Cisco’s research group Talos posted new findings on the latest version of the Locky ransomware. For those that are not familiar with Locky ransomware, its malicious code typically delivered through email. Opening the email will infect the host with ransomware that will encrypt all personal data and hold it for a bitcoin ransom.
This post reviews the distinct characteristics of each Locky ransomware family campaign so you can better understand how these email attacks are being delivered. The original post can be found HERE.
SUMMARY
We had .locky, we had .odin and then we had .zepto but today we hit rock bottom and we now have Locky using .shit as their encrypted file extension. In today’s latest wave of spam, Talos has observed three distinct spam campaigns distributing the newest version of Locky ransomware. This comes after a seeming vacation for Locky for around two weeks. Using the LockyDump utility that was previouslyreleased by Talos, we were able to determine that there are distinct differences in the characteristics of the malware campaigns that seem to correlate with the Affiliate ID associated with the Locky binaries that are delivered by each campaign.
The technical details associated with the Locky ransomware family itself has been extensively documented and reported on, so we won’t spend time providing an in-depth technical analysis of the ransomware family itself. This post highlights some of the distinct characteristics that we have observed for each campaign. We will summarize all Indicators of Compromise (IOCs) at the end of this post.
CAMPAIGN DETAILS
Campaign 1: “Receipt XXX-XXX” Spam (Affil ID=3)
This campaign was first observed this morning (2016-10-24) and featured emails attempting to leverage malicious .HTA files as malware downloaders. The emails are encouraging the recipient to open the message claiming they contain a receipt. The emails associated with this campaign used the subject “Receipt XXX-XXX” where XXX was a sequence of numbers. These HTA files were encapsulated in .ZIP archives named “Receipt XXX-XXX.zip”. The .HTA file is named “Receipt XXXXX-XXXXXX.hta” and when opened, functions as a malware downloader for the actual Locky ransomware.
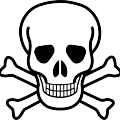
Interestingly enough, the obfuscation employed by the .HTA downloader contained repeated use of variable names that were based on the word “PUMPKIN”. In the samples we analyzed, “PUMPKIN” showed up in 37 separate instances. This is a timely reference with Halloween rapidly approaching.
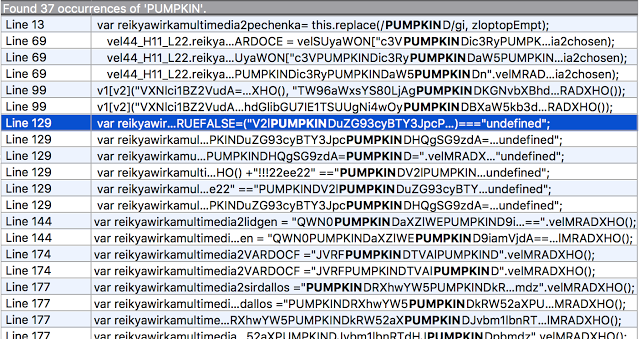 Figure A: References to ‘PUMPKIN’ in HTA Downloader
Figure A: References to ‘PUMPKIN’ in HTA Downloader
 Figure B: LockyDump Output For Sample
Figure B: LockyDump Output For Sample
Campaign 2: “saved_letter_XXXXXXXX” Spam (Affil ID=1)
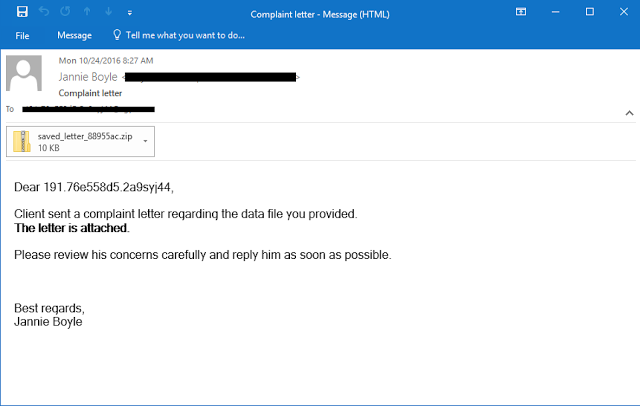 Figure C: Sample Complaint Email Message
Figure C: Sample Complaint Email Message
Campaign 3 – Various Spam, namely ‘Free’ (Affil ID=3)
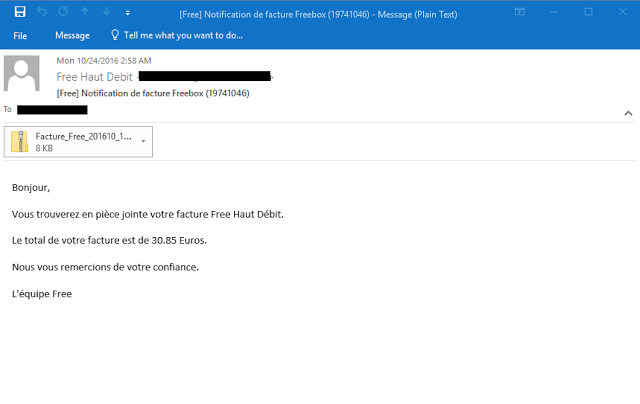 Figure D: Sample “Free” Email Message
Figure D: Sample “Free” Email Message
Subject: We could not deliver your parcel, #000990048
Subject: Unable to deliver your item, #0000248834
Subject: Problem with parcel shipping, ID:00480186
These all followed the normal Locky distribution method of .ZIP attachments which contained .WSF malware downloaders. We believe this third campaign is a small test campaign as the attachments appear to be corrupt in some instances. The messages outside of the “Free” spam campaign all had broken .ZIP attachments which contained files with the double-extension of “.doc.wsf”, none of which are valid. It’s rare for spam campaigns attempting to distribute Locky downloaders to have a high percentage of corrupt attachments.
Changes to Locky
- URL path used to for C2 has changed to /linuxsucks.php.
- The file extension used when encrypting files has changed to “.shit”
- The file containing the ransom note is now named “_WHAT_is.html”
INDICATORS OF COMPROMISE
Campaign 1:
We have included all 210 unique sample hashes for this campaign here
Campaign 2:
We have included all 388 unique sample hashes for this campaign here
Campaign 3:
We have included all 42 unique sample hashes for this campaign here
COVERAGE
Additional ways our customers can detect and block this threat are listed below. 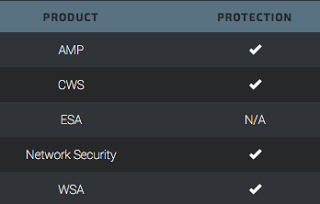 Advanced Malware Protection (AMP) is ideally suited to prevent the execution of the malware used by these threat actors.
Advanced Malware Protection (AMP) is ideally suited to prevent the execution of the malware used by these threat actors.
ESA can block malicious emails sent by threat actors as part of their campaign.