Bleeping computer posted about an increase in code phishing attacks HERE. I completely agree these attacks are popular and hitting organizations I work with. To summarize how this works, I’ll pull from the Bleeping computer post (see the full post for details)
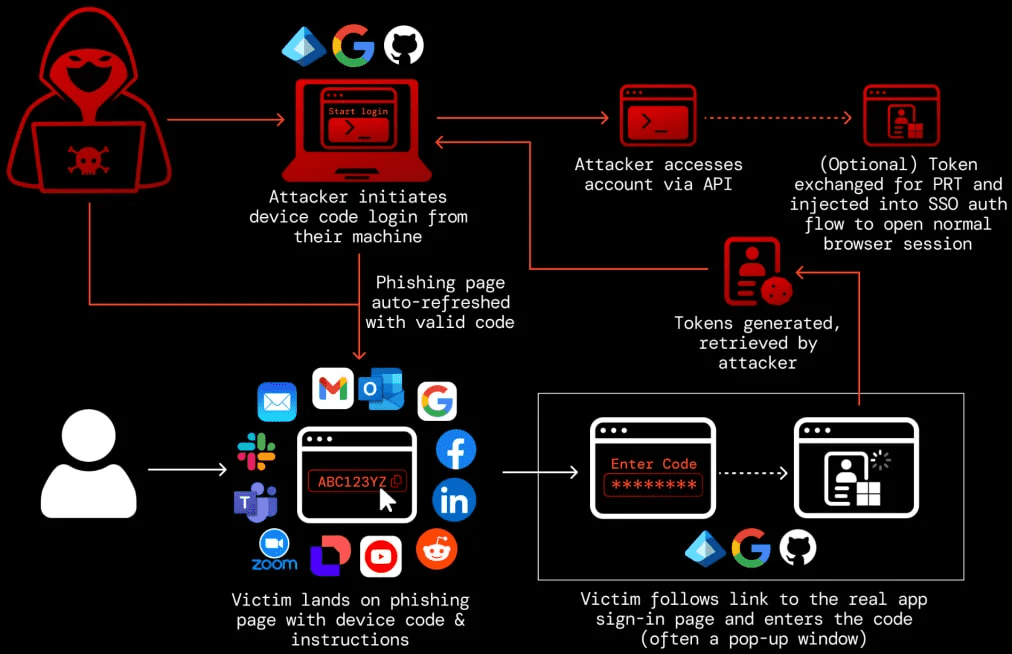
In this type of attack, the threat actor sends a device authorization request to a service provider and receives a code, which is sent to the victim under various pretexts.
Device code phishing attacks that abuse the OAuth 2.0 Device Authorization Grant flow to hijack accounts have surged more than 37 times this year.
Next, the victim is tricked into entering the code on the legitimate login page, thus authorizing the attacker’s device to access the account through valid access and refresh tokens.
Here is a diagram
How do you defend against this type of attack. If I had to choose one capability, I would recommend good old risk based conditional access controls. By checking if a device is corporate issued, where its located, does it have specific security parameters running, etc., a threat actor with stolen credentials would not be able to pass the additional conditional access policies. This technology has been around and offered by a handful of vendors.
There are other layers of defenses including what some believe is critical (but I don’t think is a top suggestion) …. user training. I’m part of the camp that assumes users will get tricked regardless how well trained they are. In the world of AI, phishing is becoming really hard to detect. I believe we are moving towards a world that you could get on a video conversation with a threat actor or AI and believe you are talking to somebody you work with. My thought is including phishing defense and training but assume users will be tricked.
Check out the article to learn more about this phishing attack. Phishing continues to be the number one threat vector and this approach is common today.