Interesting flaw in apt-get utility based on a HTTP vulnerability that permits a man-in-the-middle-attack. The original post from thehackernews can be found HERE.
Some cybersecurity experts this week arguing over Twitter in favor of not using HTTPS and suggesting software developers to only rely on signature-based package verification, just because APT on Linux also does the same.
Ironically, a security researcher just today revealed details of a new critical remote code execution flaw in the apt-get utility that can be exploited by a remote, man-in-the middle attacker to compromise Linux machines.
The flaw, apparently, once again demonstrates that if the software download ecosystem uses HTTPS to communicate safely, such attacks can easily be mitigated at the first place.
Discovered by Max Justicz, the vulnerability (CVE-2019-3462) resides in the APT package manager, a widely used utility that handles installation, update and removal of software on Debian, Ubuntu, and other Linux distributions.
According to a blog post
published by Justicz and details shared with The Hacker News, the APT
utility doesn’t properly sanitize certain parameters during HTTP
redirects, allowing man-in-the-middle attackers to inject malicious
content and trick the system into installing altered packages.
APT HTTP redirects help Linux machines to automatically find suitable
mirror server to download software packages when others are unavailable.
If the first server somehow fails, it returns a response with the
location of next server from where the client should request the
package.
“Unfortunately, the HTTP fetcher process URL-decodes the HTTP Location header and blindly appends it to the 103 Redirect response,” Justicz explains.
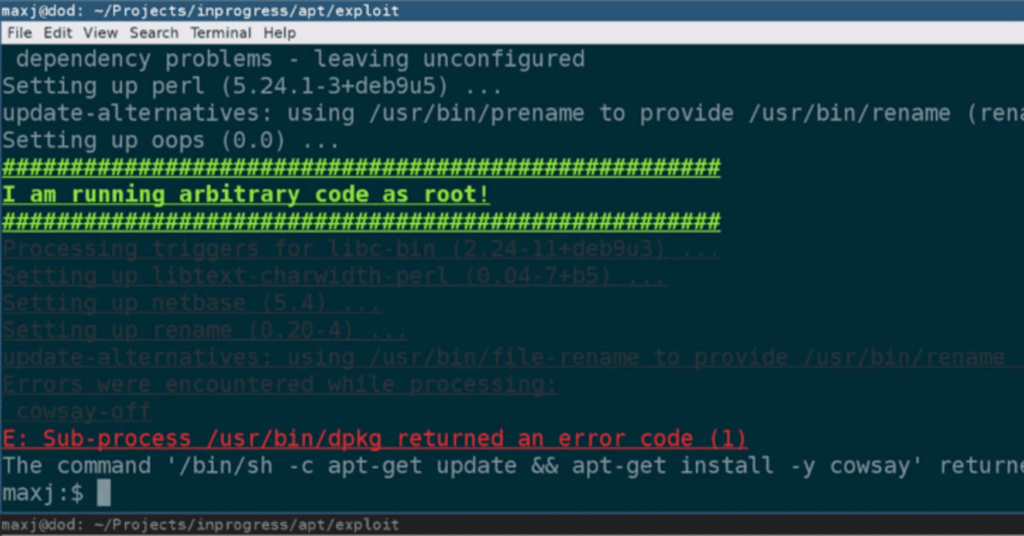
As shown by the researcher in a video demonstration shared with The Hacker News, an attacker—intercepting HTTP traffic between APT utility and a mirror server, or just a malicious mirror—can inject malicious packages in the network traffic and execute arbitrary code on the targeted system with the highest level of privileges, i.e. root.
“You can completely replace the requested package, as in my proof of concept. You could substitute a modified package as well, if you wanted to,” Justicz told THN.
Though Justicz has not tested, he believes the vulnerability affects all type of package downloads, even if you are installing a package for the very first time or updating an old one.
No doubt, to protect the integrity of the software packages, it’s important to use signature-based verification, as software developers do not have control over mirror servers, but that doesn’t mean one should ignore benefits of using HTTPS protocol over the complexity of infrastructural upgrades in some particular cases.
No software, platform or server can claim to be 100% secure, so adopting
the idea of defense-in-depth is never a bad idea to consider.
It should also be noted that cybersecurity experts do not expect
organizations or open-source developers to implement HTTPS overnight,
but they should also not even reject the defensive measures completely.
“By default, Debian and Ubuntu both use plain http repositories out of the box (Debian lets you pick what mirror you want during installation, but doesn’t actually ship with support for https repositories – you have to install apt-transport-https first),” the researcher explains.
“Supporting http is fine. I just think it’s worth making https repositories the default – the safer default – and allowing users to downgrade their security at a later time if they choose to do so.”
The developers of APT software have released updated version 1.4.9 to fix the reported remote code execution vulnerability.
Since apt-get is part of many major Linux distributions including Debian and Ubuntu, who have also acknowledged the flaw and released security updates, it is highly recommended for Linux users to update their systems as soon as possible.