I have had a few people ask me what to expect when upgrading their Cisco Firepower deployments from 5.4 to 6.0. I went ahead and upgraded both my ASA 5506x using ASDM and ASA 5512x using the FireSIGHT centralized manager. Here is a breakdown of my experience. I also posted about the new Firepower 6.0 features HERE.
First off, it is important to always read the documentation when you perform a upgrade. One major item that isn’t made clear in the release notes is the fact that Cisco Firepower 6.0 doesn’t support FireSIGHT high availability. This means if you have two managers configured in a HA cluster, you should stay on 5.4 and wait for the 6.01 patch scheduled to be released shortly.
If you decide to upgrade to 6.0, the first step is to download the appropriate upgrade file. You will not find the file under ASDM or FireSIGHT when going to the upgrade section and clicking the download updates button. That button is for minor release updates such as 5.4.0 to 5.4.1. You must download 6.0 directly from Cisco.com and upload it as I’ll be showing in this post. You will see in my ASA5506x example that I used the download updates button to go from 5.4.1 to 5.4.3 before uploading the 6.0 file I obtained from Cisco.com.
FireSIGHT Virtual Manager 5.4.1 Upgrade To 6.0
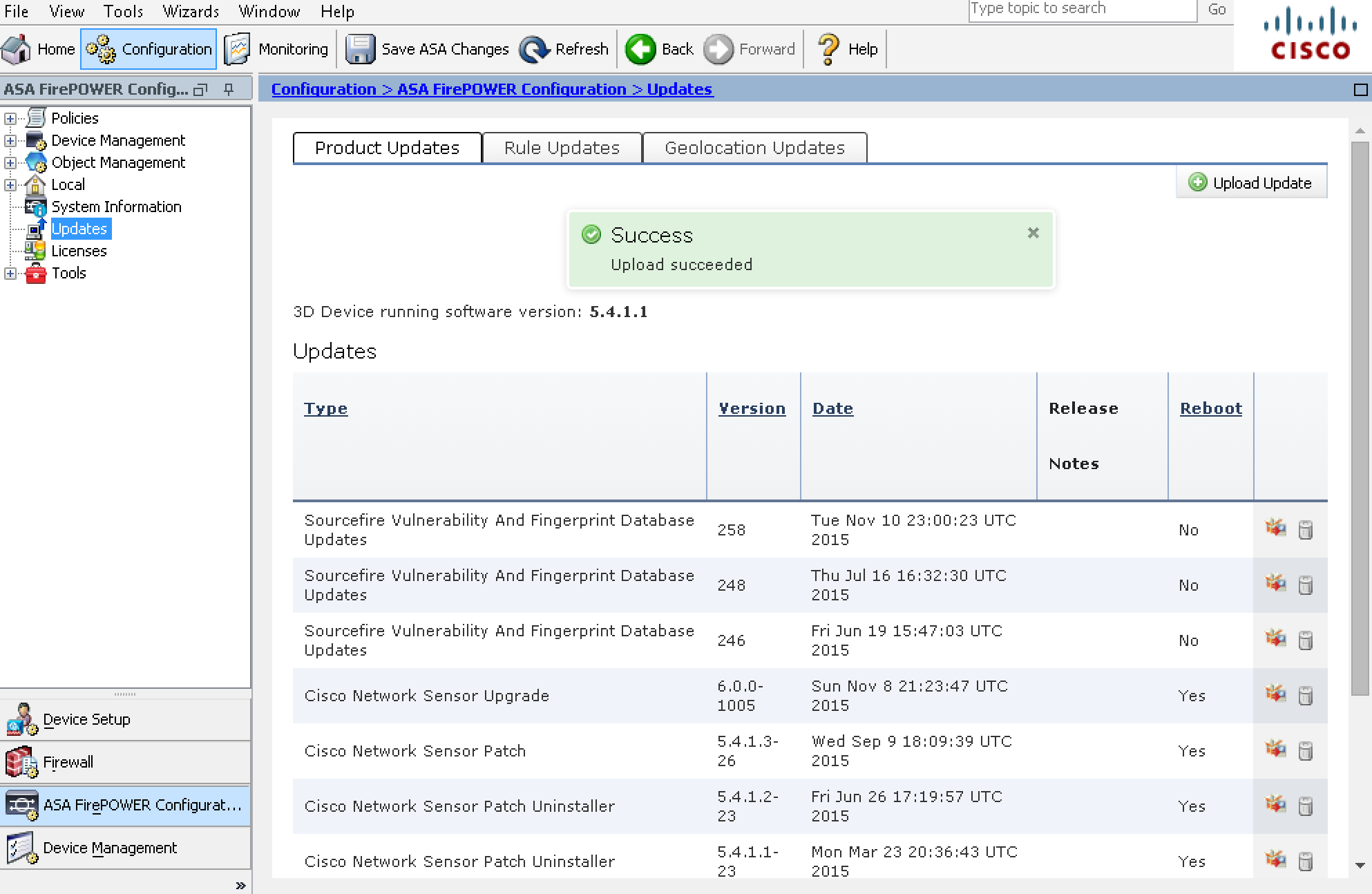
I started off upgrading my FireSIGHT manager. This means I needed the FireSIGHT 6.0 upgrade file called Sourcefire_3D_Defense_Center_S3_Upgrade-6.0.0-1005.sh. The file is pretty big so it took almost an hour to download. Once downloaded, I logged into my FireSIGHT manager, clicked updates and selected to upload this file. Once uploaded, it appeared as a upgrade option as shown in the next image.
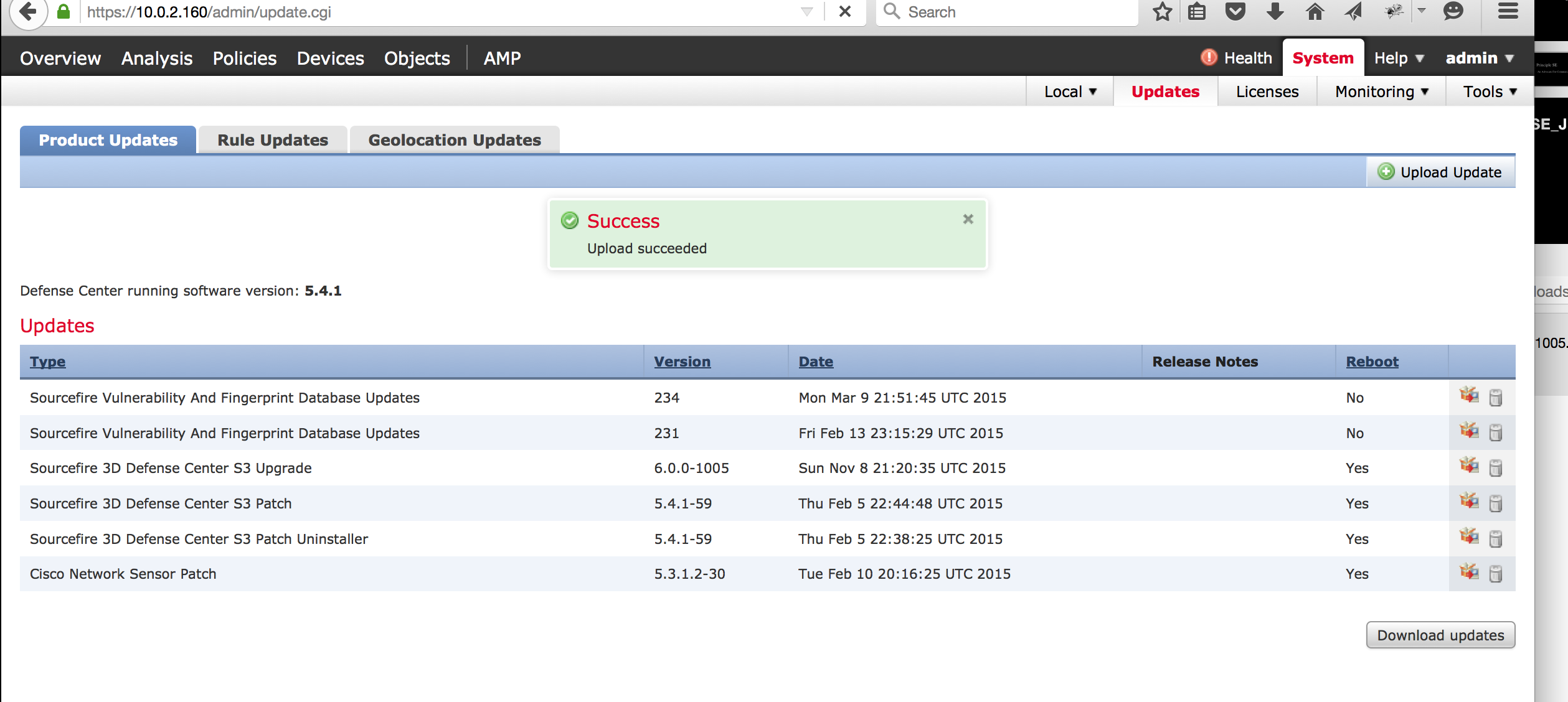 Next I selected the package image next to the 6.0 update that states a reboot will be required followed by YES. If the file is corrupt, you will get a corrupt message when you attempt to launch the upgrade (I had that happen in the past). If the upgrade file is good, you will see the install page as shown.
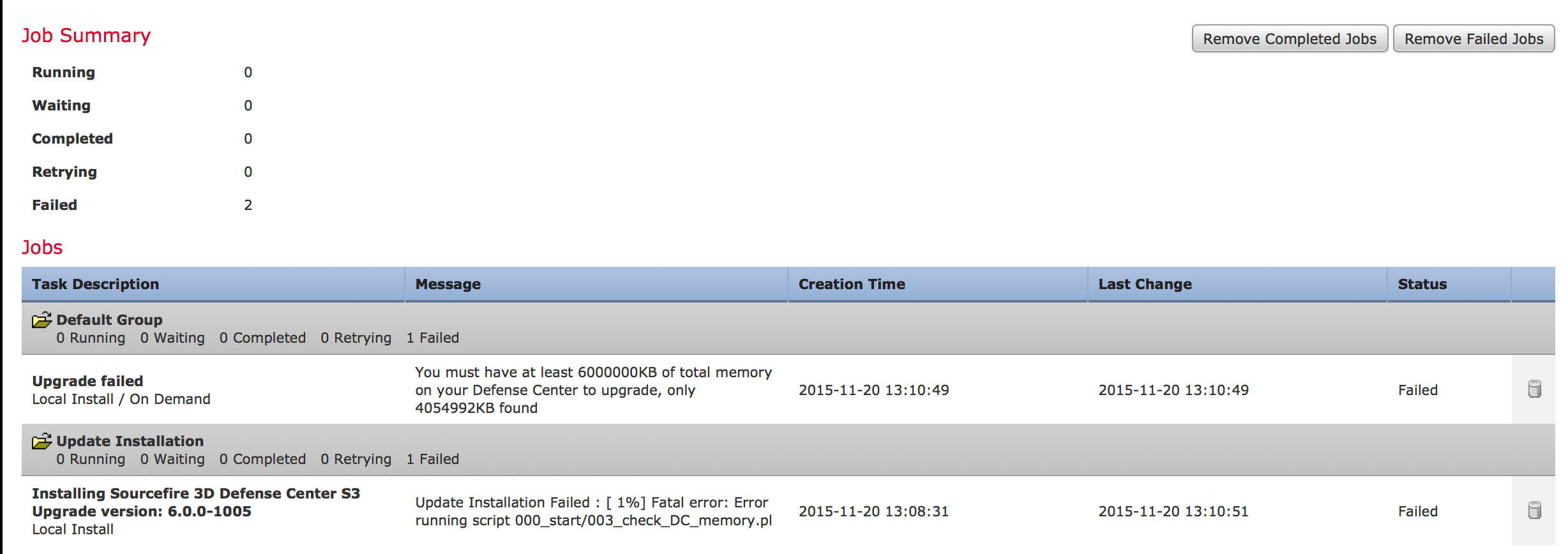
Next I selected the package image next to the 6.0 update that states a reboot will be required followed by YES. If the file is corrupt, you will get a corrupt message when you attempt to launch the upgrade (I had that happen in the past). If the upgrade file is good, you will see the install page as shown. 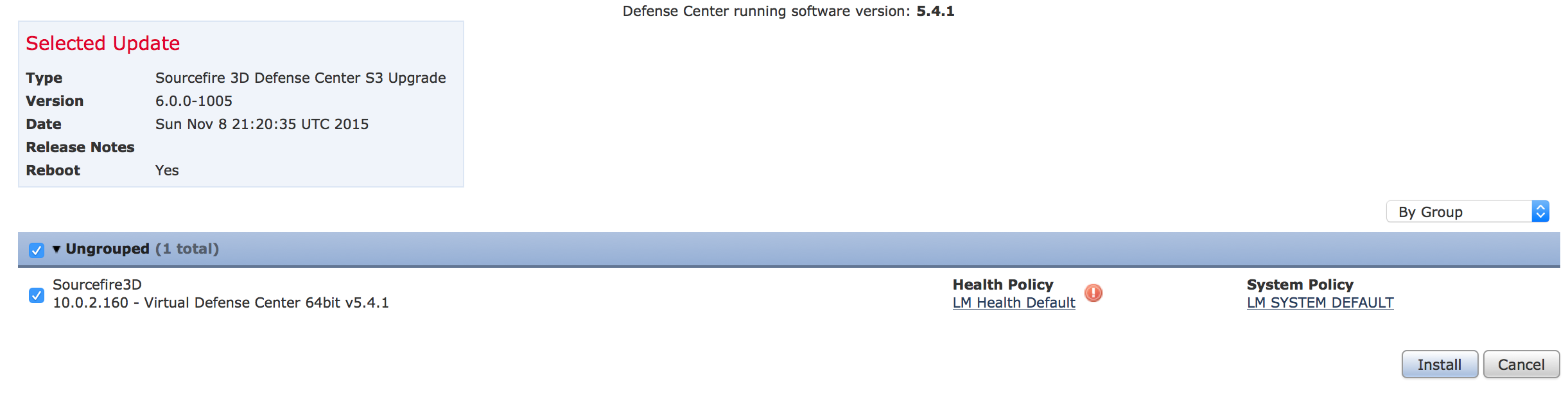 The first attempt I made failed because my FireSIGHT VM didn’t have enough memory. I found out by clicking the running task menu after I launched the upgrade and saw my upgrade task failed as shown. BUMMER. So I had to shutdown my FireSIGHT VM, add more memory, fire it back up and go through the launch process again.
The first attempt I made failed because my FireSIGHT VM didn’t have enough memory. I found out by clicking the running task menu after I launched the upgrade and saw my upgrade task failed as shown. BUMMER. So I had to shutdown my FireSIGHT VM, add more memory, fire it back up and go through the launch process again.
 This time it worked. After the upgrade task completed, my system rebooted. Now my manager was running FirePOWER 6.0 so I was ready to move on to my ASA 5512x running FirePOWER 5.4.1and upgrade that to 6.0 since its managed by this FirePOWER manager.
This time it worked. After the upgrade task completed, my system rebooted. Now my manager was running FirePOWER 6.0 so I was ready to move on to my ASA 5512x running FirePOWER 5.4.1and upgrade that to 6.0 since its managed by this FirePOWER manager.
ASA5512X FirePOWER 5.4.1 to 6.0 Upgrade
Next I upgraded my 5512X that is being managed by the FireSIGHT manager.
NOTE: A FireSIGHT manager can only manage one version older than the version its running. If my FirePOWER version on the 5512x was 5.3 or lower, my FireSIGHT manager would no longer be able to manage it. Once again, it is important to read the release notes, which states to upgrade all FirePOWER appliances to 5.4 before taking your manager to 6.0. So at this point, my FireSIGHT manager is running 6.0 and my ASA 5512x is running FirePOWER 5.4.3.
To start the upgrade process, I downloaded the ASA5512x Firepower 6.0 upgrade file from cisco.com.  Next I went under updates, and selected upload to upload this file. Once uploaded, I selected the package next to the upgrade file to start the upgrade process just like I did with the manager. It took around 40 minutes for the upgrade to complete. So at this point, my FirePOWER manager and sensor were both at 6.0. My last project was upgrading my stand alone ASA5506x to FirePOWEr 6.0.
Next I went under updates, and selected upload to upload this file. Once uploaded, I selected the package next to the upgrade file to start the upgrade process just like I did with the manager. It took around 40 minutes for the upgrade to complete. So at this point, my FirePOWER manager and sensor were both at 6.0. My last project was upgrading my stand alone ASA5506x to FirePOWEr 6.0.
ASA 5506 FirePOWER ASDM Upgrade
Now to switch gears, I decided to upgrade my ASA 5506X running FirePOWER 5.4.1 to FirePOWER 6.0 using ASDM verses the centralized manager. Note that I could use my centralized manager to accomplish the same thing however I decided to test the upgrade processing using ASDM. Also note that only the ASA 5506x, ASA 5508x and ASA 5516x running 5.4.1 have FirePOWER options within ASDM. All other versions of ASAx appliances will have FirePOWER options added to ASDM once they are running FirePOWER 6.0. For example, my ASA 5512x running FirePOWER 5.4.1 did not have FirePOWER management options in ASDM. I had to use a FireSIGHT manager to upgrade to 6.0. Now that the 5512x is running FirePOWER 6.0, I can log into ASDM and there are options to view the status of the FirePOWER services. NOTE though that they will not be available if the ASAx appliance has its FirePOWER stuff managed by a centralized manager. You have to disassociate it and manage the FirePOWER features by itself with ASDM to see configuration options.
So the first step is to log into ASDM and click the configuration tab. If your FirePOWER features are running, you should see the FirePOWER tab options on the left hand side. Before moving forward, I found my core ASA and ASDM were a few versions behind so I use the ASDM upgrade wizard that leverages my Cisco CCO directly from Cisco.com to upgrade both of these. That upgrade took around 15 minutes to complete. Now my ASA was on the latest core ASA code (9.5) and ASDM was on the latest version.
Next I downloaded the file from cisco.com. Once the file downloaded, I went in ASDM, I went under the Configure tab, selected the FirePOWER tab on the left, selected updates and upload to upload the upgrade file. This looked the same as when uploading the upgrade file to the centralized FirePOWER manager. The next screenshot shows the 6.0 upgrade file added in ASDM.
 I attempted to apply the update however found I was running FirePOWER 5.4.1 on my ASA5506x. This gave me a error message asking that I first upgrade to 5.4.3. BUMMER. I clicked “download upgrades“, which automatically pulled the 5.4.3 file. I applied that upgrade and waited 40 minutes for the upgrade to complete. After a few minutes post reboot, my ASA5506x was now running FirePOWER 5.4.3. I once again attempted to apply the 6.0 upgrade and this time it moved forward. Again, it took around 40 minutes and after the reboot I had my ASA5506x running FirePOWER 6.0.
I attempted to apply the update however found I was running FirePOWER 5.4.1 on my ASA5506x. This gave me a error message asking that I first upgrade to 5.4.3. BUMMER. I clicked “download upgrades“, which automatically pulled the 5.4.3 file. I applied that upgrade and waited 40 minutes for the upgrade to complete. After a few minutes post reboot, my ASA5506x was now running FirePOWER 5.4.3. I once again attempted to apply the 6.0 upgrade and this time it moved forward. Again, it took around 40 minutes and after the reboot I had my ASA5506x running FirePOWER 6.0.
So that is all there is too it. Another option to get to FirePOWER6.0 is doing a new install as explained in this post HERE. Note if you go this route, all default passwords are user name admin and password Admin123. They removed all of the “sourcefire” passwords with 6.0. Hope this helps with your upgrade plans.





Hey Joseph, thanks for the concise instructions – it is posts like this that make Cisco upgrades go that little bit easier! Well done.
Ps. Website bookmarked.
James
You mention that “the 6.01 patch scheduled to be released shortly” will support Defense Center HA. Can you confirm this? Cisco support will only say that Defense Center HA will be re-introduced at a later time, which may be late 2016.
I can’t officially post the release date but expect it very early 2016.
…and never forget to change your HTTPS certificate if you have higher then SHA256 and RSA2048 hash or bit…. it will upgrade but you cannot longer login to the webinterface after restart.
Thank you very much for sharing this.
Is it okay to download version 6 upgrade files from Sourcefire support site ?
https://support.sourcefire.com/sections/1
I had tried to download the files several times but fails after some time.
You should be ok doing this however I believe they are taking down that site this summer. They want you to use Cisco.com via having a CCO account to get these files. A CCO account is free to get so at some point, you probably want to do that. This also is important since a lot of the technology such as the new unified 6.0.1 image requires SMART licensing. Hope this helps
Hi everyone.
when I upgrade firesight from version 5.4.1 to 6.0.0 have Error:
Info
No valid appliances available for Sourcefire 3D Defense Center S3 Upgrade 6.0.0-1005
This update is intended for software versions greater than or equal to 5.4.1 and less than 6.0.0-1005
Plz tell me how to solved problem.
Thanks!
Hi Cuong. I experienced something similar to this when I tried to use the GUI to upgrade my firepower 6.0.0.1 to 6.0.1 unified image found in todays blog post here https://www.thesecurityblogger.com/upgrading-to-firepower-unified-6-0-1/. My understanding is if FirePOWER manager doesn’t see a system that is supported by the install you are looking to use, you will get that message. For example, if you try to install the separate 6.0.1 upgrade on a sensor that is not running 6.0.0.1, you will see the same message until you upgrade that sensor to 6.0.0.1. So most likely, your 5.4.1 is either not the latest 5.4.1, you are not seeing connectivity in the manager to the sensor (if this was a sensor upgrade verse manager upgrade), the upgrade file is corrupted, or you downloaded the wrong upgrade file (maybe the physical box verse virtual upgrade file). My suggestion is try following my blog to get to 6.0.1. Worst case, build a new 6.0.1, get it up and running like your 5.4.1 then migrate systems over. NOTE NOTE NOTE … Firepower only supports one version back for management meaning if your sensors are running 5.4.1, your manager running 6.0.1 may think they are too old (haven’t tested this yet so not sure. It may be ok until 6.1 but again not sure). Hope this helps
Has anyone ‘successfully’ upgraded a 5506X (in particular) from 5.4.1 to 6.0.1 ? (Source Fire)
I tried it and it failed,,, miserably,,, in fact I never got the SFR module back up again, it always showed as Unresponsive.
Long story short,,, I send back the ASA & got a replacement. The 1st ASA was a V01 and my replacement is a V02.
I’m a little gun shy to try it again on my replacement.
My thought was to replace 5.4.1 with 6.0.1 instead of going through an upgrade process.
Maybe that’s where I/it failed??
Any experiences either way ?
Thanks in advance
Check out my post on upgrading to 6.0.1. First off, you need to go to 6.0 THEN 6.0.1. Next you need to choose if its a unified image or separate image. Next you need to validate what version of ROM you are running. You may have to upgrade the ROM before the upgrade. Go check out that post and let me know if everything there makes sense.
HI
im having issues with a ASA 5508 when i try to upload an update from asdm.
how you chose your file from your laptop. hopefully this makes sense as i have 5.4.1 and want to update to 6.0 but im not even getting this far to get the image/file onto firepower.
I get a BAD Gateway
“The proxy server received an invalid respose from an upstream server”
my laptop and asa is connected to a switch on same vlan and management port is connected to the switch and no internet is setup.
i can ping f/w and firepower no issue it just not uploading the update from my laptop.
if anyone can assist please
Hi Nick. Well first off keep in mind that using the built in Firepower on ASDM or using the centralized manager both only provide MINOR update downloads from the GUI. This means you have to download the major release updates from cisco.com.
Next there are two types of updates with regards to 6.0.1. I assume you are going with the separate image verses the unified? See my blog post on the difference. Also note 6.1 is about to come out as well, which will have more feature parity between the unified and separate image.
Is this a lab setup? Do you have TAC support? I posted some new installation videos so worst case if it is a lab, you could use ASDM file management to upload the temp boot file and install 6.0.1 verses upgrading to 6.0 then 6.0.1. The process I showed in this post should work if you have the right file and the ASA can access your system hosting the file. Maybe your laptop has a firewall or other security enabled preventing the transfer? Hope this helps
On my ASA with FirePOWER 5.4.1(211) system I was also getting the ‘BAD GATEWAY’ message when trying to upload version 5.4.1.7 via ASDM. I ended up enabling internet access for the FirePOWER module and downloading 5.4.1.7 via its ‘Updates’ menu. I was concerned that I’d encounter the same error when trying to upload v.6.0.0, so while that was processing I did a bit more research and found a possibly relevant note in some older Cisco documentation:
—-From FireSIGHT System Release Notes, Version 5.3.1.4—-
Note: Version 5.3.1.1 currently does not support including local directory paths when uploading files to your server on Microsoft Internet Explorer 11. Cisco recommends disabling the Internet Explorer Include local directory path when uploading files to server option via Tools > Internet Options > Security > Custom level.
——————————————————————————
On the computer running ASDM, I modified the ‘Internet Options’ per the above note. I was able to manually upload both the 6.0.0 Pre-Install and the 6.0.0 successfully.
Just purchased an ASA 5506-X and successfully upgraded from 5.4.1 to 6.2.0.1, using ASDM. But be forewarned…
You cannot upgrade using the path mentioned in the above article, as Cisco will no longer let you. You NOW have to follow the path as outlined by Cisco for the 5506-X (read the release notes for 6.2.0.1) which is as follows: Version 5.4.1 > Version 5.4.1.1 or later > Version 6.0.0 Pre-Installation Package > Version 6.0.0 > Version 6.0.1.x > Version 6.1.0 Pre-Installation Package > Version 6.1.0 > Version 6.2.0 > Version 6.2.0.x. Yes, you read that correctly!
If you try to skip any of these you will get an error telling you the upgrade is meant for version X.X.X or later where the Xs represent the previous version from the one you just tried to installed.
This really irritates me. Cisco needs to get to get their heads out of their a** and get this right. There is no reason that when I buy a new 5506 (May 2017) with a manufacture date less than two months back (Mar 23, 2017), that it should ship with software that is over two years and 20 upgrade versions out of date.
What makes it worse is that they have the audacity to charge you for the pleasure of downloading the updates and wasting 2 days of your life (that is how long it took to complete all of the upgrades) to upgrade the device to the point of where it should have been in the first place when it shipped.
Hi Steve,
That doesn’t sound cool at all. Feel free to email me at [email protected] with the details and if you need anything else to help. I know one major push is to unify all upgrades to one single upgrade as well as move away from CLI to GUI upgrades to simplify things.
What version of software showed up with your new purchase? 5.4.1? Are you trying to run the newer Threat Defense image that consolidates everything or the separate ASA and Firepower image? If its the separate image, I can see it coming with a older code. Most likely this will be the last time you see something like that as the developers are focused on all future upgrades to be one upgrade regardless of how older the current image is. Sorry for the poor upgrade experience.
Joe,
First let me state that I have been using 5505s for years and just got my first 5506 to replace a failing 5505. Your site and blogs have help me a great deal with the transition, which in the long run has saved me time.
Yes, the device shipped with the “ASA with FirePOWER Services” configuration with firepower v5.4.1. To be fair, had I known that it was going to take so long, and if I was more familiar with the device, I would have pursued reimaging the 5506 with the consolidated Threat Defense image, as that most likely would have been the faster route.
Would there be any advantage for me to reimage with the Thread Defense image at this point in time as opposed to staying with the now upgraded 5506 with separate ASA and Firepower module?
The upside was that I had a lot of time between initiating upgrades to read some of your other blogs.
I just updated via the ISO in the system restore menu.
I read from some Cisco engineers that this is the cleanest way to do the update.
Hey Guys,
I’m hoping this post is still monitored.
Our customers have 2* 5516X configured for failover.
The firepower module is currently unused and on version 5.4.1.X.
My first question as its not in use it would be easier to do a fresh install on the module. with it been a fresh install can I apply the latest version 6.2.X straight from the off?
My second question as its a HA pair do I need to uninstall 5.4.1.X on both and install 6.2.X on both? how will I integrate the ASA failover with the Firepower module?
Many thanks,
Hi Scott. Check out this https://www.cisco.com/c/en/us/td/docs/security/firepower/620/relnotes/Firepower_System_Release_Notes_Version_620/update_vs_reimage_vs_deploy.html#id_45253 …. this basically explains you should probably reimage. The upgrade path is like Version 5.4.1.1 > Version 6.0.0 Pre-Installation Package > Version 6.0.0 > Version 6.0.1 Preinstall > Version 6.0.1 > Version 6.1.0 Pre-Installation Package > Version 6.1.0 > Version 6.2.0 > Version 6.2.2 since you are so behind.
Also see https://www.cisco.com/c/en/us/td/docs/security/firepower/622/relnotes/Firepower_Release_Notes_622/Firepower_Release_Notes_622_chapter_0101.html … in particular … HA is covered here https://www.cisco.com/c/en/us/td/docs/security/firepower/622/relnotes/Firepower_Release_Notes_622/Firepower_Release_Notes_622_chapter_0101.html#task_ry4_tlj_yz