Authentication is a critical security topic many administrations overlook. You can build layers of security however inadequate authentication methods can lead to sensitive information being compromised. Calculating investments in authentication should be comparable to costs of loosing critical data, which for most organizations is VERY expensive. It baffles me when stakes are high yet agencies don’t invest in authentication solutions. A well rounded authentication architecture should include multi-factor authentication and leverage user identity for access control to the network, device management and physical access to locations with critical infrastructure.
Authentication is a critical security topic many administrations overlook. You can build layers of security however inadequate authentication methods can lead to sensitive information being compromised. Calculating investments in authentication should be comparable to costs of loosing critical data, which for most organizations is VERY expensive. It baffles me when stakes are high yet agencies don’t invest in authentication solutions. A well rounded authentication architecture should include multi-factor authentication and leverage user identity for access control to the network, device management and physical access to locations with critical infrastructure.
All standard password policies are or will eventually be vulnerable due to advances in technology. I wrote a blog on this subject HERE. Multifactor authentication is critical and can be accomplished leveraging a combination of something you have, know and are. Common solutions range from physical cards (CAC/PIV) mixed with pins, physical or soft tokens that generate random numbers mixed with passwords to hidden certificates on devices. Best practice is to leverage encryption and data loss prevention technology that locks out access after a specific number of failed attempts.
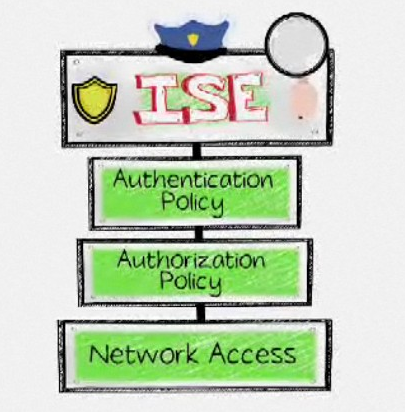
 Advanced Access control solutions are becoming popular and based around authentication. Access control methods such as port security and whitelist technology lack considering user identity for authentication, which increases risks of bypassing security using spoofing or other technics. Manual access control methods are also difficult to manage. The latest access control technologies use multiple forms of authentication to determine whom, what and how much risk is associated with devices accessing the network. A strong authentication foundation can be built into an access control deployment by leveraging a combination of factors to determine how network resources are provisioned. An example is treating employees with iPads connecting wirelessly different than employees with cooperate issued devices accessing the LAN.
Advanced Access control solutions are becoming popular and based around authentication. Access control methods such as port security and whitelist technology lack considering user identity for authentication, which increases risks of bypassing security using spoofing or other technics. Manual access control methods are also difficult to manage. The latest access control technologies use multiple forms of authentication to determine whom, what and how much risk is associated with devices accessing the network. A strong authentication foundation can be built into an access control deployment by leveraging a combination of factors to determine how network resources are provisioned. An example is treating employees with iPads connecting wirelessly different than employees with cooperate issued devices accessing the LAN.
Device management should include individual authentication rather than default administration accounts. Many network problems are caused by administration mistakes that could be avoided if proper polices for configuration change management are enforced. Using one account for all administration control to devices removes the ability to enforcing role-based access control, assign accountability and restrict access due to termination or loss of privileges without changing all access passwords.
 Physical protection to data centers with sensitive data should leverage strong authentication. People are your weakest link and typically will not question somebody who looks like they belong in a data center or walking out the door with a cooperate laptop. I’ve had coworkers compromise networks during approved penetration exercises by walking into a data center and borrowing people’s passwords using social engineering tactics. Best practice to avoid this attack vector is including multiple authentication factors for physical access to areas containing critical information. Physical access should control who enters and leaves specific areas. It’s also wise to track mobile devices with critical data in a protected area with RFID technology that sets off alarms when devices are moved from a specific zone. These tactics won’t completely remove risk however increase suspicion when unauthorized uses request multiple forms of lost authentication data or attempt to remove devices from your data center.
Physical protection to data centers with sensitive data should leverage strong authentication. People are your weakest link and typically will not question somebody who looks like they belong in a data center or walking out the door with a cooperate laptop. I’ve had coworkers compromise networks during approved penetration exercises by walking into a data center and borrowing people’s passwords using social engineering tactics. Best practice to avoid this attack vector is including multiple authentication factors for physical access to areas containing critical information. Physical access should control who enters and leaves specific areas. It’s also wise to track mobile devices with critical data in a protected area with RFID technology that sets off alarms when devices are moved from a specific zone. These tactics won’t completely remove risk however increase suspicion when unauthorized uses request multiple forms of lost authentication data or attempt to remove devices from your data center.
Best practice for authentication is consolidating all authentication solutions for physical and logical access into a centralized solution. This simplifies controlling and monitoring who is accessing what data based on location and logical authorization. An example is using a CAC card mixed with pin to access a data center, which also is one of the factors required to log into a router or laptop for accessing the network. There isn’t one vendor that offers a single authentication solution for all access vectors so it’s recommended to speak with a trusted security consultant to assist building your authentication architecture.