Cisco recently released Identity Services Engine (ISE) 1.4 (official release notes can be found HERE). For those unfamiliar with ISE, it is Cisco’s flagship network access control solution. This provides features such as device profiling, advanced guest access, BYOD, posture enforcement, and so much more for all LAN, VPN and Wireless devices. This post will provide a overview of the new features and how I upgraded my ISE 1.3 lab to the latest version.
What Is New With 1.4
GUEST
- Guest Periodic AUP Acceptance – You can create an authorization rule that requires a Guest user to accept an AUP to keep the session open after a certain number of hours.
- Guest Maximum Sessions – Limit the number of concurrent sessions that one Guest user can have, which is configured on the Guest Type.
- SAML – A SAML server can be used to authenticate Guest users.
CERTIFICATE MANAGEMENT
The release of Cisco ISE offers the following Certificate-related enhancements:
- You can now create a generic Certificate Signing Request and can specify the usage at a later time. You can specify the usage at the time of binding or later by editing the certificate.
- When you edit a wildcard certificate from the Admin portal, the changes are replicated to all the nodes in the deployment.
- You can now delete system certificates that you no longer need from the Admin portal.
- You can now reassign the default portal certificate group tag to a CA-signed certificate. Also, from the System Certificates page, you can view the list of portals that use this tag.
PROFILER
Profiler feed button – A test button was added to the profiler feed page that tests the connection to the Cisco feed server.
PORTALS
Cisco ISE supports SAML Single Sign On (SSO) for the following portals:
- Guest portal (sponsored and self-registered)
- Sponsor portal
- My Devices portal
You can add an Identity Provider, such as Oracle Access Manager or Oracle Identity Federation, as an external identity source for a portal. The Identity Provider stores and validates the user credentials and generates a SAML response that allows the user to access the portal. It reduces password fatigue by removing the need for entering different user name and password combinations.
Cisco ISE supports automatic failover for the administration persona. To enable the auto-failover feature, at least two nodes in your distributed setup should assume the administration persona and one node should assume the non-administration persona. If the primary administration node (PAN) goes down, an automatic promotion of the secondary administration node is initiated. For this, A
ADMINISTRATION
Cisco ISE supports automatic failover for the Administration persona. To enable the auto-failover feature, at least two nodes in your distributed setup should assume the Administration persona and one node should assume the non-Administration persona. If the Primary Administration Node (PAN) goes down, an automatic promotion of the Secondary Administration Node is initiated. For this, a non-administration secondary node is designated as the health check node for each of the administration nodes. The health check node checks the health of PAN at configured intervals. If the health check response received for the PAN health is not good due to being down or not reachable, health check node initiates the promotion of the Secondary Administration Node to take over the primary role after waiting for the configured threshold value. There are some features that are unavailable after auto-failover of the Secondary Administrative Node. Cisco ISE does not support fallback to the original PAN.
MDM
- Cisco ISE 1.4 allows you to run multiple active MDM servers on your network, including ones from different vendors. You can route different endpoints to different MDM servers based on device factors such as location or device type. You can set up an MDM portal for each MDM server on your network.
- Cisco ISE 1.4 also supports MDM for devices accessing the network over VPN via AnyConnect and Cisco ASA 9.3.2 or later.
- Cisco ISE 1.4 now supports MDM servers from Meraki.
FIPS
FIPS Mode Support – This release of Cisco ISE is FIPS compliant. Product Cisco Identity Services Engine uses embedded FIPS 140-2 validated cryptographic modules Cisco Common Cryptographic Module (Certificate #1643 and #2100). For details of the FIPS compliance claims, see the FIPS Compliance Letter.
PATCHES
Cisco ISE supports posture patch management and patch remediation features that allow you to proactively manage software patches. You can add the support of patch management compliance check and remediation by using the Opswat OESIS library to detect and remediate patch management applications for Windows OS and Mac OSX. You can select the installation, Enabled, and Up to Date attributes for different products that a vendor supports. The posture patch management remediation feature allows you to enable the patch management software, install missing patches, or activate the patch management software GUI on an endpoint.
ENDPOINTS AND ANYCONNECT
SOURCEfire’s Advanced Malware Protection (AMP) for endpoint software protects endpoints before, during, and after attacks. It provides a level of visibility and control you need to stop advanced threats missed by other security layers. The software should be downloaded from the SOURCEfire portal to add the AMP enabler profile to the client provisioning resources in Cisco ISE. You must download two images, namely, the redistributable version of the AMP for endpoint software for Windows OS and AMP for endpoint software for Mac OSX. The downloaded software is hosted on a server that is accessible from the enterprise network. The AnyConnect AMP Enabler module uses the URL to download the file to the endpoints.
How To Upgrade to ISE 1.4
For my lab (standalone node solution), I upgraded from ISE 1.3 to ISE 1.4. The steps I used are as follow. Note that this is a lab so I skilled some of the back up steps. Make sure to check out the official upgrade guide before proceeding with upgrading a production environment.
1) Download the new file ise-upgradebundle-1.4.0.253.x86_64.gz from Cisco.com (you will need authorization to do this). I used the 1.3 to 1.4 upgrade bundle. If you are running a older version, you may need to do additional steps. See the official upgrade guide for the upgrade matrix.
2) Next you need to post it to a FTP or other source so ISE can download it to the manager. I used dropbox for this purpose. Note you must post it in a public dropbox folder for this to work.
3) Next configure a repository by typing config followed by repository (name) such as repository upgrade. You will see a warning message.
4) Now you need to download the ISE software to the manager using the prepare command. For me I used the command copy https://MYDROPBOXLINK- ise-upgradebundle-1.4.0.253.x86_64.tar.gz. It will take some time for this depending on your network speed. For me it was about 20 minutes. When it is finished, you will see the command prompt again.
5) Next you need to launch the prepare command. That command is application upgrade prepare ise-upgradebundle-1.4.0.253.x86_64.tar.gz upgrade. You will see a few prompts before it asks you to continue. Say yes. This will extract the file.
6) The final step is to proceed with the upgrade. That command is application upgrade proceed. The upgrade process will run for about 30-40 minutes depending on your system. You will see a bunch of step commands showing you the status.
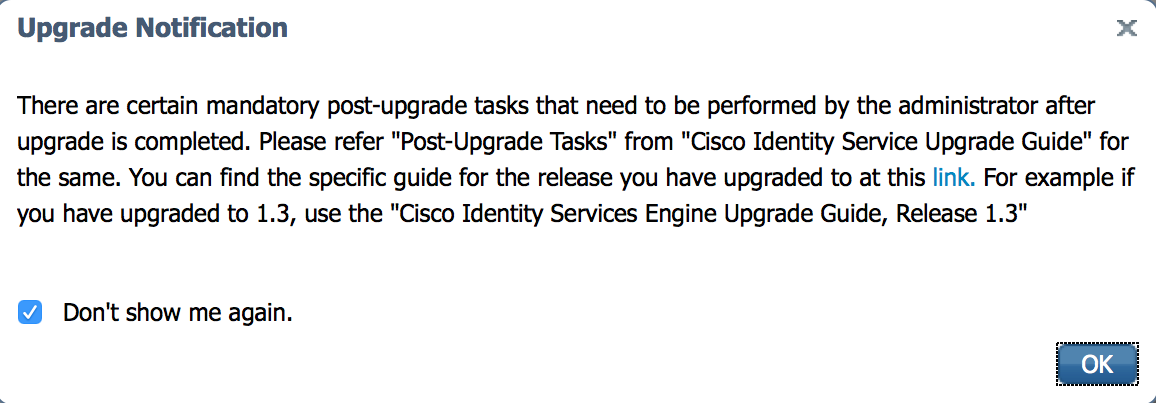
7) Once its complete, I logged into my ISE GUI and saw this warning message. I tested and system seems to be working fine on the new code.
Hopefully these steps are helpful for your upgrade to ISE 1.4. Please see the complete configuration guide found HERE for details.





Some nice features there. What I really still can’t do is have single-sign-on for Guests that don’t use an open WLAN.
I want to use PEAP-MSCHAPv2 to secure the initial guest login (works nicely on iOS) but then use CWA redirect to take the user to the Sponsored Guest portal. It works fine at the moment but there’s no way to only redirect them to the AUP page rather than having to re-enter their credentials 🙁