are due an upgrade?
The MX60 was replaced by the MX64 and MX64W. They have some decent throughput increases and is very similar to the MX80, however, VPN tunnels are at 25 vs 50 on the MX80.
A little known fact is that a lot of routers today are still running off of very dated technology. The Juniper SSG-550M, for example, is running off Pentium 4 Prescott CPUs with 512MB of ram.
Merakis are probably a SoC setup with whatever current hardware was when the unit was first prototyped. So it’s understandable that these appliances can be slightly limited in overall performance. However, the feature sets are quite amazing for the price and management interface which totally offsets any issues you might have with performance.
When in doubt, I would get the larger unit and the 5yr license. A lot of people will size their first office security appliances in a 1yr or 3yr scale. Looking ahead and getting larger earlier will reduce the downtime of upgrading the box later on. We have to consider the lifecycle on these units is roughly that long as well. It’s good to coincide your purchases to whenever Meraki releases a new product in your class.
Necro Thread Resurection:
The MX60 and MX60W are using some variant of the Power4 Architecture by Applied Micro. It’s a new implementation of an old standard. They are actually quite quick for their power consumption.
If you have some old ones laying around you can make a pretty nice standalone router with a few minutes of tinkering and a little bit of hardware knowledge.
https://openwrt.org/toh/meraki/mx60
I have two units “in production” running a recent build of Openwrt, both are rock solid and quite fast even with OpenVPN and a bunch of other services running.